Compass Security Offensive Defense
Compass Security Blog Offensive Defense
- SSH Labsby Emanuel Duss on May 27, 2026 at 7:00 am
SSH is a widely used protocol that provides secure access to remote systems. It enables encrypted communication, file transfers, command execution and shell access for system administration. Visit https://sshlabs.compass-security.training to learn more about SSH security.
- Introducing RAPTRby Felix Aeppli on May 11, 2026 at 7:00 am
I’m happy to announce that we are releasing the beta version of RAPTR, a fully open source, API driven collaboration platform built specifically for red and purple team engagements.
- Tabletop Simulations: Where Theory Meets Realityby Andreas Arnold on April 28, 2026 at 7:00 am
On paper, the vast majority of crisis plans look reasonable, actionable and complete. Once the rubber hits the road, however, chaos emerges quickly.
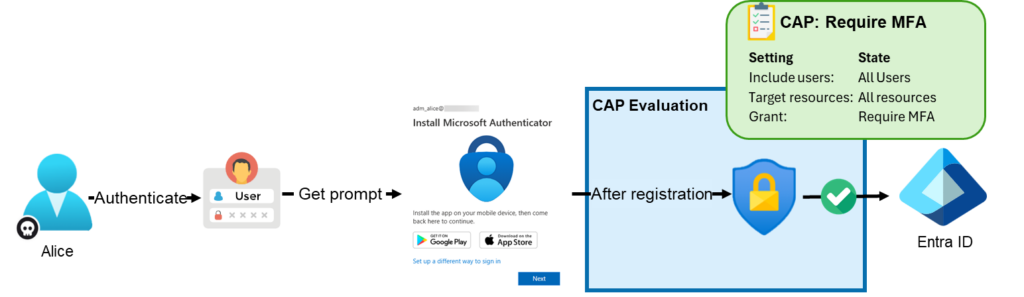
- Common Entra ID Security Assessment Findings – Part 4: Weak Conditional Access Policiesby Christian Feuchter on April 14, 2026 at 7:00 am
This post is part of a small blog series covering common Entra ID security findings observed during real-world assessments. Each article explores selected findings in more detail to provide a clearer understanding of the underlying risks and practical implications. Conditional Access Policies Conditional Access policies are among the most important security controls in Entra ID.
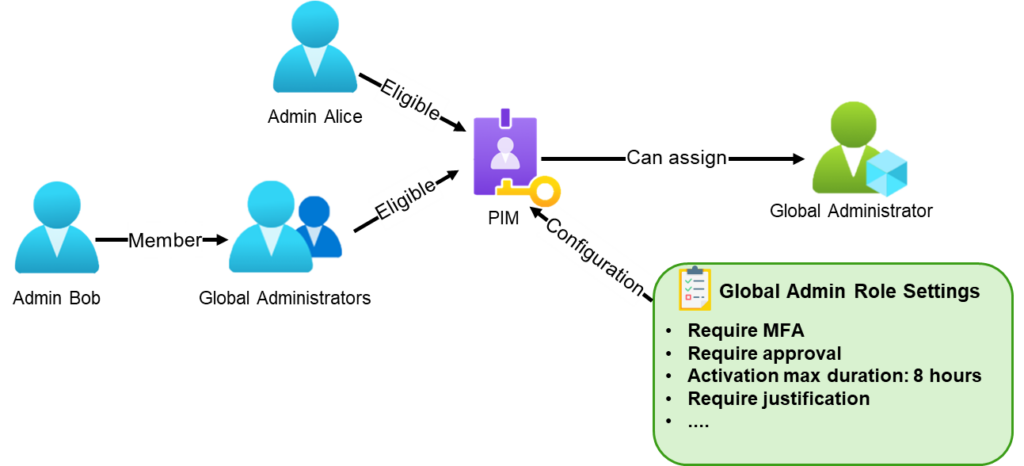
- Common Entra ID Security Assessment Findings – Part 3: Weak Privileged Identity Management Configurationby Christian Feuchter on April 7, 2026 at 7:00 am
This post is part of a small blog series covering common Entra ID security findings observed during real-world assessments. Each article explores selected findings in more detail to provide a clearer understanding of the underlying risks and practical implications. What Is Privileged Identity Management? Privileged Identity Management (PIM) is a service in Microsoft Entra ID
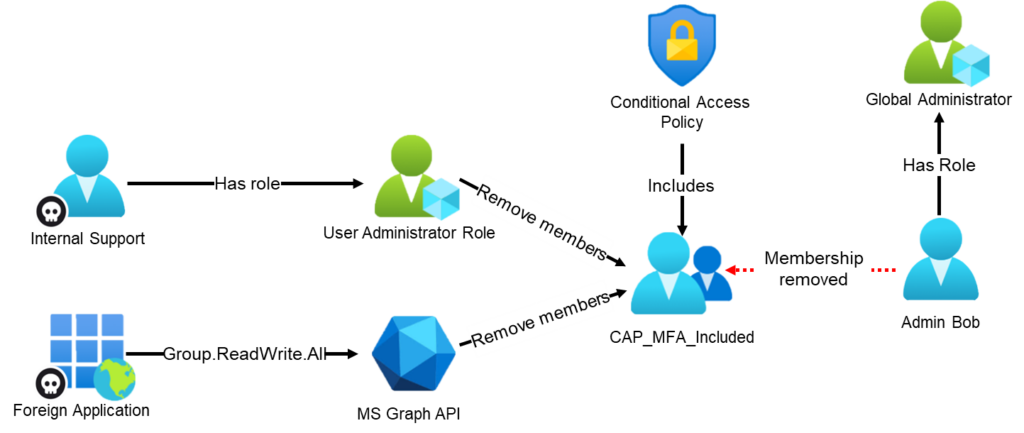
- Common Entra ID Security Assessment Findings – Part 2: Privileged Unprotected Groupsby Christian Feuchter on March 31, 2026 at 7:41 am
In part 2 of our 4-part series on common Entra ID security findings, we show how seemingly harmless group configurations can be abused to bypass security controls and gain high privileges. The post shows scenarios where insufficiently protected groups are used to: weaken Conditional Access protections for administrators enable privilege escalation through PIM for Groups grant privileged access to Azure resources, leading to full compromise We also show how to detect these issues in practice using EntraFalcon and how to mitigate them.
- Common Entra ID Security Assessment Findings – Part 1: Foreign Enterprise Applications With Privileged API Permissionsby Christian Feuchter on March 24, 2026 at 9:23 am
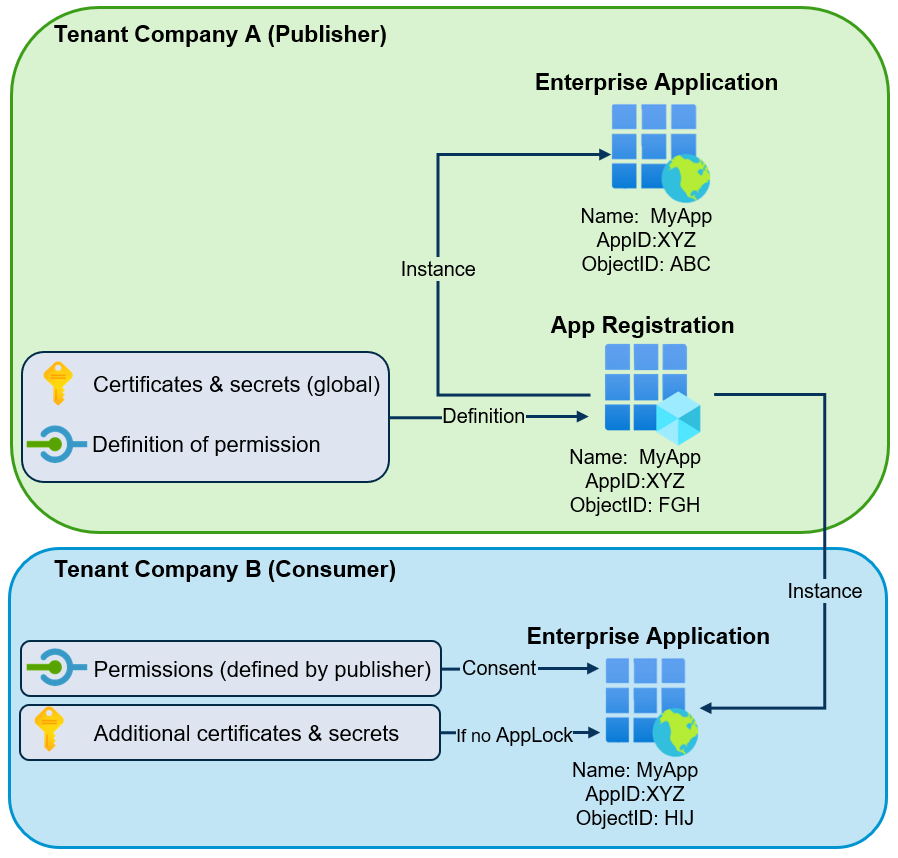
This post is part of a small blog series covering common Entra ID security findings observed during real-world assessments. Each article explores selected findings in more detail to support a clearer understanding of the underlying risks and practical implications. Introduction In the vast majority of tenants we review, there are enterprise applications that originate from
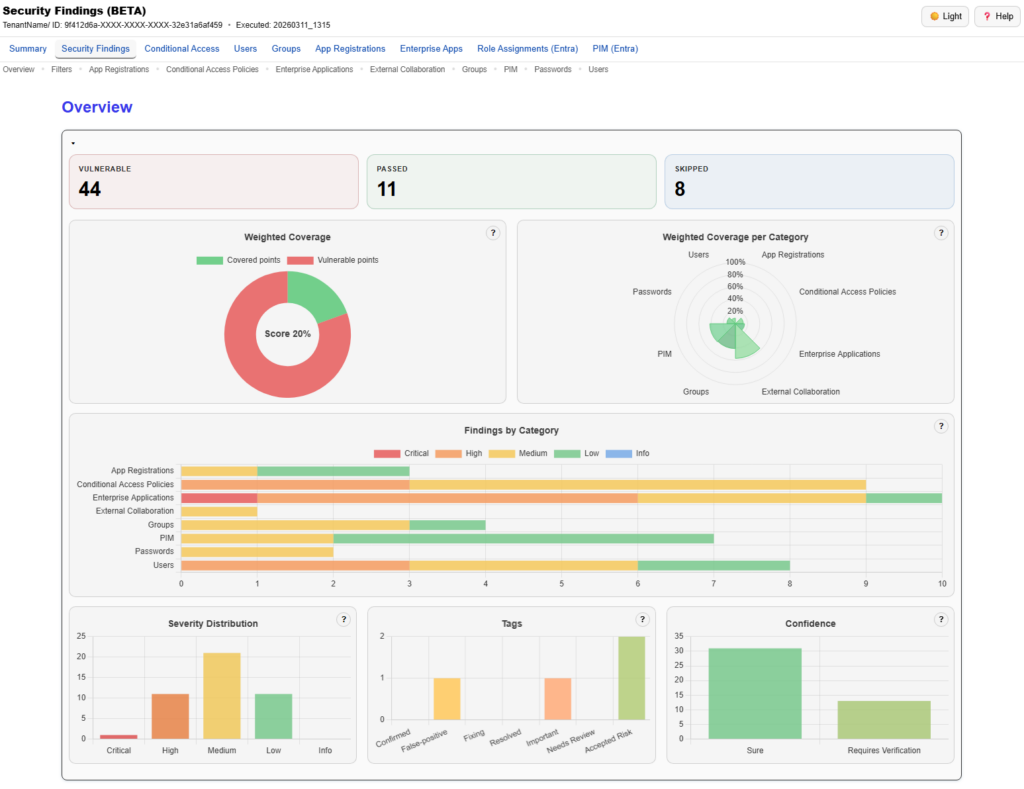
- From Enumeration to Findings: The Security Findings Report in EntraFalconby Christian Feuchter on March 17, 2026 at 8:00 am
We just released a big update for EntraFalcon. The new Security Findings Report adds an interactive HTML overview to EntraFalcon that consolidates tenant settings and object-based checks into structured security findings. Over 60 checks, graphical charts, filtering, export, and more options are now available.
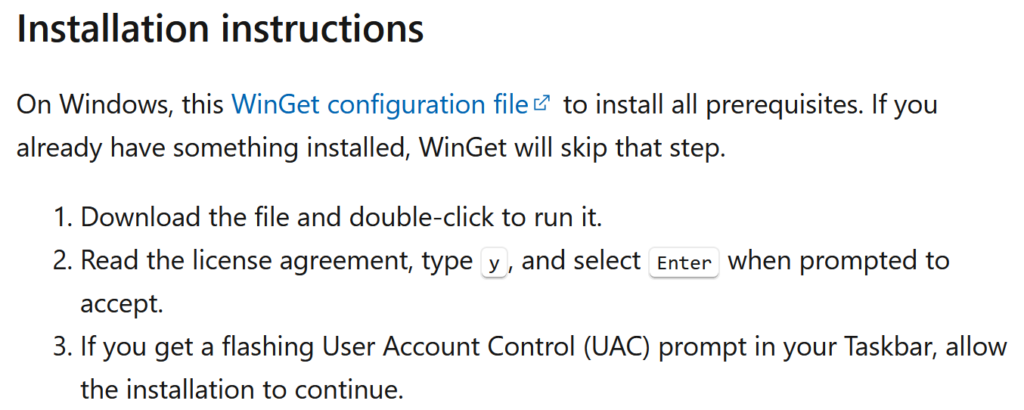
- WinGet Desired State: Initial Access Establishedby Marc Tanner on March 3, 2026 at 8:00 am
While not new, a self-referencing LNK file in combination with winget configuration instructions can be a viable initial access payload for environments where the Microsoft Store is not disabled.
- From Folder Deletion to Admin: Lenovo Vantage (CVE‑2025‑13154)by John Ostrowski on February 10, 2026 at 8:00 am
Last year we wrote about a Windows 11 vulnerability that allowed a regular user to gain administrative privileges. Not long after, Manuel Kiesel from Cyllective AG reached out to us after stumbling across a seemingly similar issue while investigating the Lenovo Vantage application. It turns out that the exploit primitive for arbitrary file deletion to gain SYSTEM privileges no longer works on current Windows machines.