- Hacking the bomb? What Claude Mythos AI reveals about the gamble of nuclear deterrenceby Thomas Fraise, Postdoctoral research fellow, University of Copenhagen; Sciences Po on May 12, 2026 at 3:01 pm
AI-powered cyber-security: the rise of new frontier platforms like Mythos highlights nuclear arsenals’ potential weak spots, and complicates the gambles inherent in nuclear deterrence.
- Iran’s military forces combine state-of-the-art drones and hackers with out-of-date conventional weaponsby Paul J. Springer, Professor of Comparative Military Studies, Air University on April 15, 2026 at 6:33 pm
Knowing what comes next in Operation Epic Fury is better understood by grasping the evolution of Iran’s military structure and capabilities.
- Commercial space technology is shaping the Iran war – the law can’t keep upby Anna Marie Brennan, Senior Lecturer in Law, University of Waikato on March 11, 2026 at 1:43 am
A new treaty on military space operations is highly unlikely, leaving private companies and militaries to define the boundaries of acceptable conduct in war.
- Is NZ defence and intelligence policy aligning with AUKUS in all but name?by Nicola Macaulay, Senior Tutor and PhD Candidate, Centre for Defence and Security Studies, Te Kunenga ki Pūrehuroa – Massey University on February 3, 2026 at 11:00 pm
NZ appears to be widening its defence and surveillance capabilities across the region, raising questions about strategic alignment, transparency and independence.
- Australia is axing a $7bn military satellite project, leaving defence comms potentially vulnerableby David Tuffley, Senior Lecturer in Applied Ethics & CyberSecurity, Griffith University on November 4, 2024 at 3:50 am
Reports claim the government is cancelling the JP9102 project by Lockheed Martin, meant to deliver an “uncrackable” comms network for the Australian military.
- Diplomacy, sanctions and soft power have failed to deter Iran’s anti-West agenda − could a new Iranian president change that?by Nakissa Jahanbani, Adjunct Lecturer, Pennsylvania State University, Penn State on June 26, 2024 at 12:17 pm
On June 28, Iranians will pick a new president. Relations with the West have been a key campaign issue.
- China turns to private hackers as it cracks down on online activists on Tiananmen Square anniversaryby Christopher K. Tong, Associate Professor of Asian Studies, University of Maryland, Baltimore County on May 31, 2024 at 1:02 pm
Beijing’s cyber operations are largely conducted in the shadows. But a recent leak has shed light on how the state is working with private companies to target online activism.
- Chinese nationalist groups are launching cyber-attacks – often against the wishes of the governmentby Lewis Eves, Teaching Associate in Politics and International Relations, University of Sheffield on May 14, 2024 at 1:42 pm
The Chinese Communist Party has inadvertently given the country’s nationalist movement influence that it’s struggling to contain.
- Governments and hackers agree: the laws of war must apply in cyberspaceby Johanna Weaver, Director, ANU Tech Policy Design Centre, Australian National University on October 25, 2023 at 4:20 am
Cyberspace is a battlefield in modern conflicts – and combatants must follow international humanitarian law to protect civilians.
- The US navy is still more powerful than China’s: more so than the Australian government is letting onby Greg Austin, Adjunct Professor, Australia-China Relations Institute, University of Technology Sydney on August 18, 2023 at 3:23 am
Part of the rationale for acquiring nuclear-powered subs is to counter China’s growing military influence. But the US navy still remains much more powerful than China’s.
- Deterring China isn’t all about submarines. Australia’s ‘cyber offence’ might be its most potent weaponby Greg Austin, Adjunct Professor, Australia-China Relations Institute, University of Technology Sydney on May 4, 2023 at 5:58 am
Contrary to popular belief, cyber security isn’t a strong point for China and this makes it particularly vulnerable to attack in wartime.
- Russia’s shadow war: Vulkan files leak show how Putin’s regime weaponises cyberspaceby Matthew Sussex, Fellow, Strategic and Defence Studies Centre, Australian National University on April 3, 2023 at 8:10 pm
More than 5,000 documents were leaked by an anonymous whistleblower.
- A new cyber taskforce will supposedly ‘hack the hackers’ behind the Medibank breach. It could put a target on Australia’s backby Mamoun Alazab, Associate Professor, College of Engineering, IT and Environment, Charles Darwin University on November 16, 2022 at 2:35 am
Beyond neutralising the cybercriminals behind the Medibank breach, the taskforce will also seek out and attack other potential threats.
- How Ukraine has defended itself against cyberattacks – lessons for the USby Robert Peacock, Assistant Professor of Criminology and Criminal Justice, Florida International University on April 5, 2022 at 12:49 pm
Russian hackers have been attacking Ukraine for years, but with help from US government agencies, businesses and universities, Ukraine’s cyber defenses have grown stronger.
- Cyberattacks have yet to play a significant role in Russia’s battlefield operations in Ukraine – cyberwarfare experts explain the likely reasonsby Nadiya Kostyuk, Assistant Professor of Public Policy, Georgia Institute of Technology on April 4, 2022 at 12:31 pm
Cyberattacks can be devastating, just not on the battlefield, according to researchers who looked at 10 years of armed conflicts around the world.
- Intelligence, information warfare, cyber warfare, electronic warfare – what they are and how Russia is using them in Ukraineby Justin Pelletier, Professor of Practice of Computing Security, Rochester Institute of Technology on March 1, 2022 at 1:44 pm
From jamming satellite signals to spreading disinformation, Russia’s military has sophisticated technologies it’s bringing to the battlefield in Ukraine.
- How much damage could a Russian cyberattack do in the US?by Scott Jasper, Senior Lecturer in National Security Affairs, Naval Postgraduate School on February 25, 2022 at 10:02 pm
Russian information warriors have the capacity to damage critical US infrastructure systems.
- Russia has been at war with Ukraine for years – in cyberspaceby Maggie Smith, Assistant Professor of Public Policy, United States Military Academy West Point on February 7, 2022 at 1:19 pm
Troop buildups and diplomatic negotiations highlight the threat of a major land war in Europe. In cyberspace, Russia has been attacking Ukrainian infrastructure and government operations for years.
- Russia could unleash disruptive cyberattacks against the US – but efforts to sow confusion and division are more likelyby Justin Pelletier, Professor of Practice of Computing Security, Rochester Institute of Technology on January 26, 2022 at 7:55 pm
Russia probably has the means to attack US electrical grids and otherwise create havoc but probably won’t go that far. Instead, watch for disinformation aimed at undermining the US and NATO.
- Cyber Cold War? The US and Russia talk tough, but only diplomacy will ease the threatby Ahmed Ibrahim, Lecturer (Computing and Security), Edith Cowan University on June 25, 2021 at 1:16 am
At this month’s summit, US President Joe Biden warned his counterpart Vladimir Putin of reprisals against ‘persistent malicious cyber-attacks’. But it will take more than posturing to end the stand-off.
- Espionage attempts like the SolarWinds hack are inevitable, so it’s safer to focus on defense – not retaliationby William Akoto, Assistant Professor of International Politics, Fordham University on January 29, 2021 at 1:30 pm
A scholar of cyber conflict sets out why retaliation doesn’t prevent future attacks, and explains what might have a better chance.
- The Sunburst hack was massive and devastating – 5 observations from a cybersecurity expertby Paulo Shakarian, Associate Professor of Computer Science, Arizona State University on December 29, 2020 at 2:17 pm
Cyberwarfare is more like cancer than bombs and bullets. Cybersecurity experts are just beginning to make their diagnosis of the Sunburst hack.
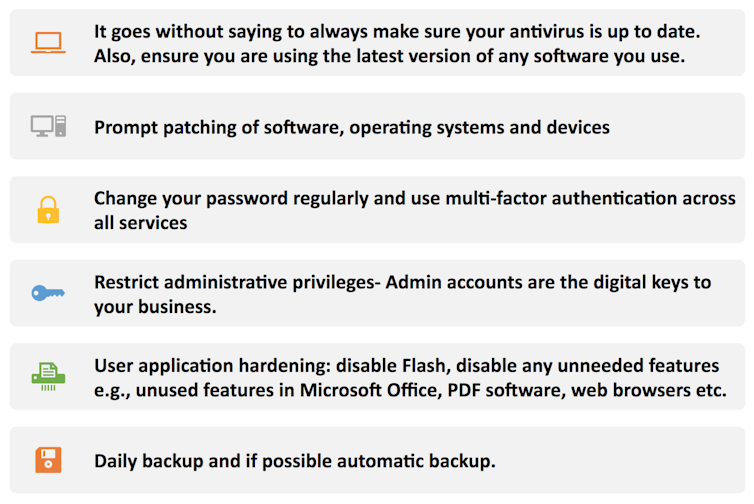
- Australia is under sustained cyber attack, warns the government. What’s going on, and what should businesses do?by Dr Mahmoud Elkhodr, Lecturer in Information and Communication Technologies, CQUniversity Australia on June 19, 2020 at 5:21 am
Australia is coming under sustained cyber attack by a ‘state-based’ actor, says Prime Minister Scott Morrison, as hackers try to exploit vulnerabilities in business and government software systems.
- Government cybersecurity commission calls for international cooperation, resilience and retaliationby Benjamin Jensen, Professor of Strategic Studies, Marine Corps University; Scholar-in-Residence, American University, American University School of International Service on May 12, 2020 at 12:35 pm
In the murky world of cyber espionage and cyber warfare, effective deterrence has long been considered out of reach. A government report argues it’s time to change that.
- Ransomware attack on sheep farmers shows there’s no room for woolly thinking in cyber securityby Roberto Musotto, Cyber Security Cooperative Research Centre Postdoctoral Fellow, Edith Cowan University on March 5, 2020 at 7:06 pm
The wool industry was paralysed for several days after hackers held to ransom the IT system that governs almost all wool sales in Australia and New Zealand. More attacks are a case of if, not when.

Cyber Warfare
We are an ethical website cyber security team and we perform security assessments to protect our clients.