AWS Security Blog The latest AWS security, identity, and compliance launches, announcements, and how-to posts.
- Secure AI agent access patterns to AWS resources using Model Context Protocolby Riggs Goodman III on April 14, 2026 at 10:52 pm
AI agents and coding assistants interact with AWS resources through the Model Context Protocol (MCP). Unlike traditional applications with deterministic code paths, agents reason dynamically, choosing different tools or accessing different data depending on context. You must assume an agent can do anything within its granted entitlements, whether OAuth scopes, API keys, or AWS Identity
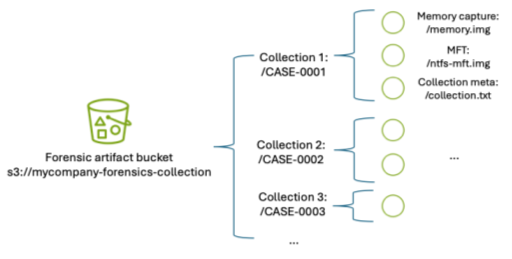
- A framework for securely collecting forensic artifacts into S3 bucketsby Jason Garman on April 8, 2026 at 6:19 pm
When customers experience a security incident, they need to acquire forensic artifacts to identify root cause, extract indicators of compromise (IoCs), and validate remediation efforts. NIST 800-86, Guide to Integrating Forensic Techniques into Incident Response, defines digital forensics as a process comprised of four basic phases: collection, examination, analysis, and reporting. This blog post focuses
- Building AI defenses at scale: Before the threats emergeby Amy Herzog on April 7, 2026 at 6:02 pm
At AWS, we’ve spent decades developing processes and tools that enable us to defend millions of customers simultaneously, wherever they operate around the world. AI has been an extremely helpful addition to the automation our security and threat intelligence teams do every day, and we’re still early in this journey. Our AI-powered log analysis system
- Introducing the Landing Zone Accelerator on AWS Universal Configuration and LZA Compliance Workbookby Kevin Donohue on April 4, 2026 at 9:35 pm
November 20, 2025: Original publication date of this post. This post has been updated to reference the most recent version of the LZA Compliance Workbook published to AWS Artifact in March 2026. We’re pleased to announce the availability of the latest sample security baseline from Landing Zone Accelerator on AWS (LZA)—the Universal Configuration. Developed from
- How AWS KMS and AWS Encryption SDK overcome symmetric encryption boundsby Panos Kampanakis on April 3, 2026 at 3:44 pm
If you run high-scale applications that encrypt large volumes of data, you might be concerned about tracking encryption limits and rotating keys. This post explains how AWS Key Management Service (AWS KMS) and the AWS Encryption SDK handle Advanced Encryption Standard in Galois Counter Mode’s (AES-GCM) encryption limits or bounds automatically by using derived key
- Four security principles for agentic AI systemsby Mark Ryland on April 2, 2026 at 8:45 pm
Agentic AI represents a qualitative shift in how software operates. Traditional software executes deterministic instructions. Generative AI responds to human prompts with output that humans review and use at their discretion. Agentic AI differs from both. Agents connect to software tools and APIs and uses large language models (LLMs) as reasoning engines to plan and
- New compliance guide available: ISO/IEC 27001:2022 on AWSby Ted Tanner on March 31, 2026 at 8:36 pm
We’re excited to announce the release of our latest compliance guide, ISO/IEC 27001:2022 on AWS, which provides practical guidance for organizations designing and operating an Information Security Management System (ISMS) using AWS services. As organizations migrate critical workloads to the cloud, aligning with globally recognized standards such as ISO/IEC 27001:2022 becomes an important step toward
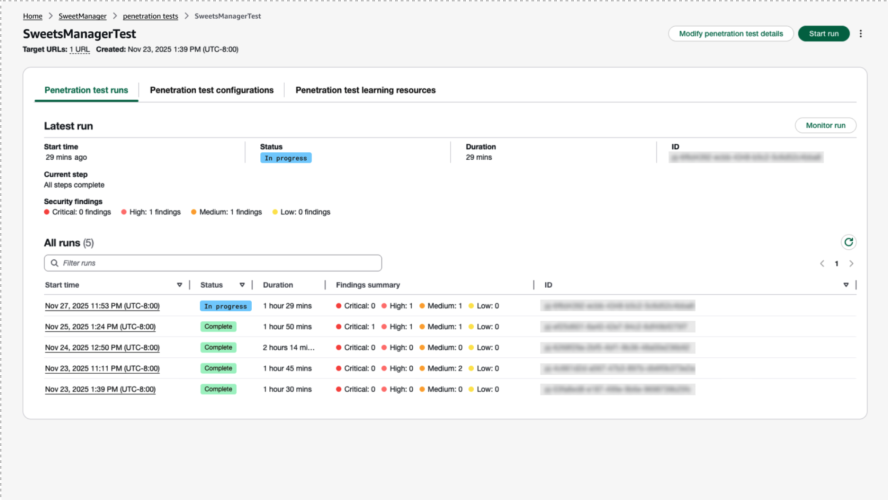
- AWS Security Agent on-demand penetration testing now generally availableby Ayush Singh on March 31, 2026 at 4:13 pm
AWS Security Agent on-demand penetration testing is now generally available, enabling you to run comprehensive security tests across all your applications, not only your most critical ones. This milestone transforms penetration testing from a periodic bottleneck into an on-demand capability that scales with your development velocity across AWS, Azure, GCP, other cloud-providers, and on-premises. With
- Preparing for agentic AI: A financial services approachby Raphael Fuchs on March 26, 2026 at 10:00 pm
Deploying agentic AI in financial services requires additional security controls that address AI-specific risks. This post walks you through comprehensive observability and fine-grained access controls—two critical capabilities for maintaining explainability and accountability in AI systems. You will learn seven design principles and get implementation guidance for meeting regulatory requirements while deploying secure AI solutions. Financial
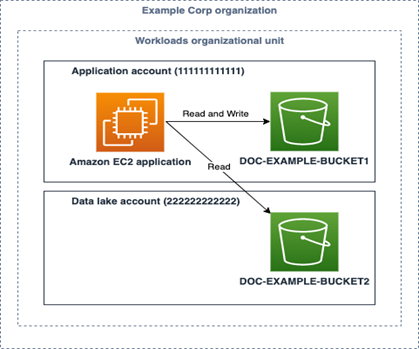
- IAM policy types: How and when to use themby Matt Luttrell on March 23, 2026 at 8:13 pm
June 3, 2022: Original publication date of this post. This post has been updated to add the additional IAM policy types: Resource control policies. You manage access in AWS by creating policies and attaching them to AWS Identity and Access Management (IAM) principals (roles, users, or groups of users) or AWS resources. AWS evaluates these
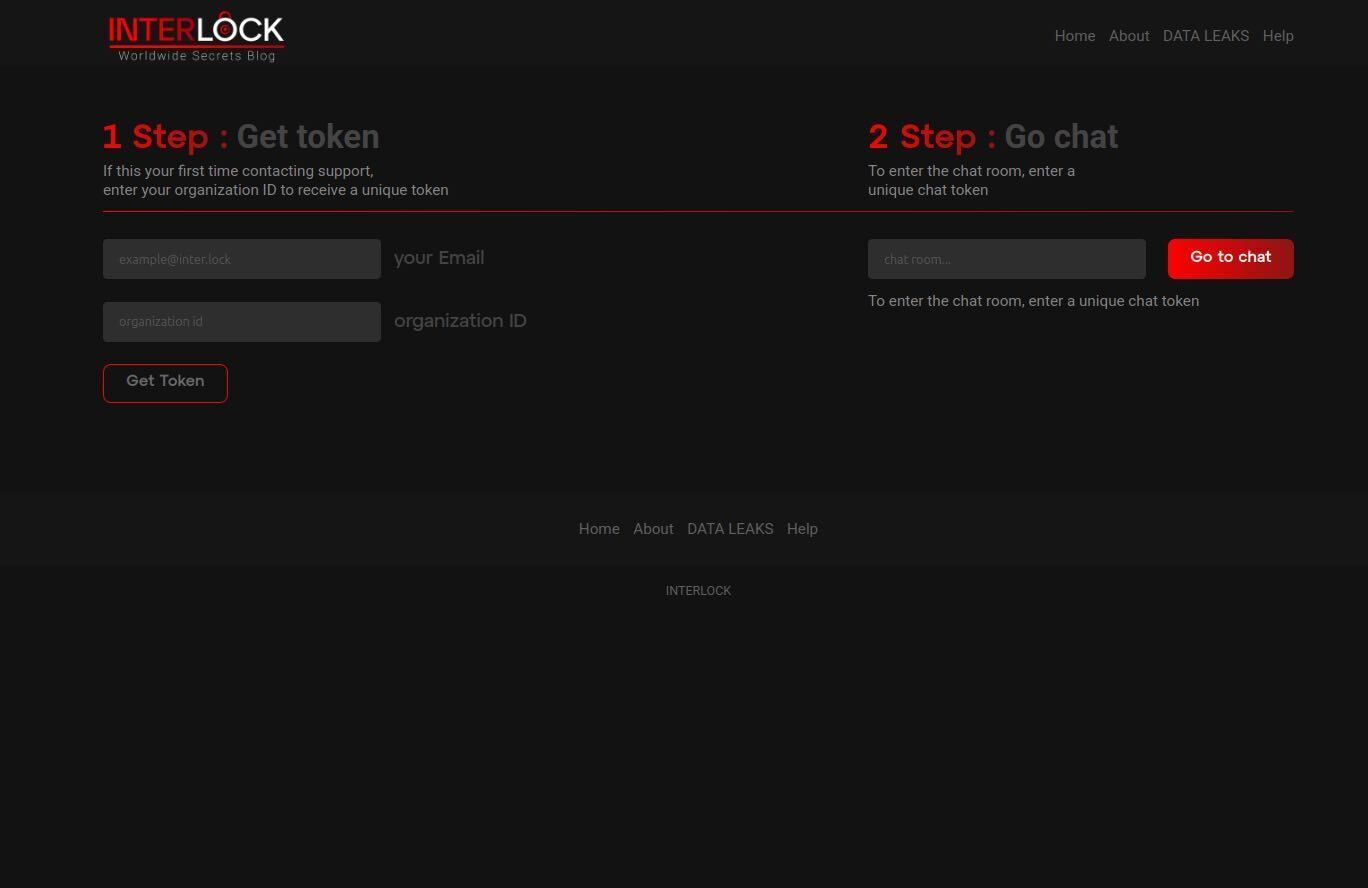
- Amazon threat intelligence teams identify Interlock ransomware campaign targeting enterprise firewallsby CJ Moses on March 18, 2026 at 3:57 pm
Amazon threat intelligence has identified an active Interlock ransomware campaign exploiting CVE-2026-20131, a critical vulnerability in Cisco Secure Firewall Management Center (FMC) Software that could allow an unauthenticated, remote attacker to execute arbitrary Java code as root on an affected device, which was disclosed by Cisco on March 4, 2026. After Cisco’s disclosure, Amazon threat
- AWS completes the second GDV community audit with participant insurers in Germanyby Flamur Abdyli on March 17, 2026 at 8:26 pm
We’re excited to announce that Amazon Web Services (AWS) has completed its second GDV (German Insurance Association) community audit with 36 members from the Germany insurance industry participating, corresponding to over 63% coverage of the German market in terms of insurance premiums. Community audits are an efficient method to provide additional assurance to a group
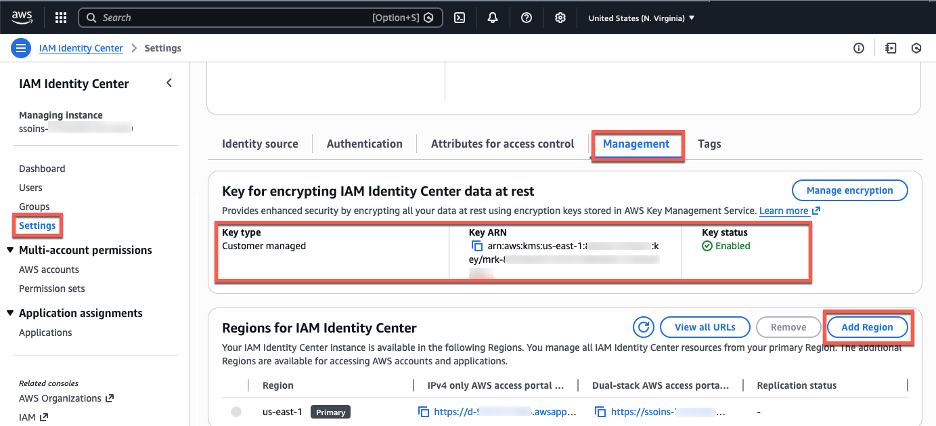
- Deploy AWS applications and access AWS accounts across multiple Regions with IAM Identity Centerby Alex Milanovic on March 14, 2026 at 9:21 pm
If your organization relies on AWS IAM Identity Center for workforce access, you can now extend that access across multiple AWS Regions with multi-Region replication. Previously, AWS access portal was only available in one Region, when you add an additional Region, users get an active access portal endpoint there. If the primary Region experiences a
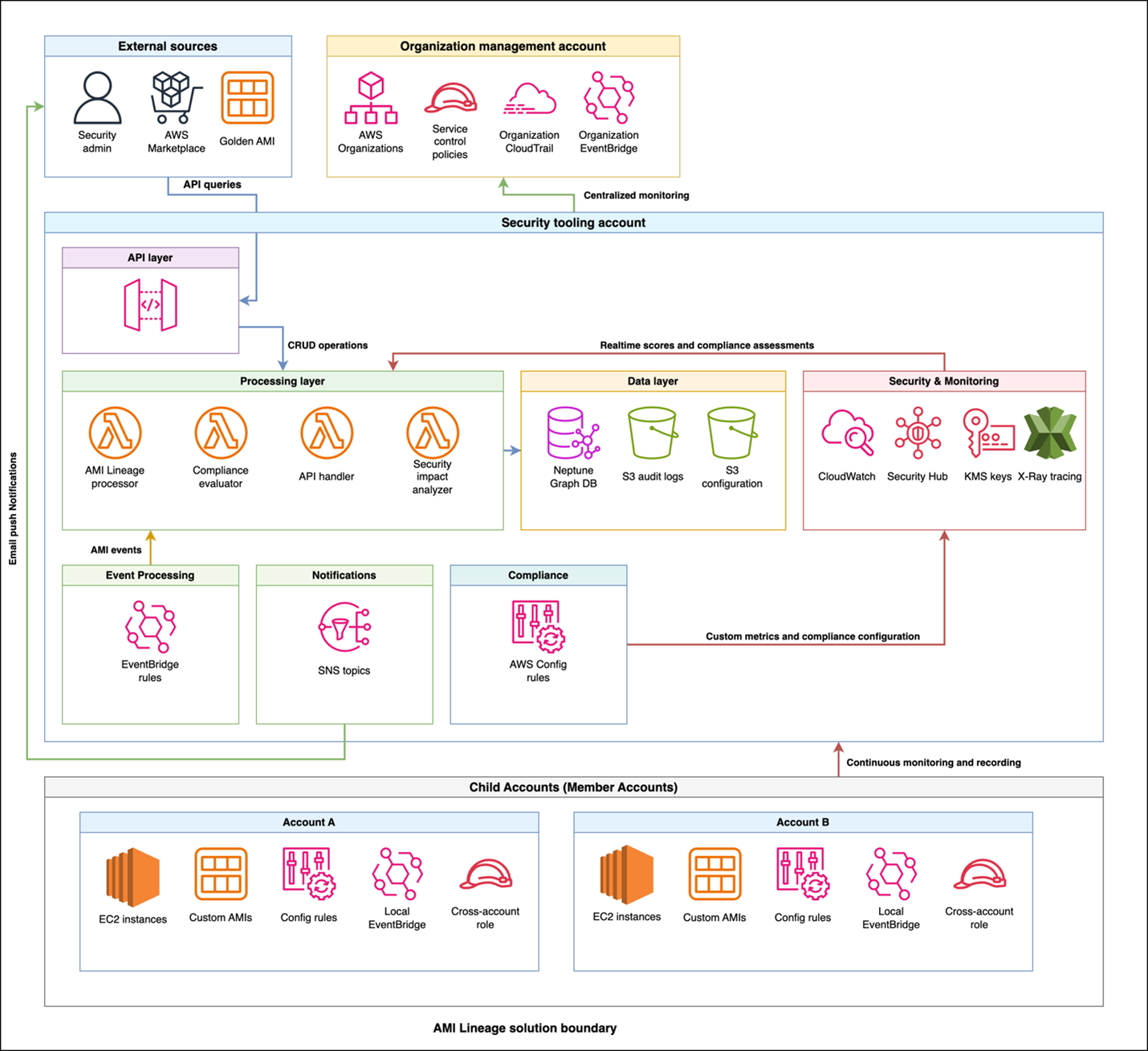
- How to manage the lifecycle of Amazon Machine Images using AMI Lineage for AWSby George’son Tib on March 12, 2026 at 4:59 pm
As organizations scale their cloud infrastructure, maintaining proper lifecycle management of Amazon Machine Images (AMIs) is a critical component of their security and risk management goals. AMIs provide the essential information required to launch Amazon Elastic Compute Cloud (Amazon EC2) instances, however; they present security and compliance challenges if not tracked and managed throughout their
- AWS European Sovereign Cloud achieves first compliance milestone: SOC 2 and C5 reports plus seven ISO certificationsby Julian Herlinghaus on March 10, 2026 at 8:06 pm
In January 2026, we announced the general availability of the AWS European Sovereign Cloud, a new, independent cloud for Europe entirely located within the European Union (EU), and physically and logically separate from all other AWS Regions. The unique approach of the AWS European Sovereign Cloud provides the only fully featured, independently operated sovereign cloud
- Security is a team sport: AWS at RSAC 2026 Conferenceby Idaliz Seymour on March 10, 2026 at 6:31 pm
The RSAC 2026 Conference brings together thousands of professionals, practitioners, vendors, and associations to discuss issues covering the entire spectrum of cybersecurity—a place where innovation meets collaboration and the industry’s brightest minds converge to shape its future. This March, Amazon Web Services (AWS) returns to the annual RSAC Conference in San Francisco to share how
- AWS Security Hub is expanding to unify security operations across multicloud environmentsby Gee Rittenhouse on March 10, 2026 at 2:51 pm
After talking with many customers, one thing is clear: the security challenge has not gotten easier. Enterprises today operate across a complex mix of environments, including on-premises infrastructure, private data centers, and multiple clouds, often with tools that were never designed to work together. The result is enterprise security teams spend more time managing tools
- AWS completes the 2026 annual Dubai Electronic Security Centre (DESC) certification auditby Tariro Dongo on March 5, 2026 at 5:46 pm
We’re excited to announce that Amazon Web Services (AWS) has completed the annual Dubai Electronic Security Centre (DESC) certification audit to operate as a Tier 1 Cloud Service Provider (CSP) for the AWS Middle East (UAE) Region. This alignment with DESC requirements demonstrates our continued commitment to adhere to the heightened expectations for CSPs. Government
- 2025 ISO and CSA STAR certificates are now available with one additional service and one new regionby Chinmaee Parulekar on March 5, 2026 at 12:18 am
Amazon Web Services (AWS) successfully completed the annual recertification audit with no findings for ISO 9001:2015, 27001:2022, 27017:2015, 27018:2019, 27701:2019, 20000-1:2018, 22301:2019, and Cloud Security Alliance (CSA) STAR Cloud Controls Matrix (CCM) v4.0. The objective of the audit was to enable AWS to expand their ISO and CSA STAR certifications to include one new AWS
- Enhanced access denied error messages with policy ARNsby Stella Hie on March 4, 2026 at 5:19 pm
To help you troubleshoot access denied errors, we recently added the Amazon Resource Name (ARN) of the denying policy to access denied error messages. This builds on our 2021 enhancement that added the type of the policy denying the access to access denied error messages. The ARN of the denying policy is only provided in