- Trump postpones executive order focused on AI security by djohnson on May 21, 2026 at 6:37 pm
Under a draft executive order, the NSA, Treasury Department and other federal agencies would get 90-days to test new models for cybersecurity and national security concerns. The post Trump postpones executive order focused on AI security appeared first on CyberScoop.
- CISA chief frets about open-source vulnerabilities, delayed security improvementsby Tim Starks on May 21, 2026 at 5:05 pm
Acting director Nick Andersen’s comments came as a wave of malware attacks hit tech that’s publicly available for collaboration. The post CISA chief frets about open-source vulnerabilities, delayed security improvements appeared first on CyberScoop.
- CISA credential leak raises alarms, and Capitol Hill demands answersby Tim Starks on May 19, 2026 at 11:28 pm
A researcher who found a repository that leaked on GitHub said it was one of the worst he’s witnessed. The post CISA credential leak raises alarms, and Capitol Hill demands answers appeared first on CyberScoop.
- AI might cut false positives, but it won’t stop the slop by djohnson on May 18, 2026 at 8:45 pm
Anthropic and OpenAI promise their latest tools will find more vulnerabilities. Cybersecurity employees say they’re already flooded with AI-generated reports. The post AI might cut false positives, but it won’t stop the slop appeared first on CyberScoop.
- Major world economies spell out key elements of AI ‘ingredients list’by Tim Starks on May 12, 2026 at 9:09 pm
Experts on the topic say the G7 guidance is good, but could still use some improvements. The post Major world economies spell out key elements of AI ‘ingredients list’ appeared first on CyberScoop.
- Google and Amnesty International teamed up to make it harder for spyware vendors to hideby Tim Starks on May 12, 2026 at 5:00 pm
Intrusion Logging marks the first feature from a major device vendor to aid with forensic detection of sophisticated threats, Amnesty International said. The post Google and Amnesty International teamed up to make it harder for spyware vendors to hide appeared first on CyberScoop.
- Instructure claims hackers returned stolen Canvas data after an extortion standoffby Matt Kapko on May 11, 2026 at 11:31 pm
ShinyHunters, a prolific cybercrime group, threatened to leak data from more than 8,800 school systems. The post Instructure claims hackers returned stolen Canvas data after an extortion standoff appeared first on CyberScoop.
- Google spotted an AI-developed zero-day before attackers could use itby Matt Kapko on May 11, 2026 at 1:00 pm
Researchers found artifacts in the code that proved AI was heavily involved. A prominent cybercrime group planned to exploit the zero-day en masse for financial gain. The post Google spotted an AI-developed zero-day before attackers could use it appeared first on CyberScoop.
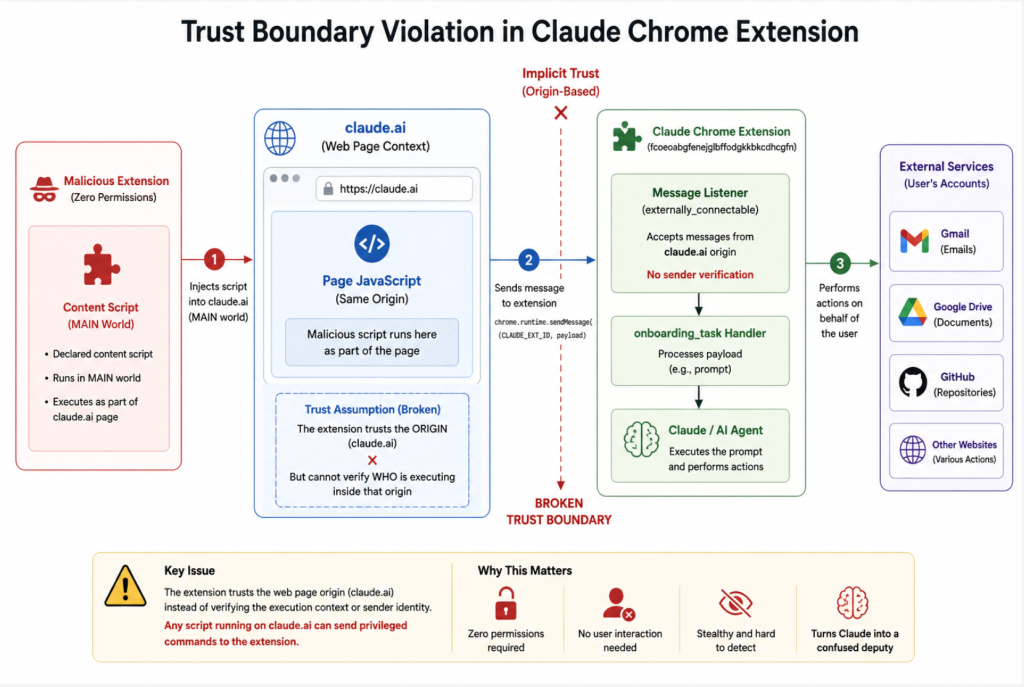
- Flaw in Claude’s Chrome extension allowed ‘any’ other plugin to hijack victims’ AIby djohnson on May 8, 2026 at 1:06 pm
Agentic AI is more popular than ever, but researchers keep finding trivial ways to hijack LLMs for nefarious purposes. The post Flaw in Claude’s Chrome extension allowed ‘any’ other plugin to hijack victims’ AI appeared first on CyberScoop.
- A college student is suing a dating app that allegedly used her TikTok videos to target men in her dormitoryby djohnson on May 4, 2026 at 4:02 pm
The woman’s lawyer told CyberScoop they believe the company edited her video to suggest she was a “friend with benefits” and intentionally geofenced it to men around her. The post A college student is suing a dating app that allegedly used her TikTok videos to target men in her dormitory appeared first on CyberScoop.

Technology Cyberscoop
We are an ethical website cyber security team and we perform security assessments to protect our clients.