- New FTC Data Spotlight highlights text scams that may target your businessby chundycz on April 16, 2025 at 5:31 pm
New FTC Data Spotlight highlights text scams that may target your business chundycz April 16, 2025 | 1:31PM New FTC Data Spotlight highlights text scams that may target your business According to the FTC’s latest Data Spotlight, text scam losses are skyrocketing. In 2024 people reported $470 million in losses to text scams, more than five times the amount reported in 2020. Check out the Data Spotlight for more information.Want to help your employees spot and avoid the most common text scams highlighted by the Data Spotlight? Check out the FTC’s Consumer Alert with details and advice.Here are a few examples of text scams that may be particularly likely to target your business:Fake fraud alerts. If you get an urgent text about “suspicious activity” or a large purchase you don’t recognize on your business credit card or bank account, it could be a scam. The text might look like it’s from your financial institution and include a phone number to call. But people who respond report getting connected to scammers who pressure them to move money out of their accounts, supposedly to keep it safe. Those “safe spaces” end up being under the scammer’s control, and people who move their money don’t get it back.Bogus unpaid toll notices. If you manage your business’s fleet, you may be on high alert for tolls, parking tickets, or other related expenses. Don’t be tricked by an unexpected text saying there’s a toll balance to pay, even if the text looks like it’s from your local highway toll program. In reality, there’s a good chance it’s scam, there’s no toll owed, and if you click the link in the text, you may be asked to hand over financial information.Phony job opportunities. Impersonators may use your business’s good name to offer people fake job opportunities through unsolicited texts offering pay for repetitive tasks like rating products or apps. Impersonators hurt consumers and honest competitors, and the Rule on Impersonation of Government and Businesses gives the FTC enhanced tools to stop them. If you learn someone is posing as your business to scam people, the FTC wants to hear about it. Tell us what happened at ReportFraud.ftc.gov.To protect yourself, your employees, and your business from text scams:Don’t click on links or respond to unexpected texts. If you don’t recognize the texter or expect the communication, stop and do your due diligence. Run a search for the business that claims to be contacting you, and call or email the business directly using contact information you know is correct or find on its verified website. Don’t click the link or call the number in the text.Pause for a moment. One of the top tricks in the scammer playbook is to apply pressure to act quickly. If someone you don’t know texts to say there’s an urgent problem or demands you pay immediately, take a minute to do some research and check in with someone you trust.
- New resources to help protect consumers and small businesses from fraudby lfair on November 8, 2023 at 5:02 pm
New resources to help protect consumers and small businesses from fraud lfair November 8, 2023 | 12:02PM New resources to help protect consumers and small businesses from fraud By Lesley Fair Consumers speak many languages and unfortunately scammers are conversant in all of them. That’s why the FTC has reinforced its fraud fighting capabilities by collecting scam reports in multiple languages. As a member of the business community, you can lend a hand by sharing these new resources with employees, friends, and others in your network.To report in Mandarin, Tagalog, Vietnamese, French, Arabic, Korean, Russian, Portuguese, Polish, and many other languages, consumers can call the FTC at (877) 382-4357, and press 3 to speak to an interpreter. To report identity theft, they can call (877) 438-4338 and choose the option for their preferred language. Lines are open between 9AM-5PM Eastern Time.For consumers who prefer to report in English, a visit to ReportFraud.ftc.gov or IdentityTheft.gov will get them immediate guidance on the next steps to take. Spanish-speaking consumers can go to ReportFraude.ftc.gov or RobodeIdentidad.gov. Image The FTC also just announced additional online resources for consumers in multiple languages with to-the-point guidance on how to avoid scams. Prefer it in print? Visit ftc.gov/bulkorder to order free copies.In addition, we have a new resource for entrepreneurs. The revised publication Scams and Your Small Business is now available in English, Spanish, Simplified Chinese, Korean, and Vietnamese. Share this useful guide with members of your local business community. Every page features actionable advice on how to spot, stop, and report questionable practices that target small business owners.
- FTC consumer protection year in review offers 2020 vision for your businessby lfair on January 8, 2020 at 2:26 pm
FTC consumer protection year in review offers 2020 vision for your business lfair January 8, 2020 | 9:26AM FTC consumer protection year in review offers 2020 vision for your business By Lesley Fair They say hindsight is 20/20, but what about foresight? We’re not ones to prognosticate, but a look at notable FTC cases and initiatives from the past year suggests some topics likely to be top of mind in months to come. Here is a non-exhaustive list of issues in our 2019 rearview mirror and likely visible through the 2020 windshield. Consumer privacy. The FTC’s $5 billion enforcement action against Facebook made history and headlines, but the other notable part of the case is the monumental change the order mandates to Facebook’s privacy ecosystem. The Commission opinion in Cambridge Analytica reaffirms the proposition that like any other claim, a company’s privacy promises are viewed through the lens of established FTC consumer perception principles. A series of cases demonstrates the agency’s continued commitment to challenging false or misleading representations about businesses’ compliance with the EU-U.S. Privacy Shield Framework. Another important development is the FTC’s proposed settlement with Retina-X. It’s our first action against a marketer of stalking apps – software that allowed purchasers to monitor the mobile devices on which they’re installed, without users’ knowledge. COPPA. Congress passed the Children’s Online Privacy Protection Act to ensure that when it comes to the collection of kids’ personal information online, parents are in the driver’s seat. The FTC settlement with YouTube – brought in conjunction with the New York Attorney General – alleges that the company collected kids’ personal data without parental consent, in violation of the COPPA Rule. The $170 million civil penalty broke the record for the largest remedy in an FTC COPPA case, set months before in our $5.7 million settlement with Musical.ly, now known as TikTok. If you’re a YouTube channel owner, read a special Business Blog post for tips on determining if your content is directed to children. Data security. Is your company honoring its data security promises and taking reasonable steps to safeguard the sensitive information in its possession? The FTC, CFPB, and State AG actions against Equifax illustrate how consumers are injured when companies ignore reasonably foreseeable threats. The settlement, which totals between $575 million and $700 million – also reminds businesses that heeding warnings about known risks is more prudent (and cost-effective) than the alternative. Three threads tie together the FTC’s unrelated actions against LightYear Dealer Technologies and InfoTrax Systems. They both sell management software to specific industries. They both allegedly failed to take reasonable steps to secure their networks, resulting in damaging data breaches. And they’re both covered by similar new orders the FTC has introduced in recent data security cases. If you or your clients are players in the Internet of Things, the settlement of the FTC’s litigation against connected device company D-Link sends an unmistakable message: The future of the IoT marketplace depends on secure software development. Endorsements, certifications, and influencers. Why is the FTC concerned about the accuracy of endorsements and certifications? Because they’re material to consumers. The FTC says Truly Organics’ claim that its personal care products were “certified organic” lathered up a double bubble of deception. First, its merchandise contained ingredients that weren’t organic. Second, the company falsely claimed that its products were certified by USDA’s National Organic Program. Other FTC developments focused on the use of endorsements in social media. The FTC’s action against Devumi alleges the company sold fake followers, phony subscribers, and bogus likes to companies and individuals that wanted to boost their social media presence. FTC-FDA warning letters to sellers of nicotine-laced liquid used for vaping had a lot to say about the legal obligation of influencers and advertisers in any industry to clearly disclose material connections. Looking for to-the-point tips on how to do that? Disclosures 101 for Social Media Influencers breaks it down to the basics. Consumer reviews. A look back at cases involving consumer reviews illustrates some questionable practices for businesses to avoid. The FTC settled charges against snack box company UrthBox for misrepresenting that customer reviews were independent when the company had given people free products and other incentives to post positive reviews. The FTC’s proposed settlement with Sunday Riley Modern Skincare demonstrates that undisclosed “selfie” reviews violate the FTC Act, too. According to the FTC, company managers and employees posted reviews of their own products on the website of a major cosmetics retailer, using fake accounts to hide their identities. The FTC charged that Cure Encapsulations paid a third-party website to post fake reviews on its behalf on Amazon. (The FTC says the company’s weight loss promises were deceptive, too.) In a related development, 2019 saw an uptick in enforcement of the Consumer Review Fairness Act, which bans form contract provisions that restrict a consumer’s ability to post reviews about a seller’s goods, services, or conduct. We first announced settlements with an HVAC contractor, a flooring company, and a horseback riding business, and followed up with actions against a vacation rental operator and a property management company. The cases challenged illegal “confidentiality” or “non-disparagement” clauses that sometimes threatened consumers with financial penalties for posting reviews. Health claims. Health-related misrepresentations remain a core enforcement priority. The FTC settled its lawsuit against Gerber Products Company, which had allegedly made deceptive claims about its Good Start Gentle baby formula. On the other end of the age spectrum, companies continue to target older Americans with purported remedies for joint pain, diabetes, digestive disorders, etc. Two actions – a $537,500 order against NatureCity and an $821,000 order against A.S. Research – stand for the proposition that there’s nothing #OKBoomer about promoting unproven treatments to boomer consumers. Pitching their products as “Viagra for the Brain,” Global Community Innovations promised improved memory, boosted cognition, and increased IQ. But the FTC says their claims were bogus and their supposed endorsements from people like Bill Gates and the late Dr. Stephen Hawking were blatant bunk. Warning letters to sellers of CBD products underscored the established principle that if advertisers make claims – express or implied – about the purported health effects of what they sell, they need sound science to support their statements. FinTech. The pace of innovation can be dizzying, but long-standing consumer protection principles are the fixed stars in the FinTech firmament. That’s the message businesses should take from the FTC’s $3.85 million settlement with online lender Avant. The complaint alleged that Avant engaged in unfair and deceptive practices in how it marketed and serviced loans. Established standards also apply on crowdfunding platforms. According to the FTC’s pending action against iBackPack of Texas, the company raised over $800,000 in crowdfunding campaigns, but blew a big chunk of the money on personal expenses. In an action settled in 2019, the FTC says the marketers of programs called Bitcoin Funding Team and My7Network baited the trap with promises of crypto riches, but went old-school by marketing them through chain referrals, a form of pyramid scheme. Bookmark the FTC’s new FinTech page for the latest cases and resources. Financial injury. Challenging illegal practices that hit people in the wallet is the FTC’s bread and butter, and 2019 will be known for cases that returned a substantial amount of bread to American consumers. The $191 million settlement with University of Phoenix focused on allegedly deceptive employment claims. Multi-level marketer AdvoCare paid $150 million to settle FTC charges it operated an illegal pyramid scheme. (Actions against two other AdvoCare promoters are pending.) AT&T will return $60 million to customers to resolve an FTC complaint that it made deceptive “unlimited data” promises. Career Education Corporation, operator of Colorado Technical University and American Intercontinental University, paid $30 million to settle charges it used deceptive lead generation tactics to market its schools. A settlement with Office Depot and Support.com included a financial remedy of $35 million for inducing consumers to buy pricey repair services based on false claims that in-store scans detected signs of malware on their computers. A stipulated order with the recidivist ringleader of a student loan debt relief scheme held him liable for $11 million in compensatory relief. A ruling against mortgage modification scammers imposed an $18.5 million judgment and banned them for life from the debt relief business. And an important bankruptcy ruling in an action involving a defendant in the BlueHippo case preserved a $14 million judgment from discharge. Telemarketing. The war against robocalls continued in 2019 with Operation Call It Quits, a coordinated crackdown against con artists responsible for more than a billion illegal calls. In addition to actions announced by the FTC, 25 federal, state, and local law enforcement partners filed another 87 lawsuits, including five criminal cases. The FTC opened a new front in the 360° fight against unwanted calls by filing its first Telemarketing Sales Rule action against a VoIP service provider. According to the pending lawsuit, Globex Telecom played a key role in subjecting consumers to a barrage of illegal calls for a credit card interest rate reduction scheme. The FTC also announced settlements in litigation against a perpetrator who used robocalls to solicit donations to bogus veterans charities, big wigs behind a robocall dialing platform, and a group that set up shop just weeks after a federal court – at the request of the FTC and Florida AG – shut down another telemarketing ring where some of them worked. Another action resulted in a $3.3 million summary judgment against recidivists who blasted small businesses with a barrage of robocalls that falsely threatened their companies would be removed from Google search results. The FTC isn’t alone in the battle against deception. In addition to law enforcers across the country, key partners in the effort are the millions of consumers who file reports to the Consumer Sentinel database. The FTC uses that empirical data to assist in law enforcement and to shed light on emerging scams. Using information from those reports, FTC issued Data Spotlights in 2019 revealing the staggering financial losses caused by romance scams, the rise of government imposter scams, and the different forms of fraud most frequently reported by millennials and consumers 60 and over. This year the FTC also introduced a new way to visualize and customize data: the agency’s interactive Tableau Public page. The Bureau of Consumer Protection’s busy event calendar in 2019 could be indicative of issues of continuing interest in 2020. In addition to multiple Common Ground conferences that brought together consumer protection agencies and community groups, FTC staff hosted workshops on made in USA claims, the future of the COPPA Rule, class action notices, loot boxes in gaming, online ticket sales, repair restrictions on consumer products, small business financing, accuracy in consumer reporting, and PrivacyCon 2019. The variety of topics suggests two things to us: 1) the breadth of the FTC’s consumer protection mission, and 2) our ongoing interest in exploring emerging issues with advocates and experts who bring a wide variety of perspectives to the table.
- Showcase your research at PrivacyCon 2020by lfair on October 11, 2019 at 5:36 pm
Showcase your research at PrivacyCon 2020 lfair October 11, 2019 | 1:36PM Showcase your research at PrivacyCon 2020 By Lesley Fair How would we describe PrivacyCon 2020? Is it Burning Man without the flames? The New Orleans Jazz Festival – minus the jazz and the festival? The best way to know what PrivacyCon is all about is to mark your calendar for July 21, 2020, and attend the FTC’s fifth annual gathering of leading privacy researchers. And check out our Call for Presentations to see if PrivacyCon would be a good forum for your recent research. Like its four predecessors, PrivacyCon 2020 will consider the broad range of privacy and data security issues. But this time we’re also taking a deeper dive into the privacy of health information that is collected, stored, and transmitted by apps. We’re looking for experts who can summarize their current research in a 10-minute presentation, followed by a panel discussion applying those findings to questions of consumer protection law and policy. The Call for Presentations outlines the eligibility requirements and details the type of topics we hope to cover at PrivacyCon 2020. For consideration as a PrivacyCon presenter, apply by April 10, 2020. PrivacyCon 2020 will take place at the FTC’s Constitution Center conference facility, 400 7th Street, S.W., in Washington, DC. It’s free and open to the public and we’ll webcast the event live. In the meantime, make plans to join leading privacy researchers in Washington on July 21st and consider submitting your research for discussion at PrivacyCon 2020.
- i-Dressup and a data security mess-upby lfair on April 24, 2019 at 7:08 pm
i-Dressup and a data security mess-up lfair April 24, 2019 | 3:08PM i-Dressup and a data security mess-up By Lesley Fair Kids love to play dress-up, but parents wouldn’t want them rummaging through the attic or climbing to the top shelf of the wardrobe without permission and proper supervision. The i-Dressup.com website offered users – including children – a virtual way to play dress-up and design clothes without those potential dangers. But according to an FTC complaint, Unixiz, Inc., the company behind i-Dressup, violated the Children’s Online Privacy Protection Act in ways that created different kinds of risks. COPPA puts two separate sets of protections in place to help keep parents in control of personal information collected from their kids online. First, COPPA-covered companies must clearly disclose their information policies and get parental consent before collecting personal information from children under 13. Second, companies must provide reasonable and appropriate security for the data they collect. According to an FTC settlement, i-Dressup fell short on both COPPA requirements. The complaint alleges i-Dressup failed to provide sufficient notice on its site of the information it collected online from kids, how it used it, its disclosure practices, and other specifics required by the COPPA Rule. The company’s direct notices to parents were deficient, too. Among other things, they didn’t include the COPPA-required statement that if parents don’t provide consent within a reasonable time, i-Dressup will delete their online contact information from its records. Stick with the story because that failure turned out to be particularly troubling. In addition to letting users play online games, i-Dressup featured a community where they could “explore their creativity and fashion sense with unique personal profiles” and interact with others. To register, i-Dressup required people to submit a user name, password, birthdate, and email address. If the birthdate indicated the person was under 13, the email field changed to “Parent’s Email.” Once the under-13 user filled in the required fields and clicked “Join Now,” i-Dressup collected the personal information and sent a message to the address entered into the Parent’s Email field. The person receiving the email could consent by clicking the “Activate Now!” button. However, if the parent didn’t give consent, i-Dressup retained the personal information it had collected from the child online. The FTC says the company’s failure to delete that information violated Section 312.5(c)(1) of the COPPA Rule. In addition to violating COPPA’s parental consent provisions, i-Dressup allegedly violated the Rule’s data security requirements. According to the FTC, i-Dressup stored and transmitted users’ personal information (including passwords) in plain text. In addition, the company failed to perform network vulnerability testing of its network, even for well-known threats like SQL attacks; it didn’t implement an intrusion detection and prevention system; and it didn’t monitor for potential security incidents. The upshot? The company learned that a hacker had gained entry to its network and accessed information about 2.1 million users, including approximately 245,000 users who indicated they were under 13. To settle the case, i-Dressup and its owners will pay a $35,000 civil penalty. They’re also prohibited from violating COPPA in the future, and can’t sell, share, or collect any personal information until they implement a comprehensive data security program and get independent biennial assessments. In addition, they’ll have to provide the FTC with an annual certification of compliance. The message for sites and operators covered by COPPA is that an effective system of parental consent is only the first step toward compliance. Section 312.8 of the COPPA Rule also requires you to “establish and maintain reasonable procedures to protect the confidentiality, security, and integrity of personal information collected from children.” Interested in data security issues? Read an accompanying Commission statement and learn more about another FTC action announced today.
- Top frauds of 2018by lfair on February 28, 2019 at 5:21 pm
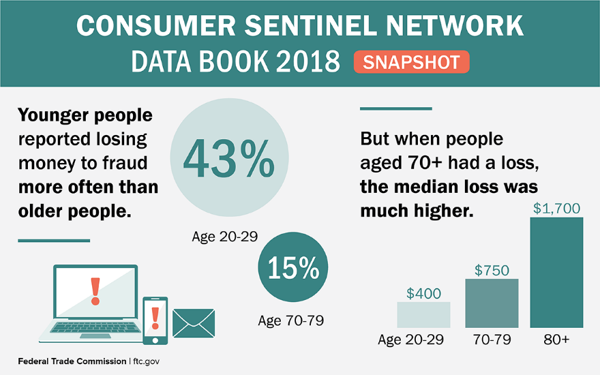
Top frauds of 2018 lfair February 28, 2019 | 12:21PM Top frauds of 2018 By Paul Witt, Supervising Data Analyst, FTC Bureau of Consumer Protection Every year, millions of consumers tell us – and our partners – about the frauds they spotted. In 2018, we heard from 3 million people and learned a lot from the reports entered into our Consumer Sentinel database. Here are some notable facts from the Consumer Sentinel Network’s 2018 Data Book – including that a new category of scams has earned the unenviable right to chant “We’re #1.” We collected more than 1.4 million fraud reports, and people said they lost money to the fraud in 25% of those reports. People reported losing $1.48 billion (with a “b” ) to fraud last year – an increase of 38% over 2017. The top reports in 2018 were: imposter scams, debt collection, and identity theft. Younger people reported losing money to fraud more often than older people. Let that sink in. It’s what the data have been telling us for a while, but it’s hard for people to grasp. Last year, of those people who reported fraud and their age, 43% of people in their 20s reported a loss to that fraud, while only 15% of people in their 70s did. When people in their 70s did lose money, the amount tended to be higher: their median loss was $751, compared to $400 for people in their 20s. Scammers like to get money by wire transfer – for a total of $423 million last year. That was the most of any payment method reported, but we also saw a surge of payments with gift and reload cards – a 95% increase in dollars paid to scammers last year. Tax-related identity theft was down last year (by 38%), but credit card fraud on new accounts was up 24%. In fact, misusing someone’s information to open a new credit card account was reported more often than other forms of identity theft in 2018. The top 3 states for fraud and other reports (per 100K population) are Florida, Georgia and Nevada. The top 3 states for identity theft reports (also per 100K) are Georgia, Nevada and California. The Consumer Sentinel Network’s online database is available to more than 2,500 users in civil and criminal law enforcement agencies across the country and around the world. Agencies use the reports to research cases, identify victims, and track possible targets. Although non-governmental organizations may contribute data, only law enforcers can access the database. Check out what happened in your state. In fact, you can slice and dice the numbers yourself. And comment below if you find something interesting. Meanwhile, consumers should keep reporting to the FTC at ftc.gov/complaint. We use those reports to investigate and bring cases – and so do our thousands of law enforcement partners.
- New date for FTC workshop on ticket salesby lfair on February 12, 2019 at 3:52 pm
New date for FTC workshop on ticket sales lfair February 12, 2019 | 10:52AM New date for FTC workshop on ticket sales By Lesley Fair You won’t need a ticket, but you will need to mark your calendar for June 11, 2019. That’s the new date for That’s the Ticket, an FTC workshop about online ticket sales. The workshop – originally scheduled for March – will explore the ticket sales marketplace, consider industry-wide advertising and pricing issues, and discuss ways to address deception beyond traditional law enforcement. Topics include ticket bots, the Better Online Ticket Sales Act (BOTS Act), the resale ticket market, disclosures of pricing and fees, and possible consumer confusion about search engine ads and websites of resellers. (The GAO has issued a report summarizing these issues.) Commissioner Slaughter will offer opening remarks. We’ll announce the rest of the agenda as the event draws nearer. The June 11th workshop – it’s free and open to the public – will be held at the FTC’s Constitution Center, 400 7th Street, S.W., in Washington, DC. Can’t make it to DC? We’ll webcast the event live.
- FTC sues American Immigration Center for claiming false government affiliationby lfair on October 16, 2018 at 4:16 pm
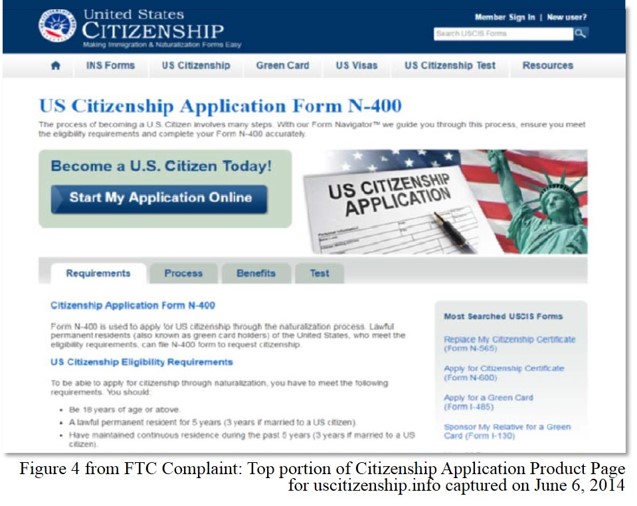
FTC sues American Immigration Center for claiming false government affiliation lfair October 16, 2018 | 12:16PM FTC sues American Immigration Center for claiming false government affiliation By Lesley Fair When the FTC warns consumers about government imposter scams, we’re usually referring to bogus calls that falsely claim to come from the IRS or some other official office. But as a case just announced by the FTC demonstrates, that’s not the only kind of false government affiliation that can deceive consumers. A $2.2 million settlement with American Immigration Center reminds other businesses of the dangers of conveying a misleading connection to a government agency. When consumers wanted to renew their green cards or apply for naturalization, where did they go? Online, of course, where they input terms like “USCIS,” “INS,” or “US Immigration” to search for the proper government site. According to the FTC, that’s how they ran across results with tag lines like “USCIS Forms – Easy Online Forms for Green Card & Citizenship.” A click took them to sites with the outward appearance of official government webpages. First, there were the URLs – usimmigration.us, uscitizenship.info, etc. Then there was the red, white, and blue color scheme, the Statue of Liberty, passports, and pictures of then-President Obama. What’s more, people looking for, say, Green Card Renewal Form I-90, saw links with the exact name of the relevant document. According to the FTC, people paid between $120 to $300 and input a substantial amount of personal information, all under the impression they were filing documents directly with a government agency. Except that they weren’t. Despite the appearance of those pages, consumers were actually on one of many commercial sites the defendants used to sell their “software wizard” to fill out government immigration forms. And the money consumers paid didn’t go toward government filing fees. It went straight into the defendants’ pockets. In addition to the $2.2 million judgment, the defendants have agreed to clearly disclose that: 1) their sites aren’t affiliated with the government; 2) people must separately file immigration applications with the appropriate government agency; and 3) people must separately pay applicable filing fees to the government. The proposed order also bars the defendants – principal Cesare Alessandrini and Forms Direct, Inc., doing business as American Immigration Center – from stating or implying any affiliation with the government. What’s the message for other companies? Avoid an affiliation conflation. Look at your ads and websites from the point of view of your target audience. Could prospective customers be left with the misimpression that your company has an affiliation with a government agency? Steer clear of any purported connection to a local, state, or federal government office. Consider the big picture. The complaint in this case cited the words the defendants used to convey claims to consumers, as well as what their websites looked like. That’s because, according to the FTC Deception Policy Statement, “The Commission will evaluate the entire advertisement, transaction, or course of dealing in determining how reasonable consumers are likely to respond.” That specifically includes visual imagery and the omission of material information. Wise companies bear in mind the FTC’s long-established “net impression” standard and exercise caution in drafting their copy, selecting graphics, and choosing what they say – and what they don’t say – to consumers.
- Under COPPA, data deletion isn’t just a good idea. It’s the law.by lfair on May 31, 2018 at 6:04 pm
Under COPPA, data deletion isn’t just a good idea. It’s the law. lfair May 31, 2018 | 2:04PM Under COPPA, data deletion isn’t just a good idea. It’s the law. By Jared Ho Buckling up in the car is a precaution parents take to protect themselves and their children. When it comes to the Children’s Online Privacy Protection Act, navigating the rules of the COPPA Road helps protect your business and the kids who visit your website or use your online service. Most companies are familiar with COPPA’s mandate to get parental consent up front before collecting personal information from children under 13. But there’s another requirement farther down the COPPA Road that some businesses may not know about. As the FTC’s Six-Step Compliance Plan for Your Business explains, if you’re covered by the Children’s Online Privacy Protection Rule, you must provide parents the right to review and delete their children’s information. But did you know that, under certain circumstances, COPPA also requires you to delete children’s personal information, even if parents don’t ask you to? Consider the example of a subscription-based app that offers children under 13 a variety of games and learning tools. What happens if, at the end of the subscription period, a parent decides not to renew the service? Absent a deletion request from Mom or Dad, can the company just keep the child’s personal information? The answer is clear: No, the company can’t keep it. Under Section 312.10 of COPPA, you’re allowed to retain children’s personal information “for only as long as is reasonably necessary to fulfill the purpose for which the information was collected.” After that, you must delete it using reasonable measures to ensure it’s been securely destroyed. With that in mind, if you haven’t reviewed your data retention policy recently, it’s time to take a fresh look at it. What do you do with the child’s information when a parent closes an account, doesn’t renew a subscription, or allows an account to become inactive? Is that information still necessary for, say, final billing purposes? If so, for how long? Here are a few questions that might help your company navigate COPPA’s data retention and deletion requirements: What types of personal information are you collecting from children? What is your stated purpose for collecting the information? How long do you need to hold on to the information to fulfill the purpose for which it was initially collected? For example, do you still need information you collected a year ago? Does the purpose for using the information end with an account deletion, subscription cancellation, or account inactivity? When it’s time to delete information, are you doing it securely? The FTC has resources to help your company streamline COPPA compliance.
- FTC challenges claims that products could treat side effects of cancer treatmentby lfair on January 11, 2018 at 7:01 pm
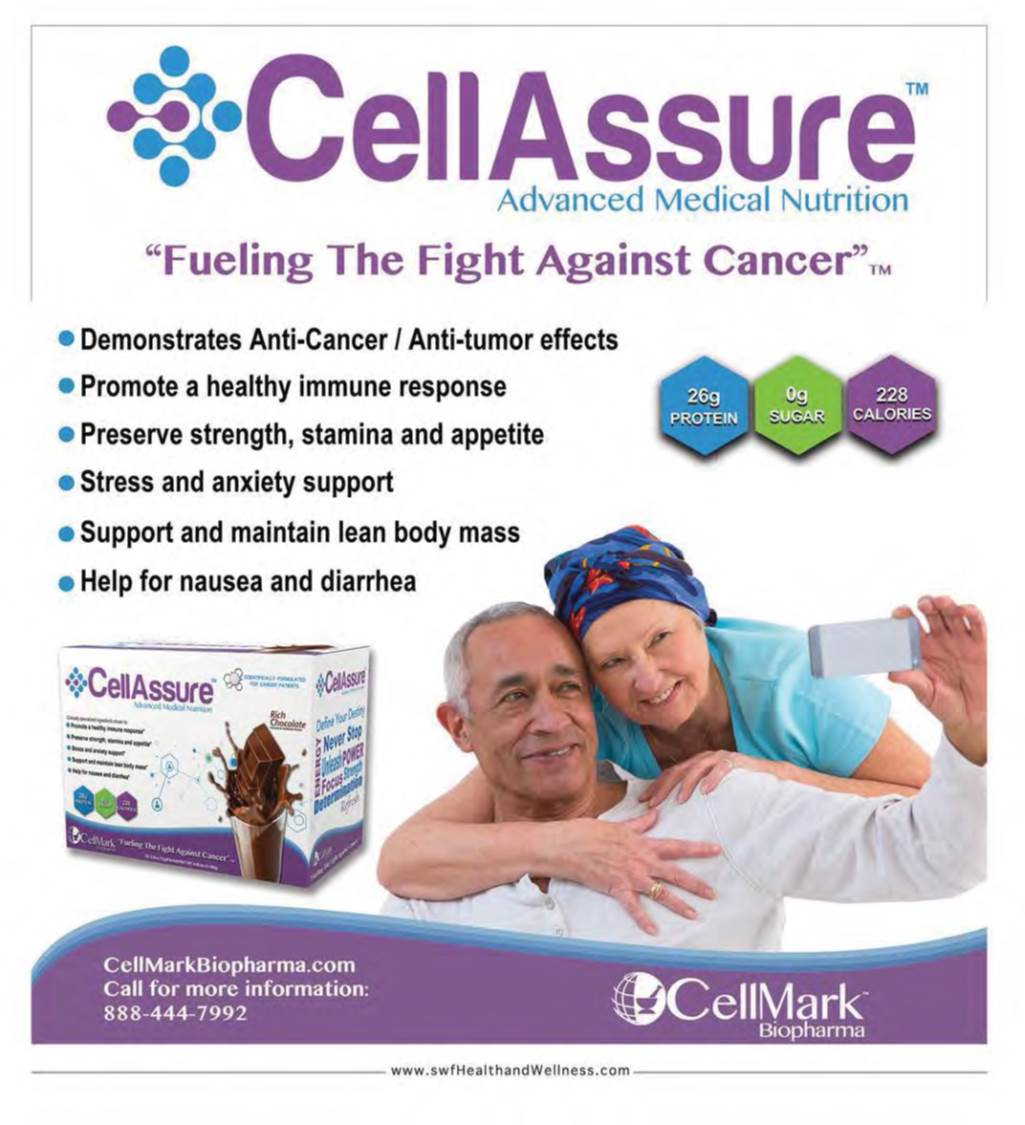
FTC challenges claims that products could treat side effects of cancer treatment lfair January 11, 2018 | 2:01PM FTC challenges claims that products could treat side effects of cancer treatment By Lesley Fair The FTC’s fight against the deceptive marketing of unproven cancer treatments goes back to the early days of the agency, and it’s disappointing that we still need to bring cases of that nature. But you can add the FTC’s settlement with Florida-based CellMark Biopharma and CEO Derek Vest to that list – and the deceptive claims they pitched to people battling cancer are particularly disconcerting. Two serious complications of cancer treatment are cachexia (the wasting syndrome some patients experience) and “chemo fog” (the chemotherapy-related cognitive dysfunction that patients often report). CellMark claimed to have the answer to both problems. Selling for $248 for a one-month supply, CellAssure was advertised to treat cachexia and cancer-related malnutrition. In addition, according to the FTC, the defendants conveyed to consumers that CellAssure would improve cancer patients’ ability to withstand the rigors of surgery, radiation, and chemotherapy. But that’s not all. The defendants also claimed that the product “exhibits anti-cancer/anti-tumor effects” and that CellAssure’s ingredients had been “clinically proven” to provide the advertised benefits. Marketed to treat the memory loss and cognitive impairment sometimes reported during and after chemotherapy, a one-month supply of Cognify cost cancer patients $79. According to ads, Cognify would “protect brain cells/neuro-transmitters against toxins,” “improve cognitive functioning, memory, and processing,” and “stimulate the growth of new brain cells” in patients undergoing chemo. The company used a similar “don’t just take our word for it” tactic by claiming that Cognify’s ingredients were “clinically proven.” But according to the FTC, the defendants didn’t have sound science to back up their promises. What’s more, the complaint charges that the company’s “clinically proven” claims were false. The settlement in the case requires the defendants to have randomized, double-blind, placebo-controlled testing conducted by qualified researchers to support future cancer- or disease-related claims for dietary supplements, foods, or drugs. Other health claims will need “competent and reliable scientific evidence,” as that phrase is defined in the order. The settlement also prohibits misrepresentations about tests, studies, or research. The terms of the settlement apply just to CellMark and CEO Derek Vest – who, by the way, is serving time in federal prison for criminal conduct related to the sale of other dietary supplements. But the case reminds marketers just how seriously the FTC takes claims directed to cancer patients and others battling serious medical conditions. There’s also a message for people dealing with a cancer diagnosis or the side effects of cancer treatment. Just because a product is available online or at a drugstore or health food shop is no guarantee that it’s effective. For some patients, certain over-the-counter formulations can interfere with proven treatments and may even be downright dangerous. Talk with your doctor before taking anything, including dietary supplements, vitamins, and other products.

FTC Business Blog
We are an ethical website cyber security team and we perform security assessments to protect our clients.