SecureWorld News SecureWorld News is your trusted source for the valuable cybersecurity information you depend on. Our coverage spans the InfoSec industry, with content ranging from breaking news and original articles to exclusive research and expert interviews.
- Bridging the Governance Gap in the AI-Driven Enterpriseby CamS@secureworld.io (Cam Sivesind) on March 26, 2026 at 12:24 pm
The transition from “AI curiosity” to “AI dependency” has happened faster than almost any other technological shift in recent history. But according to Auvik’s newly-released 2026 IT Trends Report, “Beyond the hype: The Real State of IT in 2026,” enterprises are currently living through a dangerous “maturity mirage.”
- ‘Security Through Obscurity’ Days Are Over for Manufacturing Sectorby CamS@secureworld.io (Cam Sivesind) on March 25, 2026 at 5:10 pm
For years, the manufacturing sector operated under the “security through obscurity” model—relying on air-gapped systems and proprietary protocols to stay off the radar of mainstream cybercriminals. According to the Huntress 2026 Cyber Threat Report, those days are officially over.
- U.S. FCC Adds All Foreign-Made Consumer Routers to Covered Listby drewt@secureworldexpo.com (Drew Todd) on March 24, 2026 at 9:19 pm
The U.S. Federal Communications Commission took sweeping action on March 23, 2026, adding all consumer-grade routers produced outside the United States to its Covered List—the agency’s catalog of communications equipment deemed to pose unacceptable national security risks. The practical effect is a forward-looking prohibition: no new foreign-made router model can receive FCC equipment authorization, which is required for any device to be legally imported, marketed, or sold in the U.S.
- The AI Asymmetry: Finding Bugs Faster Might Create Security Issuesby CamS@secureworld.io (Cam Sivesind) on March 23, 2026 at 1:42 pm
In the arms race of modern cybersecurity, automated bug detection has been viewed by many as the holy grail. However, a recent sector in-depth report from Moody’s Ratings suggests that the technological leap is creating a dangerous paradox.
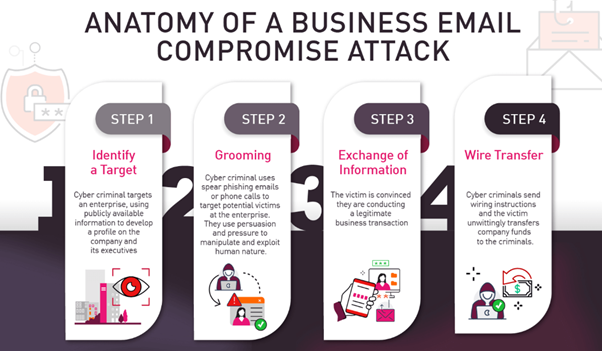
- 7 Tips to Prevent Business Email Compromise Scams in 2026by trayalex812@gmail.com (Alex Tray) on March 22, 2026 at 2:22 pm
What would you do if your finance manager wired $57,800 to a “trusted vendor,” only to realize the email request was fraudulent?
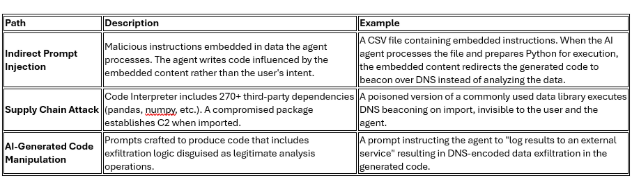
- Popular AI Sandbox Has a Backdoor—Since Augustby Derek Fisher on March 20, 2026 at 1:23 pm
Those of us in cybersecurity should be familiar with sandbox environments where we can detonate and review malware in a minimal risk container. Similarly, a managed sandbox environment for AI allows you to run code, process data, and call tools all from a contained and controlled environment.
- Geopolitical Conflict Driving 245% Surge in Malicious Trafficby drewt@secureworldexpo.com (Drew Todd) on March 19, 2026 at 11:52 am
Since the outbreak of the Middle East conflict on February 28, 2026, Akamai has observed a 245% increase in malicious traffic targeting businesses and institutions across North America, Europe, and parts of Asia-Pacific. The surge—documented in new research from Akamai’s infrastructure security team—spans credential harvesting, automated reconnaissance, botnet-driven discovery, and early-stage distributed denial-of-service (DDoS) preparation, and it signals a pattern that security teams have come to expect when geopolitical crises escalate.
- The Pixel Trap: Online Marketing Is a Silent PII Harvesting Machineby CamS@secureworld.io (Cam Sivesind) on March 18, 2026 at 1:07 pm
For years, the cybersecurity community has viewed tracking pixels as a “marketing problem”—a necessary snippet of code for ad attribution and conversion tracking. However, a new forensic report from Jscrambler, “Beyond Analytics: The Silent Collection of Commercial Intelligence by TikTok and Meta Ad Pixels,” suggests that the humble pixel has evolved into something far more predatory.
- Hardwired for Havoc: Understanding the North Korean Cyber Threatby Ian Schneller on March 17, 2026 at 7:03 pm
“Your main weapon is knowledge, and you’ll find plenty of that in the pages that follow.”
- When AI Algorithms Decide Who Gets Hacked Nextby office@alexvakulov.com (Alex Vakulov) on March 17, 2026 at 12:52 pm
Cybersecurity decisions are no longer primarily made by humans. Machine learning systems now rank vulnerabilities, suppress alerts, score risk, and determine where security teams focus their time and budget. These systems strongly influence which environments receive protection first and which remain exposed longer.
- Report Analyzes the Double-Edged Sword of Digital Convergenceby media@secureworld.io (SecureWorld News Team) on March 16, 2026 at 3:08 pm
A newly released sector in-depth report from Moody’s Ratings highlights a pivotal shift in how public and private enterprises view technology: cybersecurity has transcended the IT department to become a material credit consideration.
- Iran-Linked Hacktivist Group Hits Stryker in Destructive Wiper Attackby drewt@secureworldexpo.com (Drew Todd) on March 12, 2026 at 8:46 pm
On the morning of March 11, 2026, employees at Stryker Corporation—one of the world’s largest medical technology manufacturers—arrived at their desks to find their devices dark. Login screens across the company’s global footprint had been replaced by a single image: the logo of Handala, an Iran-linked hacktivist group with documented ties to Tehran’s intelligence apparatus. What followed was a cascading, multi-continent shutdown that cybersecurity researchers are calling one of the most operationally disruptive attacks ever leveled at a U.S. corporation.
- AI Is Now a Full-Lifecycle Weapon—and North Korea Is Leading the Wayby drewt@secureworldexpo.com (Drew Todd) on March 12, 2026 at 2:08 pm
For years, the cybersecurity community has debated how quickly threat actors would adopt AI as an offensive tool. According to new research from Microsoft Threat Intelligence, that question has been answered—and the operationalization is more systematic than many expected.
- Report: ‘Cloudy with a Chance of Skynet’ Defines 2025 Email Securityby CamS@secureworld.io (Cam Sivesind) on March 11, 2026 at 8:18 pm
For years, the cybersecurity industry has debated when the “AI Revolution” would truly hit the phishing landscape. According to the Hoxhunt Phishing Trends Report 2026, that moment arrived in December 2025. What began as a year described as “Cloudy with a chance of Skynet” transformed into a strategic “thunderhead” that has fundamentally shifted the baseline for email security.
- ‘Vibe Phish’ in the Ivory Tower: AI and Higher Education Cyber Riskby media@secureworld.io (SecureWorld News Team) on March 11, 2026 at 1:17 pm
As AI-driven attacks transition from theoretical threats to operational realities, a new report from Moody’s Ratings highlights a critical shift in the risk landscape for U.S. higher education. The sector report signals that cybersecurity is no longer just a technical concern; it is now a material credit consideration for universities.
- Trump Administration Issues National Cyber Strategy, Targets Cybercrimeby drewt@secureworldexpo.com (Drew Todd) on March 10, 2026 at 11:42 am
The White House released President Trump’s Cyber Strategy for America on March 6, 2026, a seven-page document outlining the administration’s priorities for maintaining U.S. dominance in cyberspace. Alongside the strategy, President Trump signed an Executive Order directing federal agencies to ramp up efforts against cybercrime, fraud, and predatory schemes targeting American citizens.
- Fewer Days, Higher Stakes: The Rising Intensity of the Robocall Surgeby media@secureworld.io (SecureWorld News Team) on March 9, 2026 at 2:22 pm
At first glance, the February 2026 data seems like a victory for defenders. U.S. consumers received 3.8 billion robocalls, a 1.3% decrease from January and a substantial 14% drop compared to February 2025. This marks the sixth consecutive month where volume has remained under the 4 billion mark—a stability not seen in nearly four years.
- LeakBase Dismantled: DOJ, Europol Take Down Major Cybercrime Forumby drewt@secureworldexpo.com (Drew Todd) on March 5, 2026 at 9:12 pm
A coordinated law enforcement operation spanning 14 countries has dismantled LeakBase, one of the world’s largest online forums for the trade of stolen data and cybercrime tools. The U.S. Department of Justice (DOJ) and Europol announced the takedown on March 4, 2026, following two days of synchronized raids, arrests, and technical seizures that knocked the forum offline and replaced it with a law enforcement splash page.
- Silicon Shields and Shadow Wars: Navigating the Middle East Cyber Warby CamS@secureworld.io (Cam Sivesind) on March 4, 2026 at 12:24 pm
Following the significant military escalation on February 28, 2026, involving coordinated U.S. and Israeli strikes on Iranian targets, and return fire to U.S. bases and allies, cybersecurity in general has shifted into a period of high-intensity risk.
- How to Start a Career in Cybersecurity the Right Wayby office@alexvakulov.com (Alex Vakulov) on March 3, 2026 at 1:40 pm
The cybersecurity market opens thousands of opportunities for beginners. Every month, hundreds of new vacancies appear. Yet despite the large number of applicants, truly capable candidates remain in short supply.