AWS Security Blog The latest AWS security, identity, and compliance launches, announcements, and how-to posts.
- AWS successfully completed its first surveillance audit for ISO 42001:2023 with no findingsby Atulsing Patil on February 26, 2026 at 10:45 pm
In November 2024, Amazon Web Services (AWS) was the first major cloud service provider to announce the ISO/IEC 42001 accredited certification for AI services, covering: Amazon Bedrock, Amazon Q Business, Amazon Textract, and Amazon Transcribe. In November 2025, AWS successfully completed its first surveillance audit for ISO 42001:2023, Artificial Intelligence Management System with no findings.
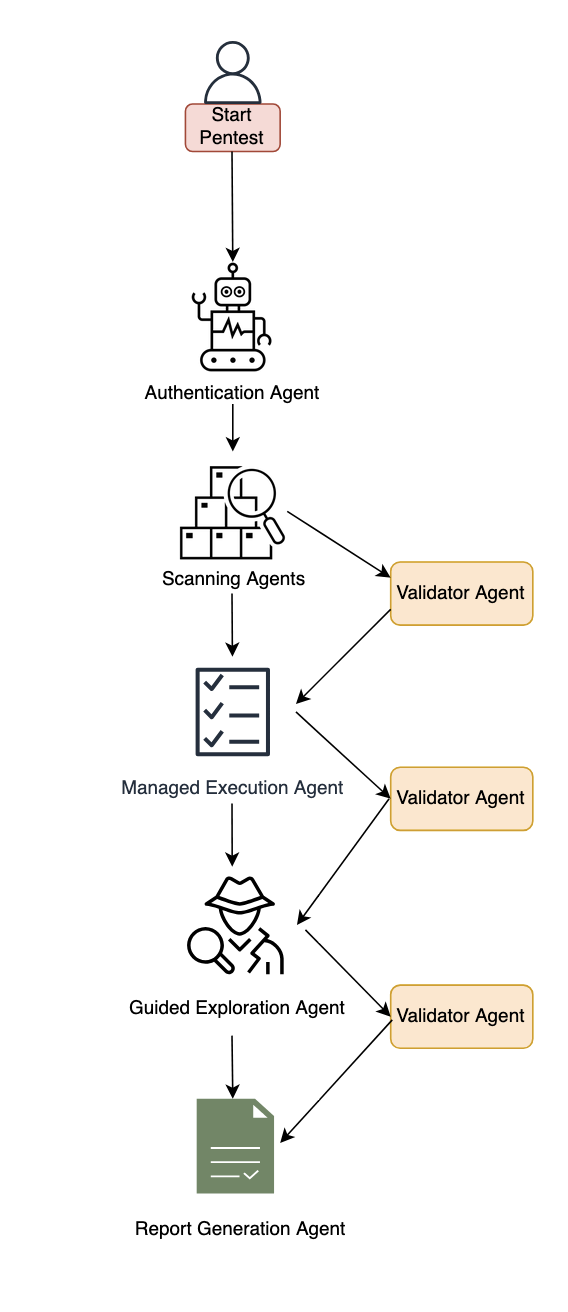
- Inside AWS Security Agent: A multi-agent architecture for automated penetration testingby Tamer Alkhouli on February 26, 2026 at 10:11 pm
AI agents have traditionally faced three core limitations: they can’t retain learned information or operate autonomously beyond short periods, and they require constant supervision. AWS addresses these limitations with frontier agents—a new category of AI that performs complex reasoning, multi-step planning, and autonomous execution for hours or days. Multi-agent collaboration has emerged as a powerful
- AI-augmented threat actor accesses FortiGate devices at scaleby CJ Moses on February 20, 2026 at 8:27 pm
Commercial AI services are enabling even unsophisticated threat actors to conduct cyberattacks at scale—a trend Amazon Threat Intelligence has been tracking closely. A recent investigation illustrates this shift: Amazon Threat Intelligence observed a Russian-speaking financially motivated threat actor leveraging multiple commercial generative AI services to compromise over 600 FortiGate devices across more than 55 countries
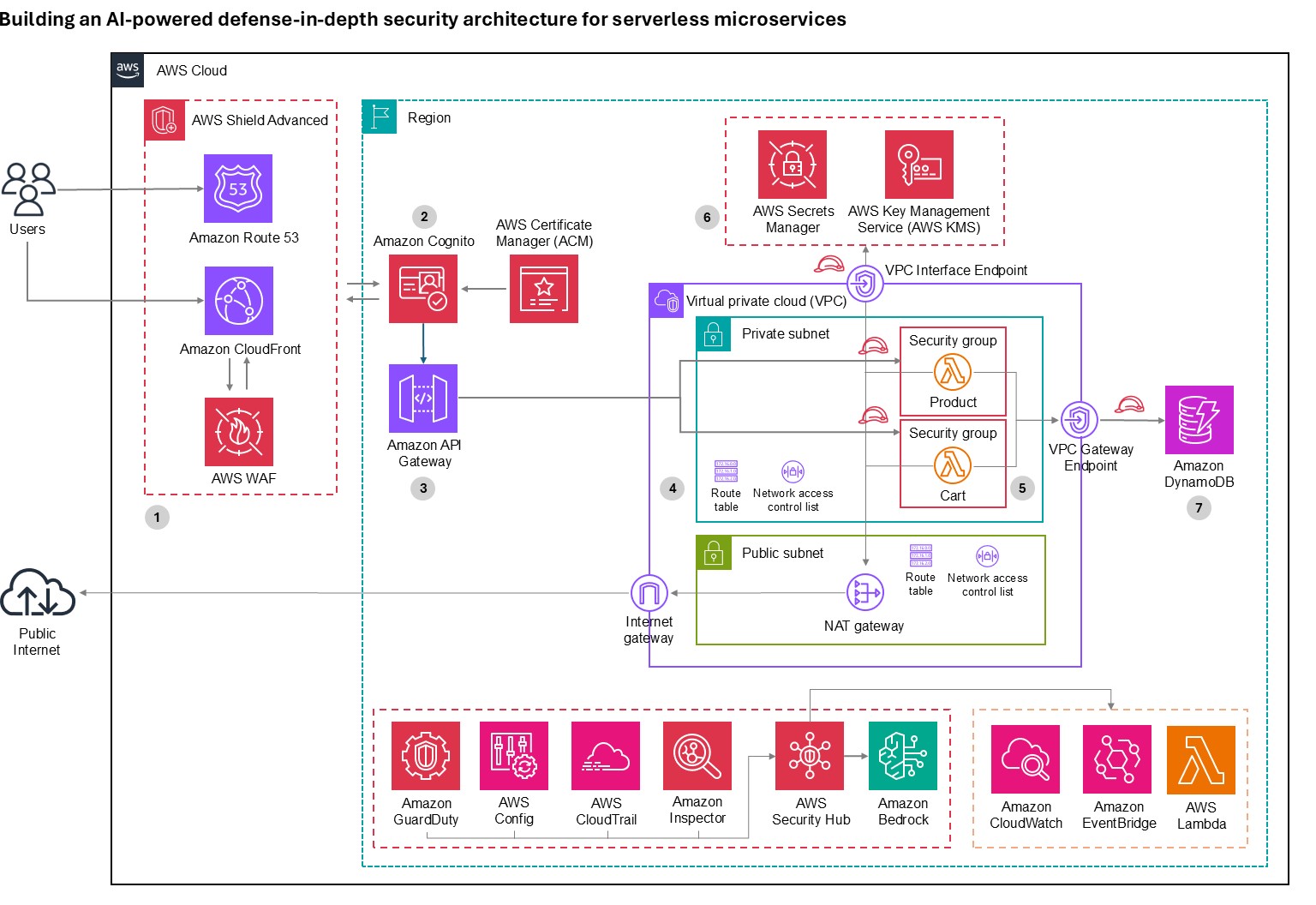
- Building an AI-powered defense-in-depth security architecture for serverless microservicesby Roger Nem on February 16, 2026 at 8:10 pm
Enterprise customers face an unprecedented security landscape where sophisticated cyber threats use artificial intelligence to identify vulnerabilities, automate attacks, and evade detection at machine speed. Traditional perimeter-based security models are insufficient when adversaries can analyze millions of attack vectors in seconds and exploit zero-day vulnerabilities before patches are available. The distributed nature of serverless architectures
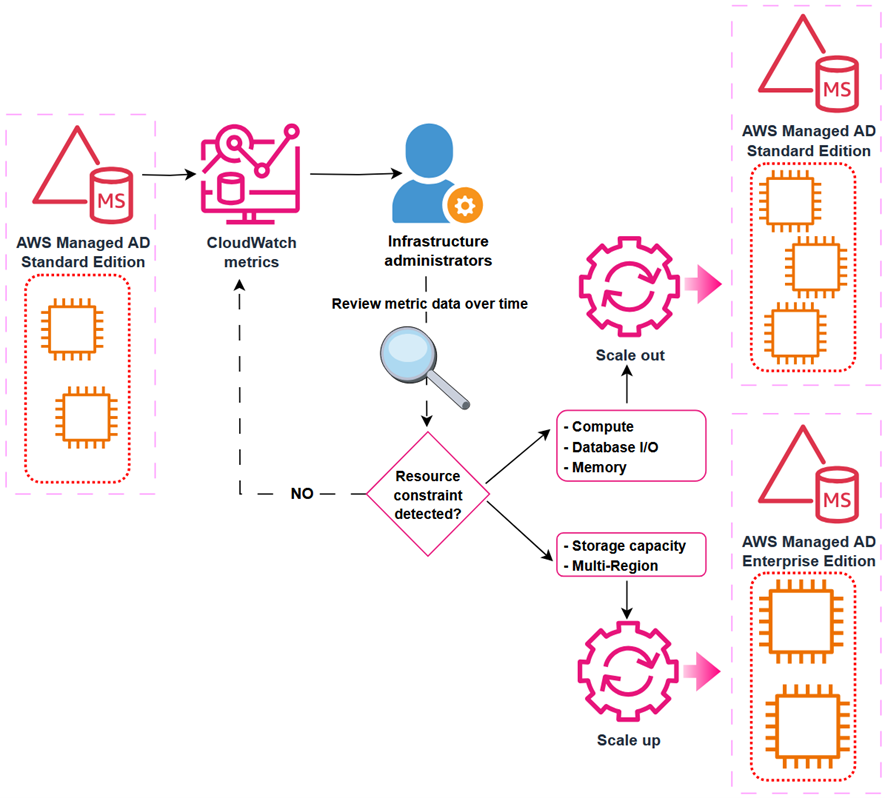
- Explore scaling options for AWS Directory Service for Microsoft Active Directoryby Nahuel Benavidez on January 30, 2026 at 7:51 pm
You can use AWS Directory Service for Microsoft Active Directory as your primary Active Directory Forest for hosting your users’ identities. Your IT teams can continue using existing skills and applications while your organization benefits from the enhanced security, reliability, and scalability of AWS managed services. You can also run AWS Managed Microsoft AD as
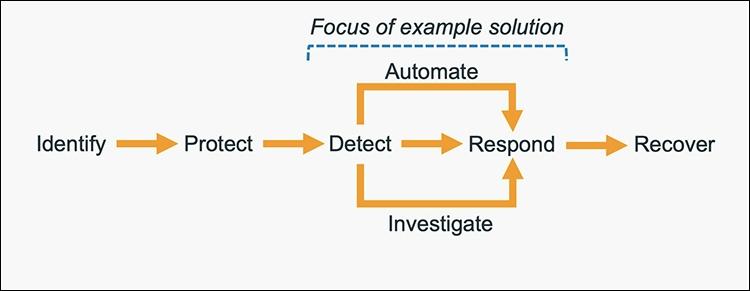
- How to get started with security response automation on AWSby Cameron Worrell on January 29, 2026 at 7:44 pm
December 2, 2019: Original publication date of this post. At AWS, we encourage you to use automation. Not just to deploy your workloads and configure services, but to also help you quickly detect and respond to security events within your AWS environments. In addition to increasing the speed of detection and response, automation also helps
- File integrity monitoring with AWS Systems Manager and Amazon Security Lake by Adam Nemeth on January 27, 2026 at 6:21 pm
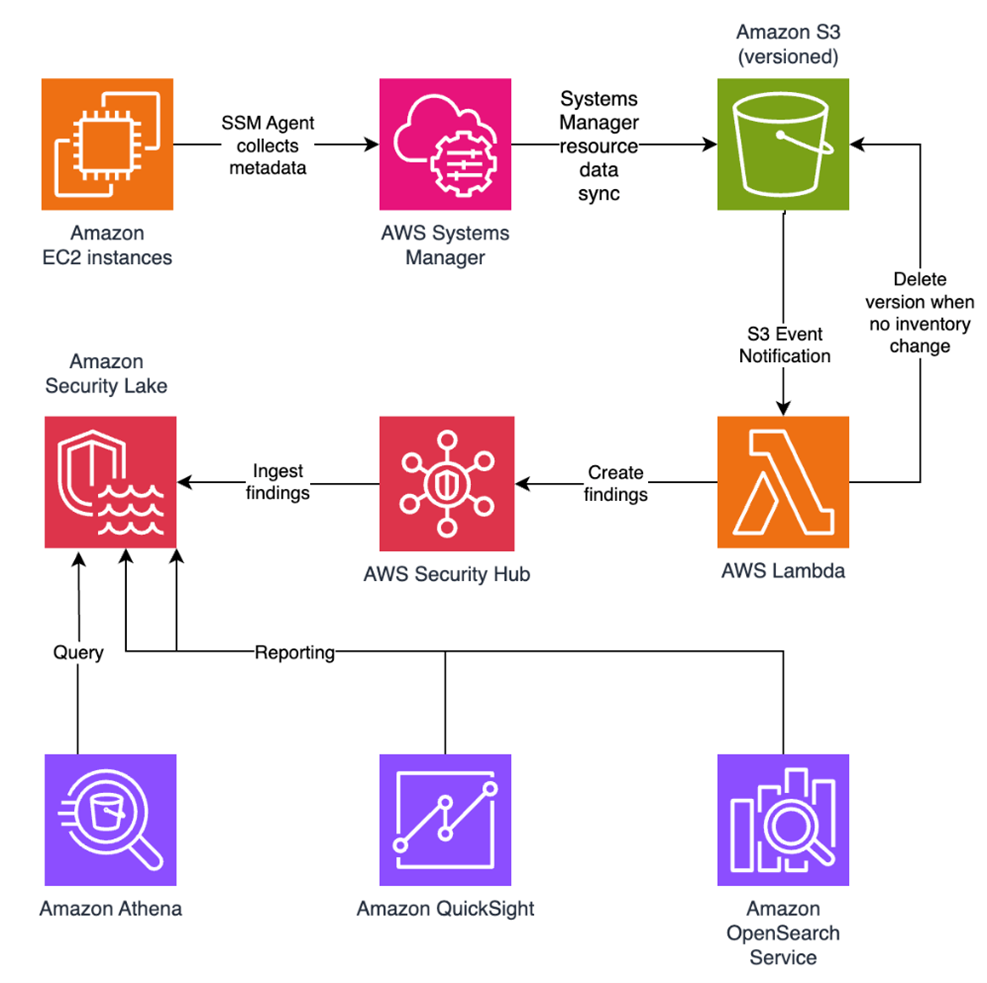
Customers need solutions to track inventory data such as files and software across Amazon Elastic Compute Cloud (Amazon EC2) instances, detect unauthorized changes, and integrate alerts into their existing security workflows. In this blog post, I walk you through a highly scalable serverless file integrity monitoring solution. It uses AWS Systems Manager Inventory to collect
- IAM Identity Center now supports IPv6by Suchintya Dandapat on January 26, 2026 at 8:17 pm
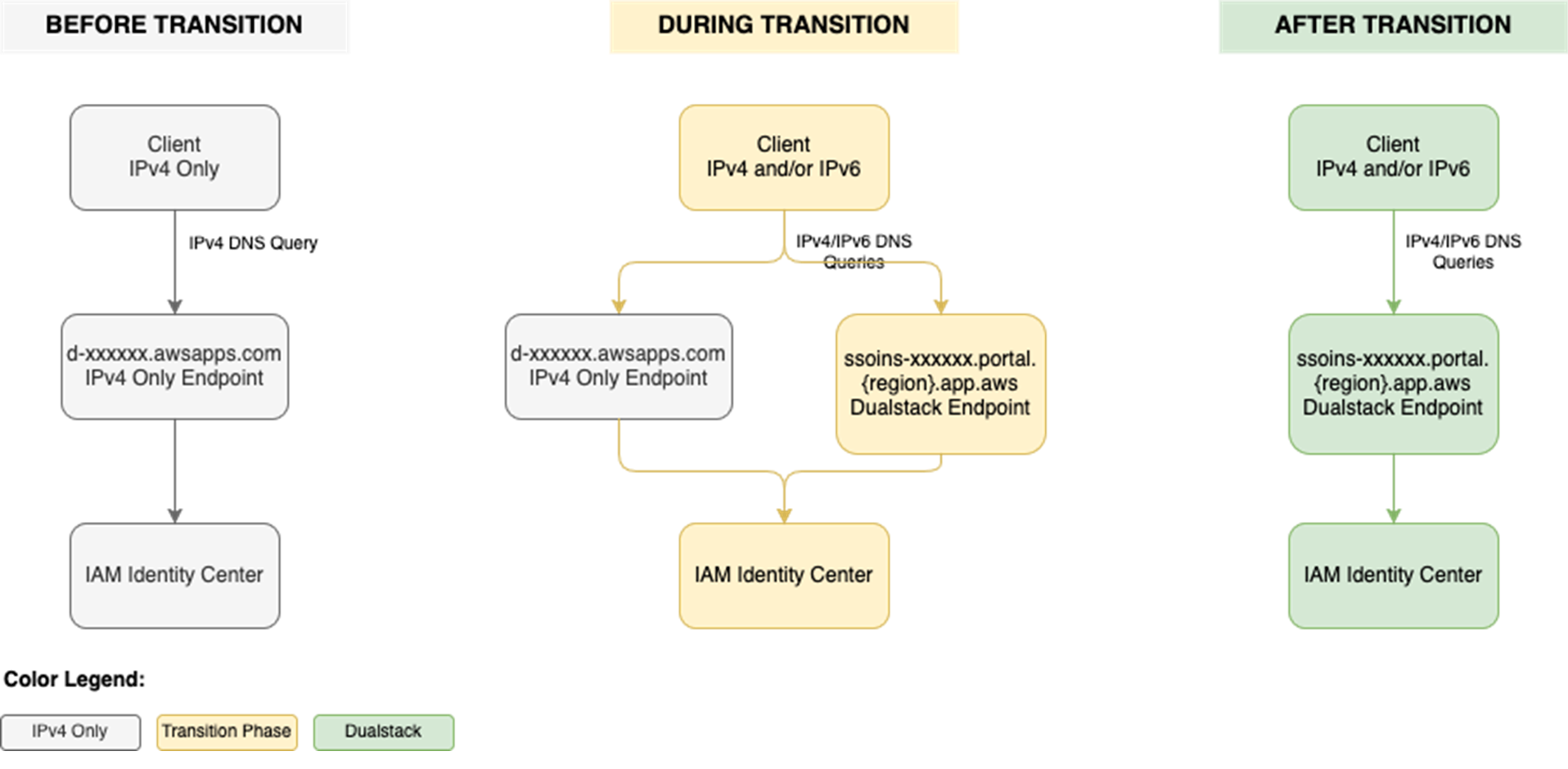
Amazon Web Services (AWS) recommends using AWS IAM Identity Center to provide your workforce access to AWS managed applications—such as Amazon Q Developer—and AWS accounts. Today, we announced IAM Identity Center support for IPv6. To learn more about the advantages of IPv6, visit the IPv6 product page. When you enable IAM Identity center, it provides
- Updated PCI PIN compliance package for AWS CloudHSM now availableby Tushar Jain on January 26, 2026 at 6:11 pm
Amazon Web Services (AWS) is pleased to announce the successful completion of Payment Card Industry Personal Identification Number (PCI PIN) audit for the AWS CloudHSM service. With CloudHSM, you can manage and access your keys on FIPS 140-3 Level 3 validated hardware, protected with customer-owned, single-tenant hardware security module (HSM) instances that run in your
- Updated PCI PIN compliance package for AWS Payment Cryptography now availableby Tushar Jain on January 23, 2026 at 11:14 pm
Amazon Web Services (AWS) is pleased to announce the successful completion of Payment Card Industry Personal Identification Number (PCI PIN) audit for the AWS Payment Cryptography service. With AWS Payment Cryptography, your payment processing applications can use payment hardware security modules (HSMs) that are PCI PIN Transaction Security (PTS) HSM certified and fully managed by
- AWS achieves 2025 C5 Type 2 attestation report with 183 services in scope by Tea Jioshvili on January 23, 2026 at 9:39 pm
Amazon Web Services (AWS) is pleased to announce a successful completion of the 2025 Cloud Computing Compliance Criteria Catalogue (C5) attestation cycle with 183 services in scope. This alignment with C5 requirements demonstrates our ongoing commitment to adhere to the heightened expectations for cloud service providers. AWS customers in Germany and across Europe can run
- AWS renews the GSMA SAS-SM certification for two AWS Regions and expands to cover four new Regionsby Michael Murphy on January 23, 2026 at 8:47 pm
Amazon Web Services (AWS) is pleased to announce the expansion of GSMA Security Accreditation Scheme for Subscription Management (SAS-SM) certification to four new AWS Regions: US West (Oregon), Europe (Frankfurt), Asia Pacific (Tokyo), and Asia Pacific (Singapore). Additionally, the AWS US East (Ohio) and Europe (Paris) Regions have been recertified. All certifications are under the
- Exploring common centralized and decentralized approaches to secrets managementby Brendan Paul on January 23, 2026 at 7:15 pm
One of the most common questions about secrets management strategies on Amazon Web Services (AWS) is whether an organization should centralize its secrets. Though this question is often focused on whether secrets should be centrally stored, there are four aspects of centralizing the secrets management process that need to be considered: creation, storage, rotation, and
- Fall 2025 SOC 1, 2, and 3 reports are now available with 185 services in scopeby Tushar Jain on January 20, 2026 at 7:48 pm
Amazon Web Services (AWS) is pleased to announce that the Fall 2025 System and Organization Controls (SOC) 1, 2, and 3 reports are now available. The reports cover 185 services over the 12-month period from October 1, 2024–September 30, 2025, giving customers a full year of assurance. These reports demonstrate our continuous commitment to adhering to
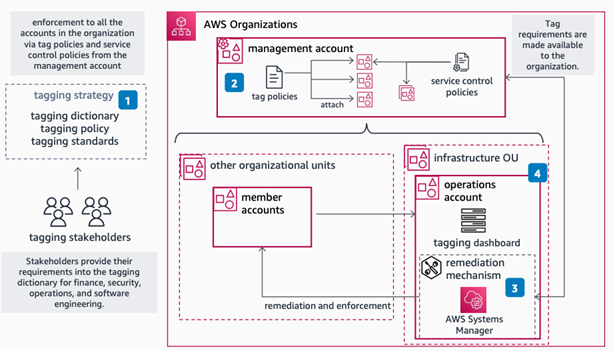
- Implementing data governance on AWS: Automation, tagging, and lifecycle strategy – Part 2by Omar Ahmed on January 16, 2026 at 8:26 pm
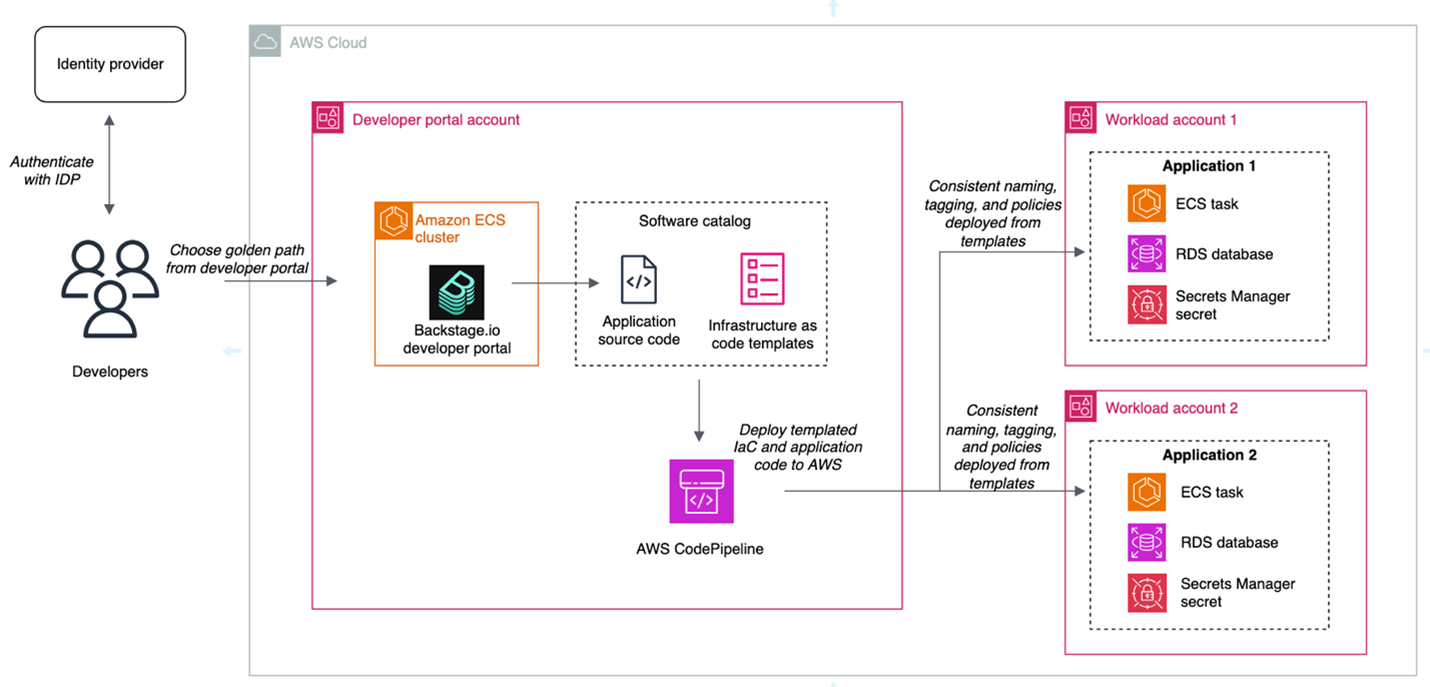
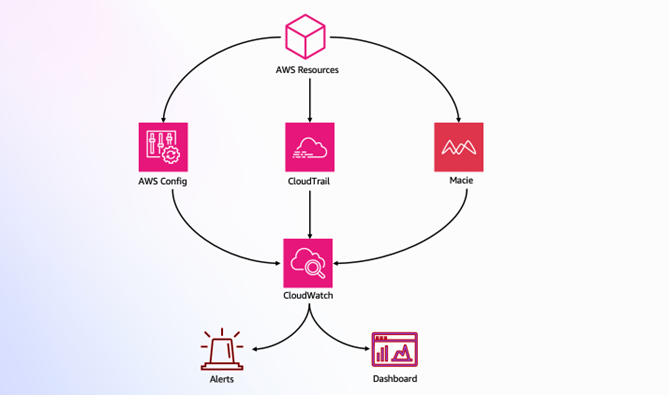
In Part 1, we explored the foundational strategy, including data classification frameworks and tagging approaches. In this post, we examine the technical implementation approach and key architectural patterns for building a governance framework. We explore governance controls across four implementation areas, building from foundational monitoring to advanced automation. Each area builds on the previous one,
- Implementing data governance on AWS: Automation, tagging, and lifecycle strategy – Part 1by Omar Ahmed on January 16, 2026 at 8:26 pm
Generative AI and machine learning workloads create massive amounts of data. Organizations need data governance to manage this growth and stay compliant. While data governance isn’t a new concept, recent studies highlight a concerning gap: a Gartner study of 300 IT executives revealed that only 60% of organizations have implemented a data governance strategy, with
- Streamline security response at scale with AWS Security Hub automationby Ahmed Adekunle on January 13, 2026 at 5:45 pm
A new version of AWS Security Hub, is now generally available, introducing new ways for organizations to manage and respond to security findings. The enhanced Security Hub helps you improve your organization’s security posture and simplify cloud security operations by centralizing security management across your Amazon Web Services (AWS) environment. The new Security Hub transforms
- Fall 2025 PCI DSS compliance package available nowby Tushar Jain on January 13, 2026 at 1:06 am
Amazon Web Services (AWS) is pleased to announce that two additional AWS services and one additional AWS Region have been added to the scope of our Payment Card Industry Data Security Standard (PCI DSS) certification: Newly added services: AWS Security Incident Response AWS Transform Newly added AWS Region: Asia Pacific (Taipei) This certification allows customers
- AWS named Leader in the 2025 ISG report for Sovereign Cloud Infrastructure Services (EU)by Brittany Bunch on January 9, 2026 at 4:11 pm
For the third year in a row, Amazon Web Services (AWS) is named as a Leader in the Information Services Group (ISG) Provider LensTM Quadrant report for Sovereign Cloud Infrastructure Services (EU), published on January 9, 2026. ISG is a leading global technology research, analyst, and advisory firm that serves as a trusted business partner
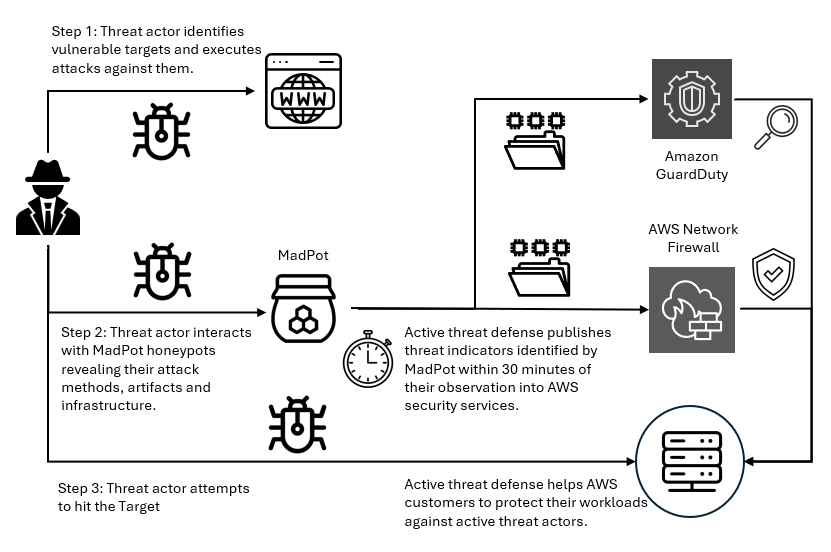
- Real-time malware defense: Leveraging AWS Network Firewall active threat defenseby Rahi Patel on January 8, 2026 at 4:01 pm
Cyber threats are evolving faster than traditional security defense can respond; workloads with potential security issues are discovered by threat actors within 90 seconds, with exploitation attempts beginning within 3 minutes. Threat actors are quickly evolving their attack methodologies, resulting in new malware variants, exploit techniques, and evasion tactics. They also rotate their infrastructure—IP addresses,