Dark Web News – The Cyber Express Trending Cybersecurity News, Updates, Magazine and More.
- Dark Web Article Contest Offers $10,000 for Exploit Writing on TierOne Forumby Ashish Khaitan on April 14, 2026 at 5:55 am
In an unusual development within the underground cyber world, a dark web article contest has been announced on a well-known dark web forum, TierOne forum. The initiative is backed by a $10,000 prize pool. The contest places a spotlight on technical writing centered around vulnerability exploitation, offering insight into how knowledge is shared and rewarded in these spaces. Traditionally, dark web forums have been linked to illicit activities such as trading stolen data, coordinating ransomware attacks, and distributing malware. However, this contest introduces a different dynamic, one that mirrors legitimate cybersecurity ecosystems, where researchers document findings and share exploit techniques. The Dark Web Article Contest Overview and Prize Structure According to an official announcement shared by an administrator on the forum, the post states: “Всем привет! Мы рады сообщить T1 erone [КОНКУРС СТАТЕЙ #1 – 2026]. Победители конкурса получают призы: 1 место 5.000$, 2 место – 3.000$, 3 место – 2.000$, [Призовой фонд 10.000$]. Прием статей начинается 13.04.2026 и заканчивается 14.05.2026.” The announcement indicates that the dark web article contest will run from April 13, 2026, to May 14, 2026, with prize amounts set at $5,000 for first place, $3,000 for second place, and $2,000 for third place, making up a total prize pool of $10,000, reportedly sponsored by the ransomware group cry0. Topics Focused on Vulnerability Exploitation The contest invites submissions covering a wide range of advanced topics related to vulnerability exploitation with real-world applicability. These include: Remote Code Execution (RCE) through deserialization flaws in React and Node.js frameworks. Command injection attacks in APIs and backend systems. Insecure Direct Object Reference (IDOR) vulnerabilities in SaaS platforms. Server-Side Template Injection (SSTI) in modern templating engines. Exploitation of insecure deserialization in PHP and Java. Client-side RCE via Markdown or Office file rendering. Firmware attacks targeting routers and cameras. Privilege escalation techniques in RouterOS and similar systems. Exploitation methods for products from Cisco, MikroTik, Oracle, and Ubiquiti. Zero-day discovery in browser components like WebGPU and Blink. AI-assisted vulnerability discovery and reverse engineering. Techniques for bypassing AV and EDR security systems. Exploitation of Remote Procedure Call (RPC) mechanisms. For context, vulnerabilities such as RCE, IDOR, and SSTI allow attackers to execute arbitrary code or access restricted data, while firmware attacks enable persistent control over hardware devices. Similarly, AV/EDR bypass techniques are designed to evade detection by modern security solutions. Participation Rules and Requirements The TierOne forum has outlined strict guidelines for participants. Articles must be published within the forum’s designated section and include a specific prefix to qualify: Submissions must be posted under the Articles section with the prefix “[Contest]”. A link to the article must be shared in the contest thread with a participation note. All users are eligible, regardless of registration date or activity level. The use of multiple accounts is strictly prohibited. In addition, the contest enforces content quality standards: Articles must be original and based on the author’s own experience. Copy-pasted or reposted material is not allowed. Submissions should comprehensively cover the chosen topic, including tools, techniques, and methodologies. Minimum length requirement is at least one A4 page. Excessive filler content is discouraged. Including video demonstrations may improve chances of winning. A Glimpse into Dark Web Knowledge Sharing While the existence of such a contest may seem surprising, it notes a bigger trend within dark web forums. Beyond illegal marketplaces and data trading, these platforms also function as hubs for technical exchange, where members document and refine vulnerability exploitation techniques. In many ways, the structure resembles legitimate bug bounty programs and penetration testing workflows, where cybersecurity professionals publish detailed reports on discovered flaws. The key difference lies in the intent and environment in which this knowledge is applied. It is important to note that this article does not endorse participation in such activities. Instead, it aims to shed light on how these underground ecosystems operate. The TierOne forum contest highlights that even within the dark web, there are organized efforts to produce structured, experience-based technical content, albeit in a context that raises ethical and legal concerns.
- Russian Hackers Exploit SOHO Routers for DNS Hijacking Campaignby Ashish Khaitan on April 9, 2026 at 11:55 am
The rise of SOHO router compromise campaigns has exposed a critical weakness in global network security, particularly as threat actors like Forest Blizzard continue to exploit poorly secured home and small-office devices. According to security researchers, this Russia-linked group has been systematically targeting vulnerable routers since at least August 2025, transforming them into covert infrastructure for surveillance and follow-on cyberattacks. Forest Blizzard and the Expanding SOHO Router Compromise Campaign Forest Blizzard, a threat actor associated with Russian military intelligence and tracked in part as Storm-2754, has conducted widespread exploitation of SOHO devices. By leveraging the SOHO router compromise, the group has successfully hijacked Domain Name System (DNS) requests, allowing it to passively monitor and collect network traffic at scale. Microsoft identified more than 200 organizations and over 5,000 consumer devices impacted by this malicious DNS infrastructure. Notably, telemetry showed no compromise of Microsoft-owned systems. However, the breadth of affected networks highlights the campaign’s reach and the effectiveness of targeting edge devices that often lack strong monitoring or security controls. For actors like Forest Blizzard, DNS hijacking provides persistent and low-visibility access to sensitive data flows. By positioning themselves upstream of enterprise environments, attackers can observe and potentially manipulate traffic without directly breaching corporate systems. How SOHO Router Compromise Leads to DNS Hijacking After gaining access to vulnerable routers, Forest Blizzard alters their default configurations to use attacker-controlled DNS resolvers. This manipulation causes connected devices to unknowingly send DNS queries to malicious servers. Most endpoint devices rely on routers for network configuration via the Dynamic Host Configuration Protocol (DHCP). Once a router is compromised, all connected devices inherit the malicious DNS settings. This makes the SOHO router a compromise, an efficient and scalable attack vector. The group is believed to use the legitimate dnsmasq utility to handle DNS queries. While dnsmasq is commonly used in home networking for DNS forwarding and DHCP services, in this context, it enables attackers to intercept, log, and respond to DNS requests while maintaining the appearance of normal operations. Forest Blizzard’s Use of Adversary-in-the-Middle Attacks Beyond passive surveillance, Forest Blizzard has extended its SOHO router compromise operations to support adversary-in-the-middle (AiTM) attacks. These attacks specifically target Transport Layer Security (TLS) connections, enabling interception of sensitive communications. In most cases, DNS traffic is transparently proxied, allowing users to connect to legitimate services without disruption. However, in select high-value scenarios, the attackers spoof DNS responses for targeted domains. This redirects victims to malicious infrastructure controlled by Forest Blizzard. Once redirected, victims may encounter invalid TLS certificates mimicking legitimate services such as Outlook on the web. If users ignore certificate warnings, attackers can intercept plaintext data within the encrypted session. This may include emails and other sensitive cloud-hosted content. Researchers observed two notable AiTM scenarios: Attacks on Microsoft 365 domains, particularly Outlook on the web. Targeted operations against government servers in at least three African countries, where DNS interception enabled further data collection. Mitigation Strategies Against Forest Blizzard Threats To counter risks associated with SOHO router compromise, researchers recommend several defensive measures. For DNS protection, organizations should enforce domain-based access controls using Zero Trust DNS (ZTDNS), block malicious domains, and maintain detailed DNS logs to detect anomalies. Enabling network and web protection features in Microsoft Defender for Endpoint further strengthens defenses. Equally critical is addressing identity security. Centralizing identity management, enforcing multifactor authentication (MFA), and applying Conditional Access policies can reduce the impact of credential theft from AiTM attacks. It is also advised to adopt passwordless solutions such as passkeys and restrict authentication to trusted devices and locations.
- Eurail Confirms Security Breach Affecting Over 300,000 U.S. Individualsby Samiksha Jain on April 9, 2026 at 5:44 am
The Eurail data breach has exposed personal information of approximately 308,777 individuals in the United States, according to a disclosure by Eurail B.V., the Netherlands-based company that manages the official online sales platform for Eurail and Interrail rail passes. Among those affected are 242 residents of New Hampshire. The Eurail data breach occurred between late December 2025 and early January 2026, when an unauthorized actor gained access to Eurail’s network and transferred files. The company identified the issue after detecting unusual activity within its systems and later confirmed the exposure of personal data. Eurail Data Breach Timeline and Response Following the detection of suspicious activity, Eurail activated its incident response procedures and initiated an investigation with third-party cybersecurity experts. Law enforcement was also notified and is continuing to investigate the incident. According to the company, the unauthorized access took place on December 26, 2025, when files were transferred from its network. The investigation concluded that these files contained personal information, with the final determination made on February 25, 2026. Eurail began notifying affected individuals and state authorities on March 27, 2026, reporting the breach to attorneys general in California, New Hampshire, Oregon, and Vermont. A public notice was also issued on the European Youth Portal. Information Compromised in the Eurail Data Breach The company confirmed that the Eurail data breach involved sensitive personal information, including: Names Passport numbers While this represents the confirmed data for U.S. individuals, earlier findings suggest that the broader impact may be more extensive. Previous disclosures linked to the incident indicated that additional data types were compromised, including financial and health-related information. Broader Exposure Linked to Eurail Data Breach Earlier this year, Eurail confirmed that data from a prior breach was being offered for sale on the dark web, with samples appearing on Telegram. This development suggested that the incident extended beyond initial containment and had evolved into a wider data exposure situation. The earlier dataset reportedly included passport details, bank account IBANs, email addresses, phone numbers, and health information, in addition to names. The combination of such data increases the risk of identity theft, financial fraud, and long-term misuse. The breach is also believed to have affected customers who purchased Eurail or Interrail passes through partner channels, as well as participants in the DiscoverEU program, which issued its own warning that sensitive personal details, including passport copies and financial information, may have been exposed. Company Measures and Security Actions In response to the Eurail data breach, the company has taken several steps, including terminating unauthorized access, strengthening internal security measures, and continuing its cooperation with law enforcement and cybersecurity experts. Eurail stated that it takes the protection of customer information seriously and is working to prevent similar incidents in the future. The investigation into the full scope of the breach is ongoing. What Affected Individuals Should Do Eurail has advised customers to stay alert to suspicious communications, especially any requests for personal information. Individuals are encouraged not to share sensitive data with unknown or unsolicited contacts claiming to represent the company. The company also recommends that users monitor their financial accounts and review credit reports regularly for any unauthorized activity. In the United States, consumers can obtain a free annual credit report from each of the three major credit bureaus. Those who suspect misuse of their information are advised to contact the Federal Trade Commission, reach out to their state’s attorney general office, and report the matter to local law enforcement. A Growing Risk Around Travel Data The Eurail data breach highlights the risks associated with large-scale travel platforms that handle sensitive identity and financial information. With passport numbers and other personal identifiers involved, the exposure can lead to long-term consequences for affected individuals. As investigations continue, the incident reinforces the need for stronger data protection measures and constant monitoring across systems that manage sensitive traveler information.
- FBI Takes Down APT28 Network Behind Global DNS Hijacking Attacksby Ashish Khaitan on April 8, 2026 at 7:00 am
The Russian-linked threat group APT28 has continued to leverage vulnerable network devices to carry out large-scale DNS hijacking campaigns, enabling adversary-in-the-middle attacks. Recent developments show that these operations have drawn direct intervention from U.S. authorities. The U.S. Department of Justice and the FBI announced a court-authorized operation to disrupt a network of compromised routers controlled by Russia’s military intelligence unit, widely known as APT28. According to findings aligned with prior reporting from the NCSC, the group has been exploiting routers to intercept communications, harvest credentials, and target individuals and organizations of intelligence interest. DNS Hijacking and Adversary-in-the-Middle Tactics APT28’s operations include DNS hijacking, a technique that manipulates how domain names are resolved into IP addresses. By altering DNS settings, often at the router level, attackers redirect legitimate traffic through malicious infrastructure. This enables adversary-in-the-middle (AitM) attacks, where victims unknowingly connect to spoofed services. These malicious endpoints are designed to imitate legitimate platforms, allowing attackers to intercept login sessions and extract sensitive data, including passwords, OAuth tokens, and emails. Both the FBI and the NCSC have noted that these attacks can impact browser sessions and desktop applications alike, increasing the scale and effectiveness of credential harvesting. U.S. Operation Targets APT28 Infrastructure The disruption effort, publicly disclosed by the Department of Justice, targeted a network of small office/home office (SOHO) routers compromised by APT28, also known as Fancy Bear, Sofacy, Sednit, STRONTIUM, Forest Blizzard, and Pawn Storm. The group is widely attributed to Russia’s GRU Unit 26165. Since at least 2024, APT28 actors have exploited known vulnerabilities to gain access to thousands of TP-Link routers globally. After stealing credentials, they modified router configurations to redirect DNS traffic to malicious servers under their control. These operations were initially indiscriminate. However, the attackers implemented automated filtering mechanisms to identify DNS queries of intelligence value. For selected targets, the malicious DNS resolvers returned fraudulent records for domains, particularly those mimicking Microsoft Outlook services, to facilitate adversary-in-the-middle attacks against encrypted traffic. Through this approach, APT28 was able to harvest unencrypted passwords, authentication tokens, emails, and other sensitive data from devices connected to compromised routers. Official Statements on the Threat U.S. officials described the campaign as both persistent and dangerous. Assistant Attorney General John A. Eisenberg stated, “The GRU’s predatory use of networks in American homes and businesses for its malicious cyber operations remains a serious and persistent threat.” U.S. Attorney David Metcalf added, “Russian military intelligence once again hijacked Americans’ hardware to commandeer critical data,” emphasizing that the government would continue to respond aggressively to nation-state cyber threats. FBI officials also stressed the scale of the campaign. Assistant Director Brett Leatherman noted that compromised routers were used globally for espionage, while Special Agent Ted E. Docks highlighted that devices across more than 23 U.S. states had been weaponized. How the FBI Disrupted the DNS Hijacking Network As part of the court-authorized operation, referred to as Operation Masquerade, the FBI deployed technical measures to neutralize the U.S. portion of APT28’s infrastructure. According to court documents: The FBI sent commands to compromised routers to collect evidence of APT28 activity. Reset DNS settings, removing malicious resolvers and restoring legitimate ISP configurations. Blocked the actors’ ability to regain unauthorized access. The operation was carefully tested on affected TP-Link devices to ensure that it did not disrupt normal functionality or collect user content. Importantly, the remediation steps can be reversed by users through factory resets or manual configuration changes. Continued Router Exploitation and Infrastructure Tactics These developments align closely with earlier findings from the NCSC, which documented how APT28 used Virtual Private Servers (VPSs) as malicious DNS infrastructure. Two main clusters were identified: Cluster One: Focused on modifying DHCP DNS settings in SOHO routers, enabling selective DNS hijacking and adversary-in-the-middle attacks. Cluster Two: Involved forwarding DNS traffic through a layered infrastructure, with some operations targeting high-value devices, including those in Ukraine. APT28’s activity has also included exploitation of vulnerabilities such as CVE-2023-50224 in TP-Link routers, allowing attackers to extract credentials and reconfigure DNS settings via crafted HTTP requests. Targeted Services and Indicators APT28’s DNS hijacking campaigns have frequently targeted Microsoft Outlook-related domains, including: autodiscover-s.outlook[.]com imap-mail.outlook[.]com outlook.live[.]com outlook.office[.]com outlook.office365[.]com These targets reflect a clear focus on email-based intelligence gathering. Supporting infrastructure includes numerous malicious IP ranges and identifiable server configurations, such as unusual SSH ports and “dnsmasq-2.85” DNS services. Mitigation and Security Recommendations Both the FBI and the NCSC recommend immediate steps to mitigate risks associated with DNS hijacking and adversary-in-the-middle attacks: Replace end-of-life or unsupported routers Update firmware to the latest available versions Verify DNS settings to ensure they point to legitimate resolvers Disable or secure remote management interfaces Implement firewall rules to limit exposure Enable multi-factor authentication (MFA) to reduce credential abuse Users are also encouraged to monitor their networks and report suspected compromises to appropriate authorities.
- $20 Billion Lost to Cybercrime as AI and Investment Scams Surge: FBI Reportby Samiksha Jain on April 7, 2026 at 5:37 am
The FBI Internet Crime Report 2025 shows just how expensive cybercrime has become. In 2025, the FBI’s Internet Crime Complaint Center (IC3) received over one million complaints, with reported losses touching $20.8 billion, the highest ever recorded. That figure is not just a statistic. It reflects everyday incidents, individuals losing life savings to investment scams, businesses wiring money to fraudulent accounts, and organizations dealing with disruptions from ransomware attacks. What used to be isolated cases are now happening at scale. The FBI Internet Crime Report 2025 also shows how the nature of cybercrime is changing. Fraud is no longer limited to suspicious emails or obvious scams. Criminals are using social platforms, messaging apps, and now even artificial intelligence to make their operations look legitimate. In many cases, victims don’t realize they are being targeted until the money is already gone. At the same time, the report highlights that law enforcement is trying to keep pace. Operations targeting crypto scams and international fraud networks are making an impact, but the overall trend shows that cybercrime is expanding faster than it is being contained. Cyber-Enabled Fraud Remains the Biggest Driver A large share of these losses comes from cyber-enabled fraud, which alone accounts for nearly 85% of the total financial damage, or about $17.7 billion. Investment fraud continues to cause the most damage. In 2025, it led to $8.6 billion in losses, followed by business email compromise (BEC) and tech support scams. Within this, cryptocurrency investment fraud stands out. Losses linked to crypto scams reached $7.2 billion, making it the biggest single category. Image Source: FBI Report These scams are no longer basic phishing attempts. Attackers spend time building trust, approaching victims through social media, messaging apps, or even dating platforms. Once trust is established, victims are guided toward fake investment platforms that show fabricated profits. By the time withdrawals are attempted, the money is gone. AI-Enabled Scams Are Growing Fast The FBI Internet Crime Report 2025 includes a separate section on AI-enabled scams for the first time, and the early numbers are already concerning. More than 22,000 complaints linked to AI Around $893 million in losses AI is making scams more convincing. Fake profiles, cloned voices, and realistic conversations can now be created quickly and at scale. This allows attackers to run highly targeted campaigns without much effort. The challenge is that these scams often look legitimate, making it harder for individuals and even businesses to identify red flags in time. Ransomware Continues to Target Critical Sectors Ransomware remains a steady threat, especially for critical infrastructure. Over 3,600 complaints reported in 2025 Losses crossed $32 million The actual impact is likely much higher. Many organizations do not report full losses, especially indirect costs like downtime or recovery expenses. The report also notes 63 new ransomware variants identified during the year, showing how quickly these attacks continue to evolve. Sectors such as healthcare, manufacturing, and government facilities remain frequent targets, where even short disruptions can have serious consequences. FBI Operations Are Preventing Some Losses The report also highlights efforts by law enforcement to limit the damage. One example is Operation Level Up, focused on cryptocurrency investment scams. Since its launch in 2024, the initiative has helped reduce potential losses by more than $500 million. In many cases, victims did not realize they were being scammed until they were contacted. This reflects a larger issue, many cyber fraud cases go unnoticed until significant financial damage has already occurred. Cybercrime Is Becoming More Structured The report also points to broader trends. Cybercriminal groups are operating more like organized businesses. At the same time, state-linked actors are becoming more active, targeting infrastructure and sensitive data. One example highlighted is the DPRK IT worker scam, where individuals posing as remote IT workers gain access to company systems and use that access for data theft or further attacks. These developments show that cybercrime is no longer limited to isolated incidents. It is part of a larger, global ecosystem. A Growing Gap Between Threats and Preparedness The FBI Internet Crime Report 2025 shows a clear pattern—cybercrime is scaling faster than awareness and response. Fraud tactics are becoming more personal and long-term AI is helping attackers improve success rates Cryptocurrency is making transactions harder to trace While recovery efforts and law enforcement actions are improving, most interventions still happen after the damage is done. Final Take on FBI Internet Crime Report 2025 The FBI Internet Crime Report 2025 highlights a shift in how cybercrime operates today. The scale—over $20 billion in losses—is significant, but the methods behind these numbers are just as important. From cyber-enabled fraud to AI-enabled scams and cryptocurrency investment fraud, attackers are using a mix of technology and human psychology to succeed. For individuals and organizations, the risk is no longer occasional—it is constant, and it is evolving.
- A Compromised Tool Opened the Door to a 91GB European Commission Data Leakby Samiksha Jain on April 6, 2026 at 8:27 am
The European Commission cloud breach did not begin with a dramatic system hack or a visible outage. It started quietly, with a trusted tool, a routine update, and a single compromised credential. Within days, that was enough to expose nearly 91.7 GB of data and drag multiple EU entities into a widening cybersecurity incident. Disclosed publicly on March 27, the European Commission cloud breach is now being treated as a clear example of how supply-chain attacks are reshaping risk in cloud environments. Not because defenses were absent, but because the entry point looked legitimate. European Commission Cloud Breach Traced to Compromised Trivy Tool Investigators from CERT-EU say, with high confidence, that the European Commission cloud breach began with a supply-chain compromise involving Trivy, a widely used security scanning tool. The malicious version, attributed to a threat actor known as TeamPCP, was unknowingly used within the Commission’s environment after being delivered through standard update channels. On March 19, the attacker obtained an AWS secret, an API key—with management-level permissions. That single key became the gateway into the Commission’s cloud infrastructure. From there, the activity was deliberate. The attacker attempted to uncover more credentials using TruffleHog, a tool designed to scan for secrets and validate access through AWS Security Token Service (STS). They also created a new access key tied to an existing user, an attempt to maintain access while avoiding detection. The European Commission cloud breach did not rely on breaking in. It relied on blending in. Data Theft and Dark Web Leak The impact became clearer days later. A large volume of data, around 91.7 GB compressed, or roughly 340 GB uncompressed—was exfiltrated from the compromised AWS account. On March 28, the data extortion group ShinyHunters published the dataset on its dark web leak site. The group claimed it included “data dumps of mail servers, datavases [sic], confidential documents, contracts, and much more sensitive material”. Early analysis confirms that the European Commission cloud breach exposed personal data, including names, usernames, and email addresses. The dataset also contains more than 51,000 files linked to outbound email communications. While most of these emails are automated notifications, some “bounce-back” messages may include original user-submitted content. That detail matters, as it raises the risk of unintended personal data exposure across systems that rely on user interaction. Wider Impact Across EU Entities The European Commission cloud breach goes beyond a single institution. The compromised AWS account is part of the infrastructure behind the “europa.eu” web hosting platform, which supports dozens of websites. Data linked to up to 71 clients may be affected, 42 internal European Commission services and at least 29 other Union entities. This shared infrastructure model is efficient, but it also means that one compromised component can have a broader footprint. Despite this, officials have confirmed that no websites were defaced, taken offline, or altered during the incident. There were no service disruptions. But the absence of visible damage should not be mistaken for limited impact. Timeline Shows Speed of Supply-Chain Attacks The timeline of the European Commission cloud breach highlights how quickly such incidents can unfold: March 19: AWS credential obtained via compromised Trivy tool March 24: Alerts triggered over unusual API activity and traffic spikes March 25: CERT-EU notified; access secured and keys revoked March 27: Public disclosure by the European Commission March 28: Data published by ShinyHunters In less than ten days, the attack moved from initial access to public data exposure. Response and Containment Efforts The European Commission acted quickly once the breach was identified. The compromised AWS secret was secured, newly created access keys were disabled, and all known exposed credentials were deactivated or deleted. Authorities also followed regulatory protocol, informing data protection bodies, including the European Data Protection Supervisor (EDPS), and notifying impacted entities. Direct communication with affected clients began on March 31. Importantly, the Commission has stated that its internal systems were not affected. However, the European Commission cloud breach remains under active investigation, particularly as analysis of the exposed databases continues. A Familiar Weakness, Repeating If the European Commission cloud breach feels familiar, it’s because the pattern is becoming more common. Attackers are no longer forcing their way in, they are entering through trusted software, CI/CD pipelines, and third-party tools. The compromised Trivy version was not flagged as malicious during installation. It behaved as expected—until it didn’t. This is the real shift. Security teams are being asked to defend not just their infrastructure, but every dependency connected to it. What This Breach Really Signals The European Commission cloud breach is not just about one incident or one tool. It reflects a deeper issue: the growing difficulty of verifying trust in modern software ecosystems. Cloud environments, automation pipelines, and open-source tools have made operations faster and more efficient. But they have also introduced new blind spots. The lesson here is uncomfortable but clear—security controls worked, but they worked late. Detection came after access had already been established and data had already moved. And that is where the real risk lies.
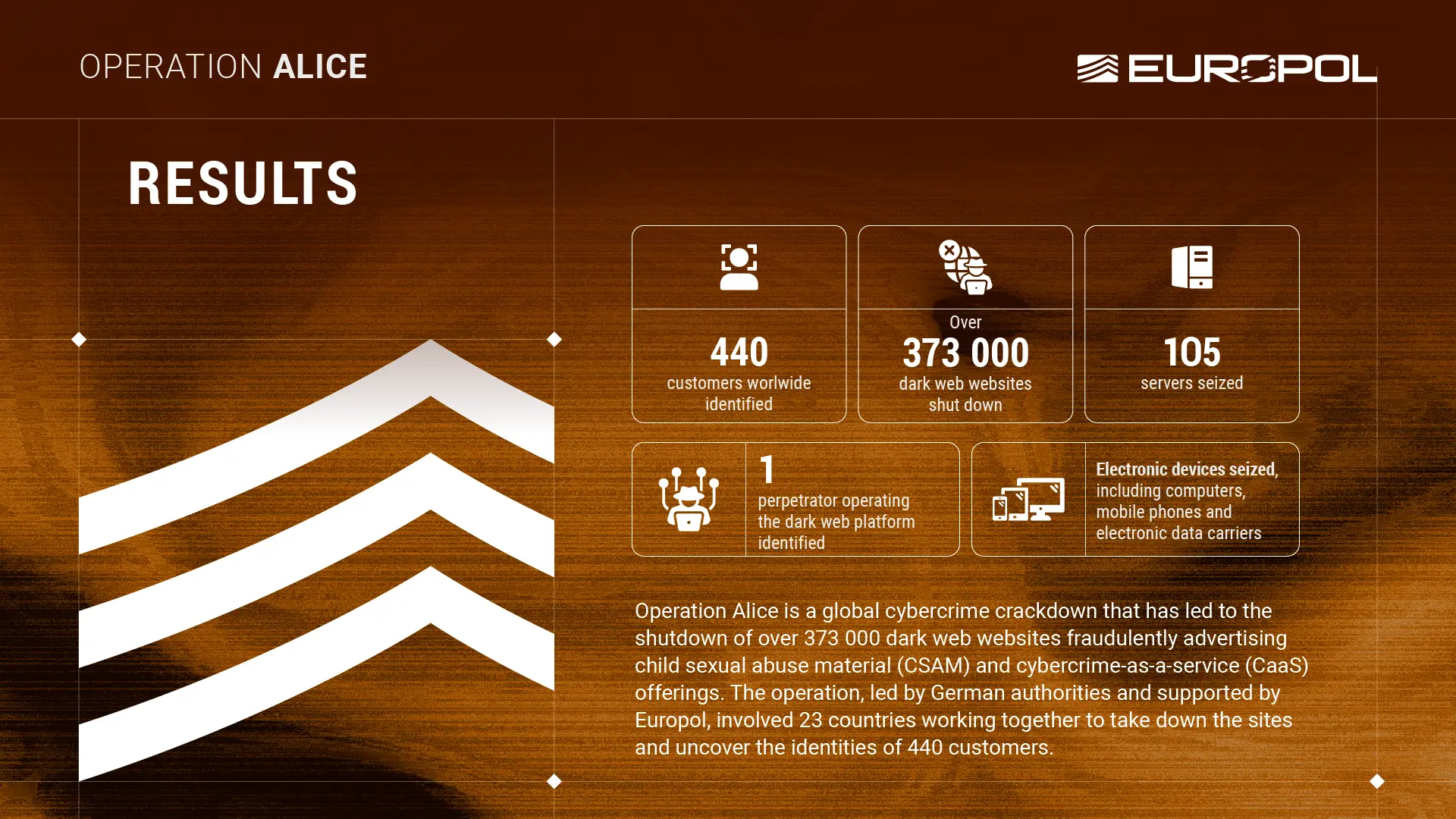
- One Operator, 373,000 Dark Web Sites, and a Criminal Business Built on Selling Nothingby Mihir Bagwe on March 23, 2026 at 9:08 am
A 35-year-old man operating from China ran the largest fraudulent dark web network ever dismantled and the most disturbing detail is not the scale of the infrastructure he built, but what he was selling — child sexual abuse material that did not exist, to thousands of buyers who paid for it anyway. On March 9, a global operation led by German authorities and supported by Europol was launched against one of the largest networks of fraudulent platforms in the dark web. The investigation began in mid-2021 against the dark web platform “Alice with Violence CP.” During the investigation, authorities discovered that the platform’s operator ran more than 373,000 fraudulent websites advertising child sexual abuse material and cybercrime-as-a-service offerings. The first phase of Operation Alice ran for 10 days, with 23 countries joining forces. The participating nations included Spain, Germany, the United States, the United Kingdom, Ukraine, Mexico, Canada, and Australia. Europol facilitated intelligence exchange, provided analytical support, coordinated the international response, and played a critical role in tracing cryptocurrency payments across jurisdictions. The criminal model this operator constructed sits at an unusual intersection of two distinct threats that security teams rarely analyze together. From February 2020 to July 2025, the suspect advertised child sexual abuse material on different platforms accessible through more than 90,000 of those onion domains. The perpetrator offered material in purchasable packages after buyers provided an email address and made a payment in Bitcoin, with each package costing between €17 and €215 and promising data volumes ranging from a few gigabytes to several terabytes. The material was never delivered. Customers were tricked into providing payment for these products but received nothing in return. Europol estimated the suspect made around €345,000 — approximately $400,000 — from around 10,000 people who attempted to buy the illicit material. Not Just Any Other Dark Web Economy The fraud architecture layered two criminal economies on top of each other. Alongside child abuse material, the platform also offered cybercrime-as-a-service listings — including stolen credit card data and access to compromised backend computer systems — extending the operator’s reach from child exploitation into enterprise-grade cybercrime services. The CaaS dimension means the operator’s customer base included not only individuals seeking abuse material but also cybercriminals seeking ready-made access to corporate networks, broadening the downstream harm considerably. The infrastructure scale alone places this case in a different category from any previous dark web takedown. The dark web runs on onion domains — a special type of website address engineered specifically to conceal the identity and location of both the operator and visitors by routing traffic through layered encryption relays. Over nearly five years of investigation, German authorities discovered that a single individual operated over 373,000 onion domains on the dark web. Managing that volume of infrastructure requires automation, deliberate operational security planning, and sustained technical capability. Operation Alice initially only targeted the platform operator. However, through international cooperation, the investigation uncovered the identities of 440 customers who had used the operator’s services. Due to the nature of the purchases, additional investigations were launched against them, and the operation remains ongoing against more than 100 of those individuals. The operational results include the seizure of 105 servers along with computers, mobile phones, and electronic storage devices. Investigators also seized the financial proceeds generated across five years of operation. Also read: FBI and Europol Dismantle LeakBase Cybercrime Forum With 142,000 Users
- The Cyber Express Weekly Roundup: Cyberattacks, AI Risks, and Geopolitical Cyber Threatsby Ashish Khaitan on March 20, 2026 at 11:44 am
In this week’s cybersecurity roundup, The Cyber Express covers key global security developments, including a major supply chain disruption affecting a global manufacturer, rising concerns over security and legal risks linked to rapid AI adoption, and the continued escalation of cyber activity driven by geopolitical tensions. Across industries, organizations are facing a mix of disruptive attacks and long-term espionage campaigns targeting both operational systems and critical infrastructure. Intelligence reports also continue to highlight sustained nation-state activity shaping the global threat landscape. These developments reflect a cybersecurity environment where operational resilience, secure technology adoption, and coordinated defense strategies are increasingly essential to managing interconnected and fast-evolving risks. The Cyber Express Weekly Roundup Stryker Cyberattack Disrupts Supply Chain, Recovery Timeline Unclear A cyberattack on Stryker Corporation has disrupted manufacturing, shipping, and order processing operations, with no clear recovery timeline announced. While internal systems were impacted, customer products have not been affected. The incident has been linked to the Handala group, and authorities, including the Cybersecurity and Infrastructure Security Agency (CISA), are currently investigating the attack. Read more… AI Legal Risks Rise as Businesses Rush Adoption, Expert Warns Cybersecurity expert Lisa Fitzgerald has warned that rapid adoption of AI tools without proper governance can expose organizations to data breaches, regulatory violations, and loss of control over sensitive information. In an interview with The Cyber Express, she emphasized the importance of structured risk assessments, employee training, and clear governance frameworks to manage AI-related risks effectively. Read more… Bonnie Butlin Highlights Role of Collaboration in Modern Security Bonnie Butlin has stressed the importance of global collaboration in addressing complex cyber, physical, and geopolitical threats. She highlighted the need to break down industry silos, strengthen cross-sector cooperation, and build more inclusive leadership models to improve resilience against evolving risks. Read more… US Intel Warns China Is Top Cyber Threat Ahead of Other Nation-States A new U.S. intelligence assessment identifies China as the most persistent cyber threat actor, with ongoing operations reportedly embedded within critical infrastructure systems. The report also highlights cyber activities from Russia, North Korea, and Iran, each employing different tactics ranging from espionage and sabotage to cybercrime and disinformation campaigns. Read more… Middle East Cyber Warfare Intensifies Amid Rising Geopolitical Conflict According to Cyble Research and Intelligence Labs, cyberattacks in the Middle East are increasing in parallel with ongoing geopolitical tensions. Critical sectors such as energy, finance, and communications have been identified as primary targets in this escalating cyber conflict landscape. Read more… Also Read: Top 50 Women Leaders in Cybersecurity to Watch in 2026 Weekly Takeaway This week’s The Cyber Express weekly roundup highlights the growing complexity of the global cybersecurity environment, from supply chain disruptions and AI governance risks to escalating nation-state cyber operations and regional cyber warfare. Organizations, governments, and individuals must remain vigilant, prioritize strong governance frameworks, and adopt proactive security measures, including timely patching and continuous monitoring, to effectively respond to the evolving threat landscape.