Qualys Security Blog Expert network security guidance and news
- Qualys VMDR and TotalCloud™ Now Available on Oracle Cloud Marketplaceby Kunal Modasiya on April 15, 2026 at 6:02 pm
Key Takeaways As organizations accelerate cloud adoption, security teams are under increasing pressure to gain unified visibility, prioritize risk effectively, and respond faster without adding complexity. We are excited to announce that Qualys VMDR (Vulnerability Management, Detection and Response) and Qualys TotalCloud™ CNAPP are now both available on the Oracle Cloud Marketplace. These Qualys listings enable joint customers to
- Microsoft and Adobe Patch Tuesday, April 2026 Security Update Reviewby Diksha Ojha on April 14, 2026 at 8:16 pm
April 2026’s Patch Tuesday arrives with Microsoft addressing a fresh set of vulnerabilities across its ecosystem, reinforcing the ongoing need for timely patching in an increasingly threat-heavy landscape. Here’s a quick breakdown of what you need to know. Microsoft Patch Tuesday for April 2026 This month’s release addresses 163 vulnerabilities, including eight critical-severity vulnerabilities. In this month’s updates, Microsoft has addressed one publicly disclosed zero-day vulnerability and one being exploited in the wild. Microsoft addressed 80 vulnerabilities in Microsoft Edge (Chromium-based) that were patched earlier this
- Anatomy of an Autonomous AI Agent Risk: How Qualys ETM Connects the Dots on OpenClawby Viren Chaudhari on April 13, 2026 at 3:44 pm
Executive Summary An unauthorized OpenClaw AI agent was detected disguised as a routine package on a Windows Server host. The situation escalated into a priority incident when Qualys ETM analyzed and correlated four distinct signals. While none of these signals alone warranted urgent action, the combination of endpoint, exposure, and identity telemetry indicated an active
- Deep Scan: Expanding Vulnerability Detection Beyond Traditional Boundariesby Spencer Brown on April 13, 2026 at 3:00 pm
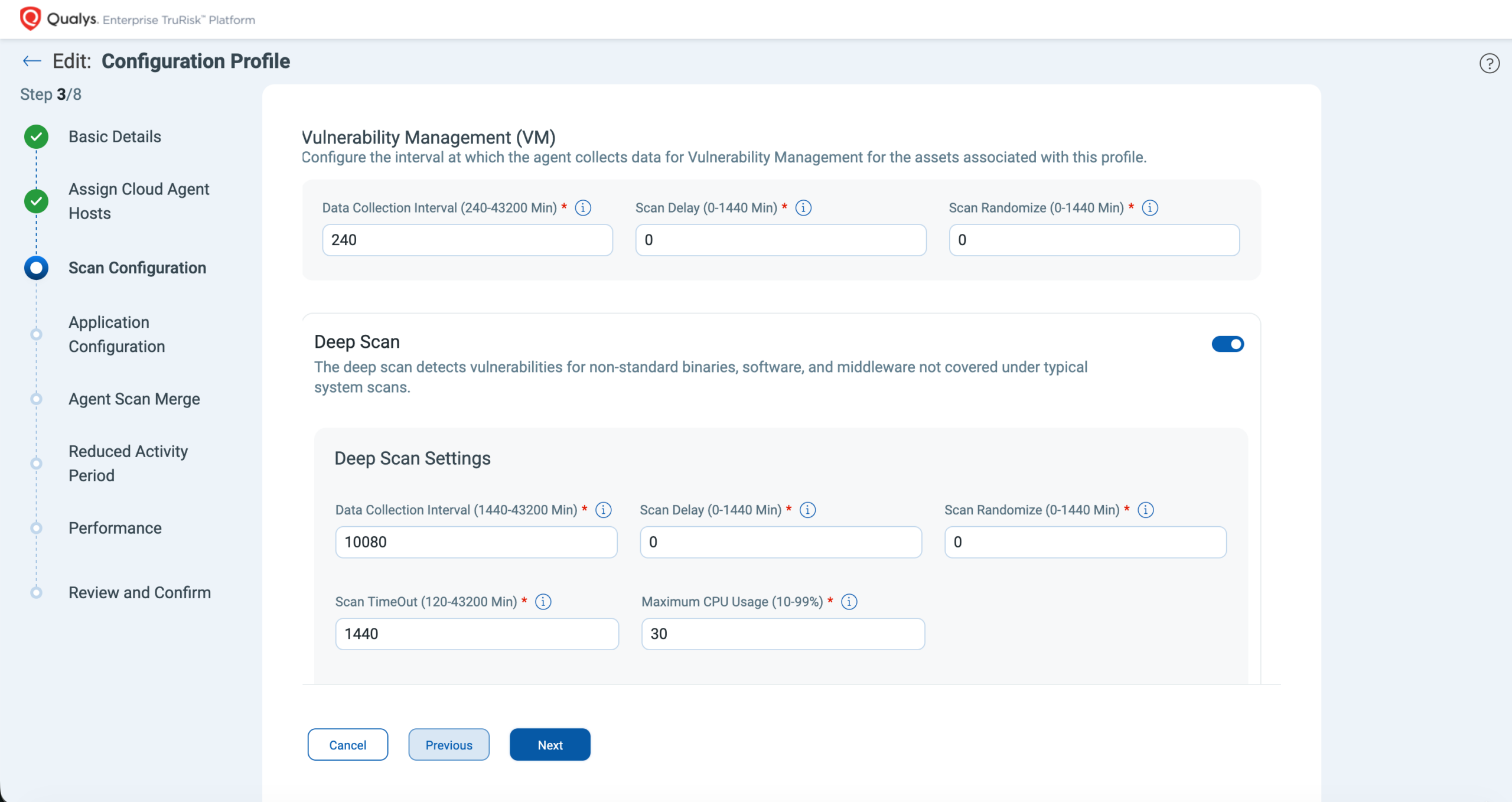
Security teams estimate that a significant percentage of enterprise software is installed outside standard system directories or package-managed locations, creating persistent visibility gaps for traditional vulnerability-scanning methods. As environments become more decentralized, with applications spread across different drives, custom installation locations, and unmanaged folders, organizations require more advanced inspection capabilities to maintain clear and accurate
- The Mythos Inflection Point: Dealing With the Upcoming Vulnerability Disclosure Avalanche and Compressed Exploitation Windowby Shailesh Athalye on April 10, 2026 at 5:26 pm
Having spent years at Qualys working on vulnerability risk and remediation management, I have watched the disclosure and remediation cycles from every angle. I have seen vulnerability researchers find a critical flaw in OpenSSH and the industry scramble to respond. I have seen organizations patching Log4Shell when it is not even applicable in production environments.
- Scaling Modern AppSec: Moving from Static Profiles to AI-Powered Scan Optimizationby Shravan Dandage on April 9, 2026 at 4:10 pm
Key Highlights Security teams today are accountable for an ever-expanding estate of web applications and APIs. In large enterprises, that often means hundreds or thousands of assets distributed across regions, cloud environments, and business units. And yet most organizations cannot confirm, within a given compliance window, that every asset in their environment has been scanned,
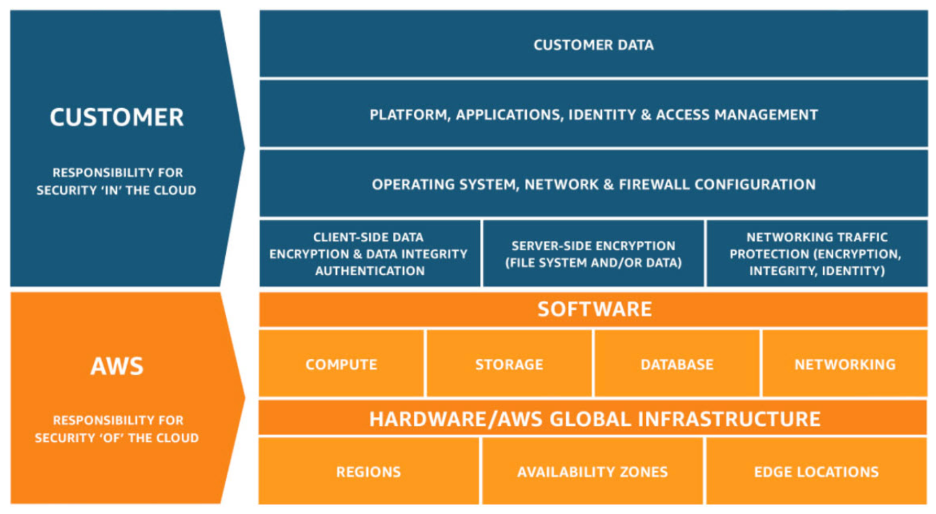
- 12 Best Practices for Securing AWS Cloud in 2026by Qualys on April 9, 2026 at 3:00 pm
Key Takeaways What Securing the AWS Cloud Really Means in 2026 Amazon Web Services (AWS) cloud security is the discipline of protecting cloud infrastructure, data, applications, and workloads on AWS through a combination of architectural choices, native controls, and continuous independent assurance. In 2026, this definition has materially evolved. Cloud environments are no longer static
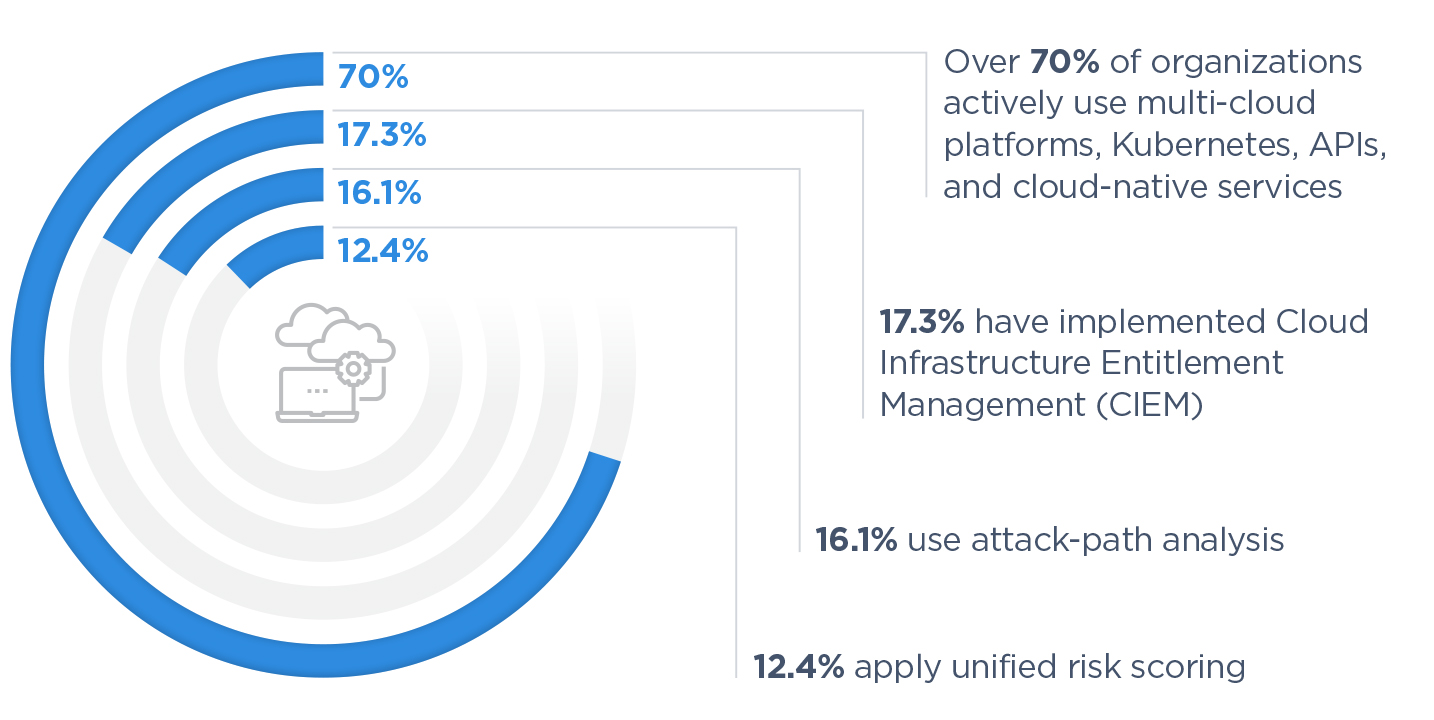
- Signals from the Cloud Security Forecast 2026: Cloud Risk Is Scaling through Design, Not Disruptionby Shilpa Gite on April 7, 2026 at 3:00 pm
Key Takeaways Cloud Risk Is No Longer Unpredictable. It Is Settling Into a Pattern. Across most enterprise environments, the same conditions produce the same outcomes. Identities carry more access than required. Trust relationships extend beyond clear boundaries. Exposure lingers longer than intended. Nothing appears broken in isolation, yet together these elements create a system where
- Why Every Enterprise Needs a Risk Operations Center (ROC)by Jonathan Trull on April 6, 2026 at 8:00 pm
Enterprise security has long optimized for speed of response over prevention of risk. At Qualys, we recognized early that this left half the problem unsolved, and we have spent years building the operational frameworks to close that gap. The Risk Operations Center is the result. Here is a scenario every security leader will recognize. A
- Optimizing Risk Discovery and Remediation with Qualys Gateway Service (QGS)by Spencer Brown on March 30, 2026 at 3:00 pm
Unpatched vulnerabilities remain one of the largest drivers of cyber risk, accounting for nearly 60% of cyber compromises. Modern security programs are therefore measured not only by how quickly they discover risk, but also by how efficiently they remediate it. As organizations scale vulnerability management and patching operations, network efficiency, bandwidth utilization, and connectivity constraints can become