Cyber Exposure Alerts From Tenable
- CVE-2026-20127: Cisco Catalyst SD-WAN Controller/Manager Zero-Day Authentication Bypass Vulnerability Exploited in the Wildby Scott Caveza on February 25, 2026 at 1:51 pm
Exploitation of a maximum severity authentication bypass zero-day vulnerability affecting Cisco Catalyst SD-WAN Controller and Manager has been reported. Immediate patching is recommended to thwart ongoing attacks.Key takeaways:CVE-2026-20127 is an Authentication Bypass Vulnerability affecting Cisco Catalyst SD-WAN Controller and Manager. Patches have been released and no workarounds are currently available. Exploitation in the wild has been observed for this zero-day by a threat actor tracked as UAT-8616. Multiple government agencies have issued alerts on this active exploitation and multiple publications include threat hunting guidance for devices that may have been compromised.BackgroundOn February 25, Cisco released a security advisory (cisco-sa-sdwan-rpa-EHchtZk) to address a maximum severity severity authentication bypass vulnerability in Cisco Catalyst SD-WAN Controller, formerly known as SD-WAN vSmart, and Cisco Catalyst SD-WAN Manager, formerly known as SD-WAN vManage.CVEDescriptionCVSSv3CVE-2026-20127Cisco Catalyst SD-WAN Controller/Manager Authentication Bypass Vulnerability10.0AnalysisCVE-2026-20127 is a critical severity authentication bypass vulnerability in Cisco’s Catalyst SD-WAN Controller and Cisco Catalyst SD-WAN Manager. A remote, unauthenticated attacker could exploit this vulnerability by sending crafted requests to an affected system, allowing them to log into an affected device as a high-privileged user. Using this access, the attacker could modify network configurations for the SD-WAN fabric. According to the advisory, this vulnerability has been exploited in the wild in limited attacks. The advisory further clarifies that this flaw affects vulnerable versions regardless of the device’s configuration and no workaround steps are available, however temporary mitigation guidance is available in the security advisory.CISA releases an Emergency Directive for CVE-2026-20127Coinciding with the release of the security advisory for CVE-2026-20127, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) released emergency directive (ED) 26-03 titled Mitigate Vulnerabilities in Cisco SD-WAN Systems. The ED directs Federal Civilian Executive Branch (FCEB) agencies to take immediate action to identify any Cisco Software-Defined Wide-Area Networking (SD-WAN) systems. The ED notes that CVE-2026-20127 and CVE-2022-20775, a privilege escalation vulnerability affecting SD-WAN devices, pose imminent risk to federal networks. While the ED applies to FCEB agencies, any users who have not yet mitigated their SD-WAN devices for either of these CVEs should take immediate action as threat actors have been observed exploiting these vulnerabilities.As ongoing exploitation has been observed, Cisco’s security advisory does include indicators of compromise which can aid defenders in identifying if their device has been compromised. Nation state-sponsored actors, including Salt Typhoon and Volt Typhoon have been known for past exploitation of Cisco devices, so it’s imperative that immediate action is taken to remediate these vulnerabilities.In addition to CISA, the Australian Signals Directorate’s Australian Cyber Security Centre (ASD’s ACSC) also released an alert warning of exploitation of CVE-2026-20127. The ACSC was credited in the Cisco security advisory for reporting the flaw to Cisco and the ACSC alert also includes a threat hunting guide co-authored by multiple agencies including CISA, the National Security Agency (NSA), the Canadian Centre for Cyber Security (Cyber Centre), the New Zealand National Cyber Security Centre (NCSC-NZ) and the United Kingdom National Cyber Security Centre (NCSC-UK).Exploitation attributed to UAT-8616While the alerts from the government agencies and Cisco’s security advisory did not provide attribution for the attacks targeting CVE-2026-20127, Cisco’s Talos threat intelligence team released a blog attributing the threat activity to UAT-8616. Cisco Talos notes that UAT-8616 is assessed “with high confidence” as “a highly sophisticated cyber threat actor.” The blog by Cisco Talos includes guidance for investigating compromised devices as well as details the exploitation activity that they have observed.Proof of conceptAt the time this blog was published on February 25, no public proof-of-concept (PoC) exploit had been identified. We anticipate that if a PoC is released, additional attackers will begin to leverage the exploit to conduct mass scanning and exploitation against vulnerable devices.SolutionCisco has released patches for affected versions of Cisco Catalyst SD-WAN devices as outlined in the table below:Affected VersionFixed VersionVersions prior to 20.9Migrate to a fixed release20.920.9.8.2 (Estimated to be released on February 27)20.1120.12.6.120.12.520.12.5.320.12.620.12.6.120.1320.15.4.220.1420.15.4.220.1520.15.4.220.1620.18.2.120.1820.18.2.1The advisory notes that versions 20.11, 20.13, 20.14, 20.16 and versions prior to 20.9 have reached their end of maintenance and customers should upgrade to a supported release.Identifying affected systemsA list of Tenable plugins for these vulnerabilities can be found on the individual CVE pages for CVE-2026-20127 and CVE-2022-20775 as they’re released. This link will display all available plugins for these vulnerabilities, including upcoming plugins in our Plugins Pipeline.Additionally, customers can utilize Tenable Attack Surface Management to identify public facing assets running Cisco Catalyst SD-WAN devices by using the following query: Document Title contains Cisco Catalyst SD-WAN Get more informationCisco cisco-sa-sdwan-rpa-EHchtZk Security AdvisoryCisco cisco-sa-sd-wan-priv-E6e8tEdF Security AdvisoryCISA ED 26-03: Mitigate Vulnerabilities in Cisco SD-WAN SystemsAustralian Signals Directorate’s Australian Cyber Security Centre Alert: Exploitation of Cisco SD-WAN appliancesCisco Talos: Active exploitation of Cisco Catalyst SD-WAN by UAT-8616Join Tenable’s Research Special Operations (RSO) Team on Tenable Connect for further discussions on the latest cyber threats.Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.
- Microsoft’s February 2026 Patch Tuesday Addresses 54 CVEs (CVE-2026-21510, CVE-2026-21513)by Research Special Operations on February 10, 2026 at 1:55 pm
2Critical51Important1Moderate0LowMicrosoft addresses 54 CVEs in the February 2026 Patch Tuesday released, including six zero-day vulnerabilities that were exploited in the wild and three publicly disclosed CVEs.Microsoft patched 54 CVEs in its February 2026 Patch Tuesday release, with two rated critical, 51 rated as important and one rated as moderate. We omitted one vulnerability from our counts this month, CVE-2023-2804, a heap based overflow vulnerability in the libjpeg-turbo component.This month’s update includes patches for:.NET.NET and Visual StudioAzure ArcAzure Compute GalleryAzure DevOps ServerAzure Front Door (AFD)Azure FunctionAzure HDInsightsAzure IoT SDKAzure LocalAzure SDKDesktop Window ManagerGithub CopilotGitHub Copilot and Visual StudioInternet ExplorerMailslot File SystemMicrosoft Defender for LinuxMicrosoft Edge for AndroidMicrosoft Exchange ServerMicrosoft Graphics ComponentMicrosoft Office ExcelMicrosoft Office OutlookMicrosoft Office WordPower BIRole: Windows Hyper-VWindows Ancillary Function Driver for WinSockWindows App for MacWindows Cluster Client FailoverWindows Connected Devices Platform ServiceWindows GDI+Windows HTTP.sysWindows KernelWindows LDAP – Lightweight Directory Access ProtocolWindows Notepad AppWindows NTLMWindows Remote Access Connection ManagerWindows Remote DesktopWindows ShellWindows StorageWindows Subsystem for LinuxWindows Win32K – GRFXElevation of privilege (EoP) vulnerabilities accounted for 42.6% of the vulnerabilities patched this month, followed by remote code execution (RCE) vulnerabilities at 20.4%.ImportantCVE-2026-21510 | Windows Shell Security Feature Bypass VulnerabilityCVE-2026-21510 is a security feature bypass vulnerability affecting Windows Shell. It was assigned a CVSSv3 score of 8.8 and was rated as important. According to Microsoft, this flaw was publicly disclosed prior to a patch being made available and was also exploited in the wild as a zero-day. Exploitation requires an attacker to convince an unsuspecting user to open a malicious link or shortcut file. This would allow the attacker to bypass Windows SmartScreen and Windows Shell warnings by exploiting a flaw in Windows Shell components.ImportantCVE-2026-21533 | Windows Remote Desktop Services Elevation of Privilege VulnerabilityCVE-2026-21533 is an EoP vulnerability affecting Windows Remote Desktop Services. It was assigned a CVSSv3 score of 7.8, rated as important and was reportedly exploited in the wild. Successful exploitation allows a local, authenticated attacker to elevate to SYSTEM privileges.ImportantCVE-2026-21519 | Desktop Window Manager Elevation of Privilege VulnerabilityCVE-2026-21519 is an EoP vulnerability affecting Desktop Window Manager, a Windows service used to render the graphical user interface (GUI) in Windows. It was assigned a CVSSv3 score of 7.8 and rated as important. A local, authenticated attacker could exploit this vulnerability to elevate to SYSTEM privileges. According to Microsoft, this vulnerability was exploited in the wild as a zero-day.ImportantCVE-2026-21514 | Microsoft Word Security Feature Bypass VulnerabilityCVE-2026-21514 is a security feature bypass vulnerability affecting Microsoft Word. It was assigned a CVSSv3 score of 7.8 and rated as important. Successful exploitation requires an attacker to convince a user to open a crafted Office file. According to the Microsoft advisory, the preview pane is not an attack vector. This vulnerability was publicly disclosed prior to a patch being made available and was also exploited in the wild as a zero-day. Microsoft credited the discovery of this vulnerability to an Anonymous researcher, Google Threat Intelligence Group, Microsoft Threat Intelligence Center (MSTIC), Microsoft Security Response Center (MSRC) and Office Product Group Security Team.ModerateCVE-2026-21525 | Windows Remote Access Connection Manager Denial of Service VulnerabilityCVE-2026-21525 is a denial of service (DoS) vulnerability affecting Windows Remote Access Connection Manager (also known as RasMan), a tool used for the management of multiple remote desktop connections. It was assigned a CVSSv3 score of 6.2, was rated as important and was exploited in the wild. While no information has been released about the exploitation of this DoS, the advisory credits the 0patch vulnerability research team for reporting this flaw.ImportantCVE-2026-21513 | MSHTML Framework Security Feature Bypass VulnerabilityCVE-2026-21513 is a security feature bypass vulnerability in the MSHTML Framework. It was assigned a CVSSv3 score of 8.8 and rated as important. According to Microsoft, it was both exploited in the wild and publicly disclosed prior to a patch being available. Successful exploitation of this flaw requires an attacker to convince a potential victim into opening either a malicious HTML file or a shortcut (.lnk) file. Like similar security feature bypass flaws, this vulnerability can bypass protection prompts that would caution a user before opening a file.ImportantCVE-2026-21511 | Microsoft Outlook Spoofing VulnerabilityCVE-2026-21511 is a spoofing vulnerability affecting Microsoft Outlook. It was assigned a CVSSv3 score of 7.5 and was rated as important. The spoofing vulnerability is the result of a deserialization of untrusted data flaw, which an attacker can trigger using a crafted email. Microsoft notes that the preview pane is an attack vector for this flaw. CVE-2026-21511 was assessed as “Exploitation More Likely” according to Microsoft’s Exploitability Index.Tenable SolutionsA list of all the plugins released for Microsoft’s February 2026 Patch Tuesday update can be found here. As always, we recommend patching systems as soon as possible and regularly scanning your environment to identify those systems yet to be patched.For more specific guidance on best practices for vulnerability assessments, please refer to our blog post on How to Perform Efficient Vulnerability Assessments with Tenable.Get more informationMicrosoft’s February 2026 Security UpdatesTenable plugins for Microsoft February 2026 Patch Tuesday Security UpdatesJoin Tenable’s Research Special Operations (RSO) Team on Tenable Connect and engage with us in the Threat Roundtable group for further discussions on the latest cyber threats.Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.
- Frequently Asked Questions About Notepad++ Supply Chain Compromiseby Satnam Narang on February 3, 2026 at 9:16 am
Threat actors compromised the update infrastructure for Notepad++, redirecting traffic to an attacker controlled site for targeted espionage purposes.Change logUpdate February 4: This FAQ blog has been updated to note that CVE-2025-15556 was assigned for this security incident.Click here to review the change log historyUpdate February 4: This FAQ blog has been updated to note that CVE-2025-15556 was assigned for this security incident.Key takeaways:Beginning in June 2025, threat actors compromised the infrastructure Notepad++ uses to distribute software updates. The issue has been addressed and Notepad++ have released 8.9.1 which now includes XML signature validation (XMLDSig) for security updates. Reports suggest that the attack was carried out by a Chinese threat actor known as Lotus Blossom.BackgroundTenable’s Research Special Operations (RSO) team has compiled this blog to answer Frequently Asked Questions (FAQ) regarding the disclosure of a supply chain compromise of Notepad++.FAQWhat happened with Notepad++?On February 2, Don Ho, creator of Notepad ++, a source code and text editor for Windows, published a blog detailing the investigation into a supply chain security incident.What kind of security incident is this?According to the blog post, threat actors compromised the infrastructure by which Notepad++ would distribute software updates. This compromise allowed the attackers to redirect update traffic from its intended destination (notepad-plus-plus dot org) to an attacker-controlled site.When did this security incident begin?The security incident began in June 2025.How long did the security incident last for?Roughly six months. The compromised infrastructure was accessible until September 2, 2025. However, because the attackers possessed valid credentials for the internal services of the infrastructure provider, they were able to continue redirecting Notepad++ update traffic until December 2, 2025.Was this incident known prior to February 2?Yes, Ho published a blog post on December 9 regarding the release of version 8.8.9 and noted that security experts “reported incidents of traffic hijacking affecting Notepad++.” The full scope of the security incident wasn’t known at the time as the investigation was ongoing.Has this attack been linked to a specific threat actor?Yes, reports suggest that the attack was carried out by a Chinese threat actor known as Lotus Blossom, also known as Bilbug, Raspberry Typhoon or Thrip.What do we know about Lotus Blossom?Lotus Blossom has been operating since 2009, known for deploying various backdoor malware. Regionally, the group has a penchant for targeting entities across Asia including government and the defense sector.How widespread was this Notepad++ attack?Despite the widespread usage of Notepad++, reports indicate that Lotus Blossom focused more on espionage of certain targets through the deployment of malware rather than financially motivated cybercrime like ransomware or extortion.Were there any vulnerabilities associated with this security incident?On February 2, CVE-2025-15556 was assigned for this security incident. CVE-2025-15556 is a download of code without integrity check vulnerability.Are there software updates available for this security incident?Yes, Notepad++ have released 8.9.1 which now includes XML signature validation (XMLDSig) for security updates with additional signing enforcement expected in version 8.9.2.Affected ProductAffected VersionsFixed VersionsNotepad ++8.9 and lower8.9.1 and aboveHas Tenable released any product coverage for these vulnerabilities?Yes, a Tenable plugin to identify vulnerable versions of Notepad++ can be found here.This link will display all available plugins for these vulnerabilities, including upcoming plugins in our Plugins Pipeline.Get more informationNotepad++ Hijacked by State-Sponsored HackersNotepad++ v8.8.9 release: Vulnerability-fixJoin Tenable’s Research Special Operations (RSO) Team on Tenable Connect and engage with us in the Threat Roundtable group for further discussions on the latest cyber threats.Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.
- CVE-2026-1281, CVE-2026-1340: Ivanti Endpoint Manager Mobile (EPMM) Zero-Day Vulnerabilities Exploitedby Research Special Operations on January 30, 2026 at 1:42 pm
Two Critical vulnerabilities in Ivanti’s popular mobile device management solution have been exploited in the wild in limited attacksKey takeaways:Patch Ivanti EPMM immediately. Both CVE-2026-1281 and CVE-2026-1340 have been exploited in the wild, though impact has been limited so far. Apply the temporary RPM patches now while waiting for version 12.8.0.0 to be released in Q1 2026. Threat actors routinely target Ivanti. These products are a frequent target for attackers, as evidenced by the multiple vulnerabilities in EPMM that have been exploited-in-the-wild since 2020. Exploitation risk is high. With public proof-of-concept code already available for both CVEs, expect widespread scanning and exploitation attempts.BackgroundOn January 29, Ivanti released a security advisory to address two critical severity remote code execution (RCE) vulnerabilities in its Endpoint Manager Mobile (EPMM), formerly known as MobileIron Core, a mobile management software used for mobile device management (MDM), mobile application management (MAM) and mobile content management (MCM).CVEDescriptionCVSSv3CVE-2026-1281Ivanti Endpoint Manager Mobile Remote Code Execution Vulnerability9.8CVE-2026-1340Ivanti Endpoint Manager Mobile Remote Code Execution Vulnerability9.8AnalysisCVE-2026-1281 and CVE-2026-1340 are both code injection vulnerabilities in Ivanti’s EPMM. An unauthenticated attacker could exploit these vulnerabilities to gain remote code execution.Limited exploitation observedAccording to Ivanti, both CVE-2026-1281 and CVE-2026-1340 were exploited as zero-days affecting “a very limited number of customers.” Because its investigation is ongoing, Ivanti has not yet provided any indicators of compromise in relation to these attacks.Historical exploitation of Ivanti Endpoint Mobile ManagerIvanti products in general are a popular target for a variety of attackers. EPMM in particular has been targeted in the past, and the Tenable Research Special Operations (RSO) team has authored several blogs about these vulnerabilities. The following table outlines some of the notable EPMM vulnerabilities over the last six years:CVEDescriptionPublishedTenable BlogsCVE-2025-4428Ivanti Endpoint Manager Mobile Remote Code Execution VulnerabilityMay 2025CVE-2025-4427, CVE-2025-4428: Ivanti Endpoint Manager Mobile (EPMM) Remote Code ExecutionCVE-2025-4427Ivanti Endpoint Manager Mobile Authentication Bypass VulnerabilityMay 2025CVE-2025-4427, CVE-2025-4428: Ivanti Endpoint Manager Mobile (EPMM) Remote Code ExecutionCVE-2023-35082Ivanti Endpoint Manager Mobile Authentication Bypass VulnerabilityAugust 2025N/ACVE-2023-35081Ivanti Endpoint Manager Mobile Remote Arbitrary File Write VulnerabilityJuly 2025CVE-2023-35078: Ivanti Endpoint Manager Mobile (EPMM) / MobileIron Core Unauthenticated API Access VulnerabilityCVE-2023-35078Ivanti Endpoint Manager Mobile Authentication Bypass VulnerabilityJuly 2025CVE-2023-35078: Ivanti Endpoint Manager Mobile (EPMM) / MobileIron Core Unauthenticated API Access VulnerabilityCVE-2020-15505MobileIron Core & Connector Remote Code Execution VulnerabilityOctober 2020CVE-2020-1472: Advanced Persistent Threat Actors Use Zerologon Vulnerability In Exploit Chain with Unpatched VulnerabilitiesProof of conceptAt the time this blog was published on January 30, a public proof-of-concept (PoC) exploit was publicly available. We expect attackers will begin to leverage this PoC to conduct mass scanning and exploitation attempts against vulnerable devices.SolutionIvanti has released temporary updates that can be applied to address these vulnerabilities. According to the advisory, the RPMs supplied should be applied based on the installed version of EPMM. The RPMs will not survive a version upgrade, so if the version is updated, the RPM would need to be applied once again. However, the advisory further notes that an upcoming release, version 12.8.0.0, is expected to be released in Q1 2026., T and this version will include the permanent fix for these CVEs. Once version 12.8.0.0 is released and applied, the RPM scripts will no longer need to be applied.Affected VersionRPM Patch Version12.5.0.0 and priorRPM 12.x.0.x12.5.1.0 and priorRPM 12.x.1.x12.6.0.0 and priorRPM 12.x.0.x12.6.1.0 and priorRPM 12.x.1.x12.7.0.0 and priorRPM 12.x.0.xFor more information on the patches, we strongly recommend reviewing the guidance in the security advisory from Ivanti.Identifying affected systemsA list of Tenable plugins for these vulnerabilities can be found on the individual CVE pages for CVE-2026-1281 and CVE-2026-1340 as they’re released. This link will display all available plugins for these vulnerabilities, including upcoming plugins in our Plugins Pipeline.Additionally, customers can utilize Tenable Attack Surface Management to identify public facing assets running Ivanti devices by using the following subscription: Get more informationIvanti Security Advisory: Ivanti Endpoint Manager Mobile (EPMM) (CVE-2026-1281 & CVE-2026-1340)Someone Knows Bash Far Too Well, And We Love It (Ivanti EPMM Pre-Auth RCEs CVE-2026-1281 & CVE-2026-1340)Join Tenable’s Research Special Operations (RSO) Team on Tenable Connect and engage with us in the Threat Roundtable group for further discussions on the latest cyber threats.Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.
- Oracle January 2026 Critical Patch Update Addresses 158 CVEsby Research Special Operations on January 20, 2026 at 4:47 pm
Oracle addresses 158 CVEs in its first quarterly update of 2026 with 337 patches, including 27 critical updates.Key takeaways:The first Critical Patch Update (CPU) for 2026, contains fixes for 158 unique CVEs in 337 security updates. 27 issues (8% of all patches) were assigned a critical severity rating. CVE-2026-21945, a high severity Server-Side Request Forgery (SSRF) vulnerability in Oracle Java was discovered by Tenable Research.BackgroundOn January 20, Oracle released its Critical Patch Update (CPU) for January 2026, the first quarterly update of 2026. This CPU contains fixes for 158 unique CVEs in 337 security updates across 30 Oracle product families. Out of the 337 security updates published this quarter, 8% of patches were assigned a critical severity. High severity patches accounted for the bulk of security patches at 45.7%, followed by medium severity patches at 42.4%.This quarter’s update includes 27 critical patches across 13 CVEs.SeverityIssues PatchedCVEsCritical2713High15467Medium14369Low139Total337158AnalysisThis quarter, the Oracle Zero Data Loss Recovery Appliance product family contained the highest number of patches at 56, accounting for 16.6% of the total patches, followed by Oracle Enterprise Manager at 51 patches, which accounted for 15.1% of the total patches.A full breakdown of the patches for this quarter can be seen in the following table, which also includes a count of vulnerabilities that can be exploited over a network without authentication.Oracle Product FamilyNumber of PatchesRemote Exploit without AuthOracle Zero Data Loss Recovery Appliance5634Oracle Enterprise Manager5147Oracle E-Business Suite3833Oracle Java SE207Oracle MySQL1410Oracle PeopleSoft1411Oracle Systems141Oracle HealthCare Applications1210Oracle JD Edwards1210Oracle Hospitality Applications1111Oracle Retail Applications108Oracle Commerce87Oracle Communications82Oracle Financial Services Applications86Oracle Database Server72Oracle TimesTen In-Memory Database76Oracle Hyperion75Oracle Analytics66Oracle GoldenGate53Oracle Fusion Middleware53Oracle Siebel CRM51Oracle Supply Chain54Oracle Construction and Engineering44Oracle Health Sciences Applications44Oracle APEX10Oracle Essbase11Oracle Graph Server and Client10Oracle Key Vault10Oracle NoSQL Database11Oracle Secure Backup11Tenable Research discoveryAs part of the January CPU, Oracle addressed CVE-2026-21945, a high severity Server-Side Request Forgery (SSRF) vulnerability in Oracle Java that is remotely exploitable without authentication. When successfully exploited, it can be leveraged to exhaust resources, causing a denial-of-service (DoS) condition. You can read more about the discovery in our blog post and in our Tenable Research Advisory (TRA).SolutionCustomers are advised to apply all relevant patches in this quarter’s CPU. Please refer to the January 2026 advisory for full details.Identifying affected systemsA list of Tenable plugins to identify these vulnerabilities will appear here as they’re released. This link uses a search filter to ensure that all matching plugin coverage will appear as it is released.Get more informationTenable Blog: Tenable Discovers SSRF Vulnerability in Java TLS Handshakes That Creates DoS RiskTenable Research Advisory: TRA-2026-03Oracle Critical Patch Update Advisory – January 2026Oracle January 2026 Critical Patch Update Risk MatricesOracle Advisory to CVE MapJoin Tenable’s Research Special Operations (RSO) Team on Tenable Connect and engage with us in the Threat Roundtable group for further discussions on the latest cyber threats.Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.
- CVE-2025-64155: Exploit Code Released for Critical Fortinet FortiSIEM Command Injection Vulnerabilityby Scott Caveza on January 14, 2026 at 3:15 pm
Exploit code has been published for CVE-2025-64155, a critical command injection vulnerability affecting Fortinet FortiSIEM devices.Key takeaways:CVE-2025-64155 is a critical operating system (OS) command injection vulnerability affecting Fortinet FortiSIEM. Fortinet vulnerabilities have historically been common targets for cyber attackers, with 23 Fortinet CVEs currently on the CISA KEV list. Public exploit code has been released, increasing the likelihood that CVE-2025-64155 could be exploited by attackers.BackgroundOn January 13, Fortinet published a security advisory (FG-IR-25-772) for CVE-2025-64155, a critical command injection vulnerability affecting Fortinet FortiSIEM.CVEDescriptionCVSSv3CVE-2025-64155Fortinet FortiSIEM Command Injection Vulnerability9.4AnalysisCVE-2025-64155 is a critical operating system (OS) command injection vulnerability affecting Fortinet FortiSIEM. A remote, unauthenticated attacker can exploit this flaw to execute arbitrary code using specially crafted requests.Historical Exploitation of Fortinet DevicesFortinet vulnerabilities have historically been common targets for cyber attackers, with 23 Fortinet CVEs currently on the Cybersecurity and Infrastructure Security Agency’s (CISA) Known Exploited Vulnerabilities (KEV) list. At the time this blog was published on January 14, CVE-2025-64155 had not been added to the KEV, however we anticipate that it is likely to be added in the near future.As Fortinet devices have been popular targets for attackers, the Tenable Research Special Operations Team (RSO) has authored several blogs about vulnerabilities affecting these devices. The following table outlines some of the most impactful Fortinet vulnerabilities in recent years.CVEDescriptionPublishedTenable BlogCVE-2025-64446Fortinet FortiWeb Path Traversal VulnerabilityNovember 2025CVE-2025-64446: Fortinet FortiWeb Zero-Day Path Traversal Vulnerability Exploited in the WildCVE-2025-25256Fortinet FortiSIEM Command Injection VulnerabilityAugust 2025CVE-2025-25256: Proof of Concept Released for Critical Fortinet FortiSIEM Command Injection VulnerabilityCVE-2025-32756Fortinet FortiVoice, FortiMail, FortiNDR, FortiRecorder and FortiCamera Arbitrary Code Execution VulnerabilityMay 2025CVE-2025-32756: Zero-Day Vulnerability in Multiple Fortinet Products Exploited in the WildCVE-2024-55591Fortinet Authentication Bypass in FortiOS and FortiProxyJanuary 2025CVE-2024-55591: Fortinet Authentication Bypass Zero-Day Vulnerability Exploited in the WildCVE-2024-21762Fortinet FortiOS Out-of-bound Write Vulnerability in sslvpndFebruary 2024CVE-2024-21762: Critical Fortinet FortiOS Out-of-Bound Write SSL VPN VulnerabilityCVE-2023-27997FortiOS and FortiProxy Heap-Based Buffer Overflow VulnerabilityJune 2023CVE-2023-27997: Heap-Based Buffer Overflow in Fortinet FortiOS and FortiProxy SSL-VPN (XORtigate)CVE-2022-42475FortiOS and FortiProxy Heap-Based Buffer Overflow VulnerabilityDecember 2022CVE-2022-42475: Fortinet Patches Zero Day in FortiOS SSL VPNsAA23-250A: Multiple Nation-State Threat Actors Exploit CVE-2022-47966 and CVE-2022-42475CVE-2022-40684FortiOS and FortiProxy Authentication Bypass VulnerabilityOctober 2022CVE-2022-40684: Critical Authentication Bypass in FortiOS and FortiProxyProof of conceptOn January 13, in coordination with the release of the advisory by Fortinet, researchers at Horizon3.ai published a technical writeup as well as a proof of concept for CVE-2025-64155. While there has been no reports of in-the-wild exploitation, we anticipate that attackers will quickly incorporate this exploit into their attacks.SolutionThe following table details the affected and fixed versions of Fortinet FortiSIEM devices for CVE-2025-64155:Product VersionAffected RangeFixed VersionFortiSIEM 6.76.7.0 through 6.7.10Migrate to a fixed releaseFortiSIEM 7.07.0.0 through 7.0.4Migrate to a fixed releaseFortiSIEM 7.17.1.0 through 7.1.87.1.9 or aboveFortiSIEM 7.27.2.0 through 7.2.67.2.7 or aboveFortiSIEM 7.37.3.0 through 7.3.47.3.5 or aboveFortiSIEM 7.47.4.07.4.1 or aboveFortiSIEM 7.5Not affected-FortiSIEM CloudNot affected-Fortinet’s security advisory advises if immediate patching is not able to be performed, they recommend limiting access to the phMonitor port of 7900. We strongly recommend reviewing the advisory for updates as well as the latest on mitigation recommendations.Identifying affected systemsA list of Tenable plugins for this vulnerability can be found on the individual CVE page for CVE-2025-64155 as they’re released. This link will display all available plugins for this vulnerability, including upcoming plugins in our Plugins Pipeline.Additionally, customers can utilize Tenable Attack Surface Management to identify public facing assets running Fortinet devices by using the following subscription: Get more informationFortinet FG-IR-25-772 Security AdvisoryHorizon3.AI Technical WriteupJoin Tenable’s Research Special Operations (RSO) Team on the Tenable Community.Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.
- Microsoft’s January 2026 Patch Tuesday Addresses 113 CVEs (CVE-2026-20805)by Research Special Operations on January 13, 2026 at 1:37 pm
8Critical105Important0Moderate0LowMicrosoft addresses 113 CVEs in the first Patch Tuesday of 2026, with two zero-days, including one that was exploited in the wild.Microsoft patched 113 CVEs in its January 2026 Patch Tuesday release, with eight rated critical and 105 rated as important. Our counts omitted one CVE that was assigned by MITRE, CVE-2023-31096.This month’s update includes patches for:Azure Connected Machine AgentAzure Core shared client library for PythonCapability Access Management Service (camsvc)Connected Devices Platform Service (Cdpsvc)Desktop Window ManagerDynamic Root of Trust for Measurement (DRTM)Graphics KernelHost Process for Windows TasksInbox COM ObjectsMicrosoft Graphics ComponentMicrosoft OfficeMicrosoft Office ExcelMicrosoft Office SharePointMicrosoft Office WordPrinter Association ObjectSQL ServerTablet Windows User Interface (TWINUI) SubsystemWindows Admin CenterWindows Ancillary Function Driver for WinSockWindows Client-Side Caching (CSC) ServiceWindows Clipboard ServerWindows Cloud Files Mini Filter DriverWindows Common Log File System DriverWindows DWMWindows Deployment ServicesWindows Error ReportingWindows File ExplorerWindows HTTP.sysWindows HelloWindows Hyper-VWindows InstallerWindows Internet Connection Sharing (ICS)Windows KerberosWindows KernelWindows Kernel MemoryWindows Kernel-Mode DriversWindows LDAP – Lightweight Directory Access ProtocolWindows Local Security Authority Subsystem Service (LSASS)Windows Local Session Manager (LSM)Windows Management ServicesWindows MediaWindows NDISWindows NTFSWindows NTLMWindows Remote AssistanceWindows Remote Procedure CallWindows Remote Procedure Call Interface Definition Language (IDL)Windows Routing and Remote Access Service (RRAS)Windows SMB ServerWindows Secure BootWindows Server Update ServiceWindows ShellWindows TPMWindows Telephony ServiceWindows Virtualization-Based Security (VBS) EnclaveWindows WalletServiceWindows Win32K – ICOMPElevation of privilege (EoP) vulnerabilities accounted for 49.6% of the vulnerabilities patched this month, followed by remote code execution (RCE) vulnerabilities at 19.5%.ImportantCVE-2026-20805 | Desktop Window Manager Information Disclosure VulnerabilityCVE-2026-20805 is an information disclosure vulnerability affecting Desktop Window Manager. It was assigned a CVSSv3 score of 5.5 and was rated as important. Successful exploitation allows an authenticated attacker to access sensitive data. According to Microsoft, this vulnerability was exploited in the wild as a zero-day.Additionally, Microsoft patched another Desktop Window Manager vulnerability this month. CVE-2026-20871 is an EoP vulnerability that was assigned a CVSSv3 score of 7.8 and was rated as important. Contrary to CVE-2026-20805, CVE-2026-20871 was not exploited in the wild, although it was assessed as “Exploitation More Likely” according to Microsoft’s Exploitability Index.ImportantCVE-2026-21265 | Secure Boot Certificate Expiration Security Feature Bypass VulnerabilityCVE-2026-21265 is a security feature bypass in the Windows Secure Boot. It was assigned a CVSSv3 score of 6.4 and is rated important. It was assessed as “Exploitation Less Likely.”Microsoft certificates are stored in the Unified Extensible Firmware Interface (UEFI) Key Enrollment Key (also known as Key Exchange or KEK) and DB. These certificates are reaching their expiration date, so these certificates need to be updated to ensure Secure Boot functionality remains and to prevent future issues from arising. The following are the certificates set to expire in 2026:Certificate Authority (CA)Expiration DatePurposeLocationMicrosoft Corporation KEK CA 2011June 24, 2026Signs updates to the DB and DBXKEKMicrosoft Corporation UEFI CA 2011June 27, 2026Signs third party boot loaders, Option ROMs and moreDBMicrosoft Windows Production PCA 2011October 19, 2026Signs the Windows Boot ManagerDBThis vulnerability is considered “Publicly Disclosed” because the information about the expiration and the location of these certificates are public.CriticalCVE-2026-20952 and CVE-2026-20953 | Microsoft Office Remote Code Execution VulnerabilityCVE-2026-20952 and CVE-2026-20953 are RCE vulnerabilities affecting Microsoft Office. Each of these vulnerabilities were assigned a CVSSv3 score of 8.4, rated as critical and assessed as “Exploitation Less Likely.” An attacker could exploit these flaws through social engineering by sending the malicious Microsoft Office document file to an intended target. Successful exploitation would grant code execution privileges to the attacker.Despite being flagged as “Exploitation Less Likely,” Microsoft notes that the Preview Pane is an attack vector for both vulnerabilities, which means exploitation does not require the target to open the file.ImportantCVE-2026-20840 and CVE-2026-20922 | Windows NTFS Remote Code Execution VulnerabilityCVE-2026-20840 and CVE-2026-20922 are RCE vulnerabilities affecting Windows New Technology File System (NTFS). Both were assigned CVSSv3 scores of 7.8 and are rated as important. Microsoft assessed both of these flaws as “Exploitation More Likely.” According to Microsoft, both these flaws stem from heap-based buffer overflows which can be exploited to execute arbitrary code on an affected system. Both advisories also note that any authenticated attacker can exploit these flaws, regardless of privilege level.Tenable SolutionsA list of all the plugins released for Microsoft’s January 2026 Patch Tuesday update can be found here. As always, we recommend patching systems as soon as possible and regularly scanning your environment to identify those systems yet to be patched.For more specific guidance on best practices for vulnerability assessments, please refer to our blog post on How to Perform Efficient Vulnerability Assessments with Tenable.Get more informationMicrosoft’s January 2026 Security UpdatesTenable plugins for Microsoft January 2026 Patch Tuesday Security UpdatesJoin Tenable’s Research Special Operations (RSO) Team on Tenable Connect and engage with us in the Threat Roundtable group for further discussions on the latest cyber threats.Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.
- CVE-2025-14847 (MongoBleed): MongoDB Memory Leak Vulnerability Exploited in the Wildby Scott Caveza on December 29, 2025 at 11:09 am
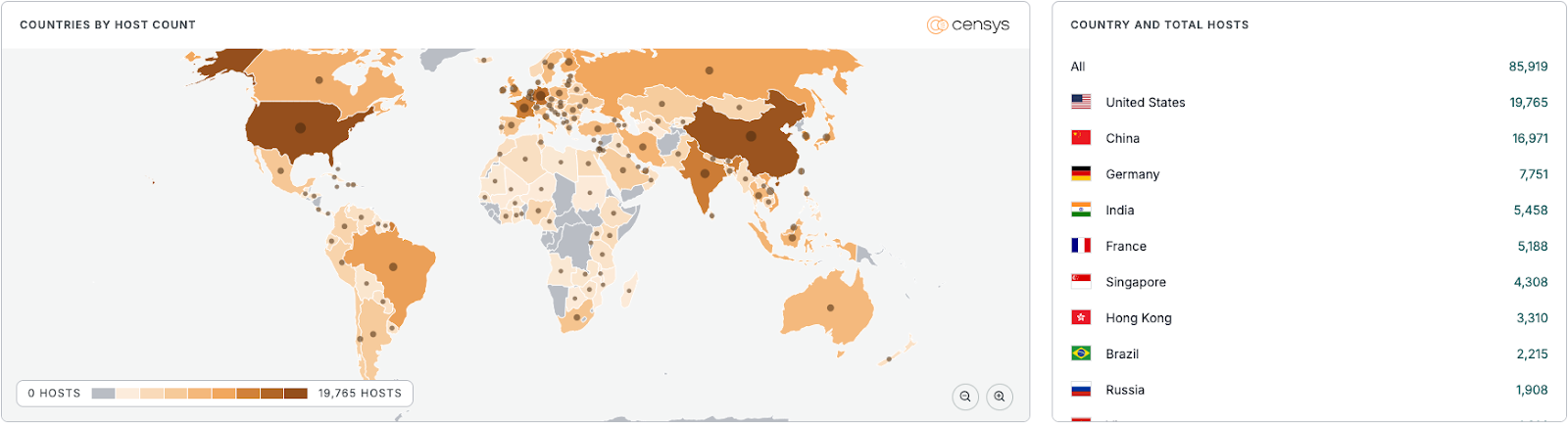
A recently disclosed vulnerability affecting MongoDB instances has been reportedly exploited in the wild. Exploit code has been released for this flaw dubbed MongoBleed.Key takeaways:MongoBleed is a memory leak vulnerability affecting multiple versions of MongoDB. Exploitation of MongoDB has been observed and exploit code is publicly available . Immediate patching is recommended as the combination of public exploit code and a high number of potentially affected internet connected instances make this a flaw attackers will be targeting.BackgroundOn December 19, MongoDB issued a security advisory to address a vulnerability affecting the zlib implementation of MongoDB.CVEDescriptionCVSSv3VPRCVE-2025-14847MongoDB Uninitialized Memory Leak Vulnerability (“MongoBleed”)7.58.0*Please note: Tenable’s Vulnerability Priority Rating (VPR) scores are calculated nightly. This blog post was published on December 29 and reflects VPR at that time.AnalysisCVE-2025-14847 is a memory leak vulnerability affecting MongoDB instances in which zlib compression is enabled. A flaw in how MongoDB implements zlib decompression could allow unauthenticated attackers to leak uninitialized memory, which can contain sensitive data including credentials, session tokens and API keys. This flaw was dubbed “MongoBleed” by Elastic Security researcher Joe Desimone, who published a proof-of-concept demonstrating the vulnerability. While exploitation does require zlib compression to be enabled and a vulnerable MongoDB version to be internet exposed, reports of in the wild exploitation have already begun.According to Censys, there are over 87,000 potentially vulnerable instances of MongoDB that have been identified, with the largest concentration being found in the United States.Source: CensysProof of conceptOn December 25, a public proof-of-concept (PoC) was released on GitHub. This PoC demonstrates how data can be leaked from uninitialized memory. According to the PoC details, the following data could be leaked:MongoDB internal logs and stateWiredTiger storage engine configurationSystem /proc data (meminfo, network stats)Docker container pathsConnection UUIDs and client IPsSolutionMongoDB has released patches to address this vulnerability as outlined in the table below:Affected VersionFixed VersionMongoDB Server v3.6 (All Versions)Upgrade to MongoDB 8.2.3, 8.0.17, 7.0.28, 6.0.27, 5.0.32, 4.4.30 or laterMongoDB Server v4.0 (All Versions)Upgrade to MongoDB 8.2.3, 8.0.17, 7.0.28, 6.0.27, 5.0.32, 4.4.30 or laterMongoDB Server v4.2 (All Versions)Upgrade to MongoDB 8.2.3, 8.0.17, 7.0.28, 6.0.27, 5.0.32, 4.4.30 or laterMongoDB 4.4.0 through 4.4.29Upgrade to MongoDB 4.4.30 or laterMongoDB 5.0.0 through 5.0.31Upgrade to MongoDB 5.0.32 or laterMongoDB 6.0.0 through 6.0.26Upgrade to MongoDB 6.0.27 or laterMongoDB 7.0.0 through 7.0.26Upgrade to MongoDB 7.0.28 or laterMongoDB 8.0.0 through 8.0.16Upgrade to MongoDB 8.0.17 or laterMongoDB 8.2.0 through 8.2.2Upgrade to MongoDB 8.2.3 or laterAccording to the MongoDB security advisory, if immediate patching is not able to be performed, the workaround suggestion is to disable zlib compression. In addition, we recommend that you limit network access to MongoDB instances to trusted IP addresses only. While this step was not outlined in the advisory, it has been recommended as a security best practice by MongoDB.Identifying affected systemsA list of Tenable plugins for this vulnerability can be found on the individual CVE page for CVE-2025-14847 as they’re released. This link will display all available plugins for this vulnerability, including upcoming plugins in our Plugins Pipeline.Tenable Attack Surface Management customers are able to identify assets running MongoDB services by using the filter ‘Services contains mongod’ as shown in the screenshot below: Get more informationMongoDB Security AdvisoryCensys: MongoBleed – Critical MongoDB Uninitialized Memory Disclosure Vulnerability [CVE-2025-14847]Join Tenable’s Research Special Operations (RSO) Team on Tenable Connect and engage with us in the Threat Roundtable group for further discussions on the latest cyber threats.Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.
- CVE-2025-40602: SonicWall Secure Mobile Access (SMA) 1000 Zero-Day Exploitedby Scott Caveza on December 17, 2025 at 3:27 pm
A zero-day vulnerability in SonicWall’s Secure Mobile Access (SMA) 1000 was reportedly exploited in the wild in a chained attack with CVE-2025-23006.Key takeaways:CVE-2025-40602 is a local privilege escalation vulnerability in the appliance management console (AMC) of the SonicWall SMA 1000 appliance. CVE-2025-40602 has been exploited in a chained attack with CVE-2025-23006, a deserialization of untrusted data vulnerability patched in January. A list of Tenable plugins for this vulnerability can be found on the individual CVE pages for CVE-2025-40602 and CVE-2025-23006.BackgroundOn December 17, SonicWall published a security advisory (SNWLID-2025-0019) for a newly disclosed vulnerability in its Secure Mobile Access (SMA) 1000 product, a remote access solution.CVEDescriptionCVSSv3CVE-2025-40602SonicWall SMA 1000 Privilege Escalation Vulnerability6.6AnalysisCVE-2025-40602 is a local privilege escalation vulnerability in the appliance management console (AMC) of the SonicWall SMA 1000 appliance. An authenticated, remote attacker could exploit this vulnerability to escalate privileges on an affected device. While on its own, this flaw would require authentication in order to exploit, the advisory from SonicWall states that CVE-2025-40602 has been exploited in a chained attack with CVE-2025-23006, a deserialization of untrusted data vulnerability patched in January. The combination of these two vulnerabilities would allow an unauthenticated attacker to execute arbitrary code with root privileges.According to SonicWall, “SonicWall Firewall products are not affected by this vulnerability.”Historical exploitation of SonicWall vulnerabilitiesSonicWall products have been a frequent target for attackers over the years. Specifically, the SMA product line has been targeted in the past by ransomware groups, as well as being featured in the Top Routinely Exploited Vulnerabilities list co-authored by multiple United States and International Agencies.Earlier this year, an increase in ransomware activity tied to SonicWall Gen 7 Firewalls was observed. While initially it was believed that a new zero-day may have been the root cause, SonicWall later provided a statement noting that exploitation activity was in relation to CVE-2024-40766, an improper access control vulnerability which had been observed to have been exploited in the wild. More information on this can be found on our blog.Given the past exploitation of SonicWall devices, we put together the following list of known SMA vulnerabilities that have been exploited in the wild:CVEDescriptionTenable Blog LinksYearCVE-2019-7481SonicWall SMA100 SQL Injection Vulnerability12019CVE-2019-7483SonicWall SMA100 Directory Traversal Vulnerability-2019CVE-2021-20016SonicWall SSLVPN SMA100 SQL Injection Vulnerability1, 2, 3, 4, 52021CVE-2021-20038SonicWall SMA100 Stack-based Buffer Overflow Vulnerability1, 2, 32021CVE-2025-23006SonicWall SMA 1000 Deserialization of Untrusted Data Vulnerability12025CVE-2024-40766SonicWall SonicOS Improper Access Control Vulnerability12025Proof of conceptAt the time this blog was published, no proof-of-concept (PoC) code had been published for CVE-2025-40602. If and when a public PoC exploit becomes available for CVE-2025-40602, we anticipate a variety of attackers will attempt to leverage this flaw as part of their attacks.SolutionSonicWall has released patches to address this vulnerability as outlined in the table below:Affected VersionFixed Version12.4.3-03093 and earlier12.4.3-0324512.5.0-02002 and earlier12.5.0-02283The advisory also provides a workaround to reduce potential impact. This involves restricting access to the AMC to trusted sources. We recommend reviewing the advisory for the most up to date information on patches and workaround steps.Identifying affected systemsA list of Tenable plugins for this vulnerability can be found on the individual CVE page for CVE-2025-40602 as they’re released. This link will display all available plugins for this vulnerability, including upcoming plugins in our Plugins Pipeline. In addition, product coverage for CVE-2025-23006 can be found here.Tenable Attack Surface Management customers are able to identify these assets using a filtered search for SonicWall devices: Get more informationSonicWall SNWLID-2025-0019 Security AdvisoryTenable Blog: CVE-2025-23006: SonicWall Secure Mobile Access (SMA) 1000 Zero-Day Reportedly ExploitedJoin Tenable’s Research Special Operations (RSO) Team on Tenable Connect and engage with us in the Threat Roundtable group for further discussions on the latest cyber threats.Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.
- Microsoft Patch Tuesday 2025 Year in Reviewby Research Special Operations on December 10, 2025 at 3:49 pm
Microsoft addressed over 1,100 CVEs as part of Patch Tuesday releases in 2025, including 40 zero-day vulnerabilities.Key takeaways:Microsoft’s 2025 Patch Tuesday releases addressed 1,130 CVEs. This is the second year in a row where the CVE count was over 1,000. Elevation of Privilege vulnerabilities accounted for 38.3% of all Patch Tuesday vulnerabilities in 2025, followed by Remote Code Execution flaws at 30.8%. 41 zero-day vulnerabilities were addressed across all Patch Tuesday releases in 2025, including 24 that were exploited in the wild.BackgroundMicrosoft’s Patch Tuesday, a monthly release of software patches for Microsoft products, has just celebrated its 22nd anniversary. The Tenable Research Special Operations Team (RSO) first covered the 20th anniversary in 2023, followed by our 2024 year in review publication, covering the trends and significant vulnerabilities from the 2024 Patch Tuesday releases.AnalysisIn 2025, Microsoft patched 1,130 CVEs throughout the year across a number of products. This was a 12% increase compared to 2024, when Microsoft patched 1,009 CVEs. With another year of Patch Tuesday releases behind us, Microsoft has yet to break its 2020 record with 1,245 CVE’s patched. However, this is the second year in a row that Microsoft crossed the 1,000 CVE threshold, and the third time since Patch Tuesday’s inception.In 2025, Microsoft broke its record for the most CVEs patched in a month twice. The year started off with the largest Patch Tuesday release with 157 CVEs patched. This record was broken again in October with 167 CVEs patched.Patch Tuesday 2025 by severityEach month, Microsoft categorizes vulnerabilities into four main severity levels: low, moderate, important and critical.Over the last three years, the bulk of the Patch Tuesday vulnerabilities continue to be rated as important. In 2025, 91.3% of all CVEs patched were rated important, followed by critical at 8.1%. Moderate accounted for 0.4%, while there were no CVEs rated as low in 2025.Patch Tuesday 2025 by impactIn addition to severity levels, Microsoft also categorizes vulnerabilities by seven impact levels: remote code execution (RCE), elevation of privilege (EoP), denial of service (DoS), information disclosure, spoofing, security feature bypass and tampering.In 2024, RCE vulnerabilities led the impact category, however 2025 saw EoP vulnerabilities taking the lead with 38.3% of all Patch Tuesday vulnerabilities. RCE accounted for 30.8%, followed by information disclosure flaws at 14.2% and DoS vulnerabilities at 7.7%. In a strange coincidence, this year there were only 4 CVEs categorized as tampering, which was the same in 2024. In both 2024 and 2025, tampering flaws accounted for only 0.4%.Patch Tuesday 2025 zero-day vulnerabilitiesIn 2025, Microsoft patched 41 CVEs that were identified as zero-day vulnerabilities. Of the 41 CVEs, 24 were exploited in the wild. While not all zero-days were exploited, we classify zero-days as those vulnerabilities that were disclosed prior to being patched by the vendor.Looking deeper at the 24 CVEs that were exploited in the wild, 62.5% were EoP flaws. EoP vulnerabilities are often leveraged by advanced persistent threat (APT) actors and determined cybercriminals seeking to elevate privileges as part of post-compromise activity. Following EoP flaws, RCEs were the second most prominent vulnerabilities across Patch Tuesday, accounting for 20.8% of zero-day flaws.While only a small number of zero-days were addressed as part of 2025’s Patch Tuesday releases, we took a deeper dive into some of the more notable zero-days from the year. The table below includes these CVEs along with details on their exploitation activity.CVEDescriptionExploitation ActivityCVE-2025-24983Windows Win32 Kernel Subsystem Elevation of Privilege VulnerabilityUsed with the PipeMagic backdoor to spread ransomware.CVE-2025-29824Windows Common Log File System Driver Elevation of Privilege VulnerabilityExploited by Storm-2460, also known as RansomEXX. Abused by the PipeMagic backdoor in order to spread ransomware.CVE-2025-26633Microsoft Management Console Security Feature Bypass VulnerabilityExploited by Water Gamayu (aka EncryptHub, Larva-208) to deploy the MSC EvilTwin trojan loader. The attack campaigns also saw several malware variants abused, including EncryptHub stealer, DarkWisp backdoor, SilentPrism backdoor, Stealc and the Rhadamanthys stealer.CVE-2025-33053Internet Shortcut Files Remote Code Execution VulnerabilityExploited by the APT known as Stealth Falcon (aka FruityArmor, G0038) to deploy Horus Agent malware.CVE-2025-49704Microsoft SharePoint Remote Code Execution VulnerabilityExploited by multiple APTs and nation-state actors including Linen Typhoon (aka Emissary Panda), Violet Typhoon, Storm-2603 and Warlock ransomware (aka GOLD SALEM). Chained with CVE-2025-49706 in an attack dubbed ToolShell.CVE-2025-49706Microsoft SharePoint Server Spoofing VulnerabilityExploited by multiple APTs and nation-state actors including Linen Typhoon (aka Emissary Panda), Violet Typhoon, Storm-2603 and Warlock ransomware (aka GOLD SALEM). Chained with CVE-2025-49704 in an attack dubbed ToolShell.ConclusionWith 2025’s Patch Tuesday releases in our rear-view mirror, it’s evident that we continue to see an upward trend in the number of vulnerabilities addressed year over year by Microsoft. With the lion’s share of the market for operating systems, it’s imperative that defenders are quick to apply patches on the monthly release of Patch Tuesday updates. Attackers are often opportunistic and ready to capitalize on the latest exploitable vulnerabilities. As always, the RSO team will continue our monthly cadence of Patch Tuesday blogs, ensuring our readers have the actionable information necessary to take immediate action and improve their organization’s security posture.Get more informationTenable Blog: Microsoft Patch Tuesday 2024 Year in ReviewTenable Blog: Microsoft Patch Tuesday 2023 Year in ReviewJoin Tenable’s Research Special Operations (RSO) Team on Tenable Connect and engage with us in the Threat Roundtable group for further discussions on the latest cyber threats.Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.